
I made a Fjällräven backpack from an IKEA bag! And you know I don't gatekeep-- the pattern is FREE and the most glorious sewing instructions I've ever created. You can use regular canvas, too. #ikea #Fjällräven
beckystern.com/2025/05/25/s...

I made a Fjällräven backpack from an IKEA bag! And you know I don't gatekeep-- the pattern is FREE and the most glorious sewing instructions I've ever created. You can use regular canvas, too. #ikea #Fjällräven
beckystern.com/2025/05/25/s...
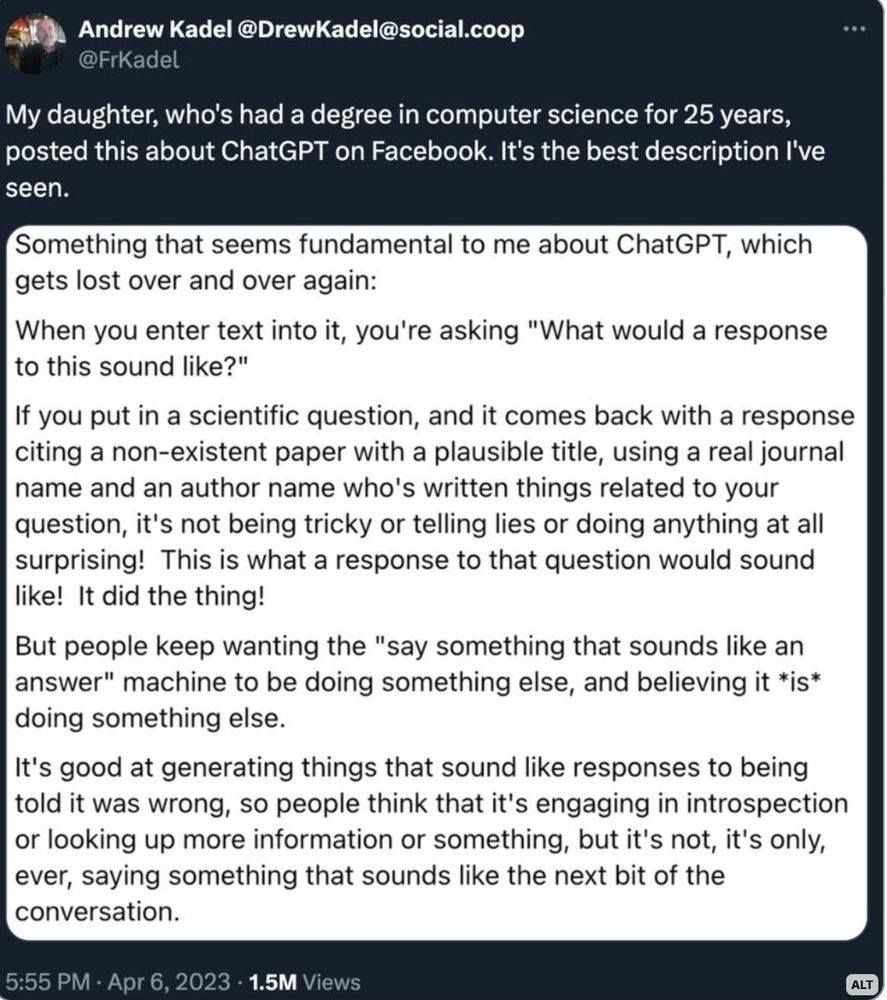
Andrew Kadel @DrewKadel@social.coop My daughter, who's had a degree in computer science for 25 years, posted this about ChatGPT on Facebook. It's the best description I've seen. Something that seems fundamental to me about ChatGPT, which gets lost over and over again: When you enter text into it, you're asking "What would a response to this sound like?" If you put in a scientific question, and it comes back with a response citing a non-existent paper with a plausible title, using a real journal name and an author name who's written things related to your question, it's not being tricky or telling lies or doing anything at all surprising! This is what a response to that question would sound like! It did the thing! But people keep wanting the "say something that sounds like an answer" machine to be doing something else, and believing it *is* doing something else. It's good at generating things that sound like responses to being told it was wrong, so people think that it's engaging in introspection or looking up more information or something, but it's not, it's only, ever, saying something that sounds like the next bit of the conversation.
The only thing ChatGPT ever does.
This is a particularly gnarly backdoor: www.nextron-systems....
Slides from my "Using PowerShell to Explore Windows" workshop at @steelcon.info 2025
files.speakerdeck.com/presentation...

I'm so excited to announce that Datadog Security Research is launching a FREE, fully-online, Detection Engineering focused conference called Datadog Detect!
bit.ly/datadog-detect
Our lineup is incredible with experts in the field of detection, response and threat intelligence.
1/
Absolutely love this resource 💙
Just came across this gem from JPCERT
👉 jpcertcc.github.io/ToolAnalysis...
It maps forensic artifacts left behind by tools used for lateral movement or credential dumping. Super detailed.

LLMs hallucinating nonexistent software packages with plausible names leads to a new malware vulnerability: "slopsquatting."

To check for existing bypass configurations, try:
Connect-ExchangeOnline
Get-MailboxAuditBypassAssociation -ResultSize Unlimited | Where-Object { $_.AuditBypassEnabled -eq $true }
To alert, try:
CloudAppEvents
| where ActionType == @"Set-MailboxAuditBypassAssociation"

A critical infra supplier in Massachusetts got a genuine call from the FBI warning of a Volt Typhoon intrusion. A manager said "Go f-yourself" after the agent tried to get him to click a link in an email. Great story by @jessicalyons.bsky.social. #infosec www.theregister.com/2025/03/12/v...

Microsoft Threat Intelligence identified a shift in tactics by Silk Typhoon, a Chinese espionage group, now targeting common IT solutions like remote management tools and cloud applications to gain initial access.
www.microsoft.com/en-us/securi...




Recorded Future's malicious infrastructure report is out
www.recordedfuture.com/research/202...
About 2 weeks after I wrote a blog post and warned about device code usage. agderinthe.cloud/2025/01/31/i...

IT Admins have you already enabled the CA policy to limit device code in your organization? If you were waiting for a reason to prioritize doing it this might help.
www.microsoft.com/en-us/securi...
#security #microsoft #entra #identity
#
Forgive your Entra ID admins, for they know not what they do. In most orgs, IAM is not owned by security. Therefore, security must inform IAM.
You MUST defend against modern cloud phishing techniques for INITIAL ACCCESS. Here are 4 of the top vectors when MFA is enforced:

A new fun way to set shadow credentials
posts.specterops.io/attacking-en...

In Part 1 of my Intune Attack Paths series, I discuss the fundamental components and mechanics of Intune that lead to the emergence of attack paths: posts.specterops.io/intune-attac...

CISA has formally brought its KEV database to GitHub, allowing easier access to the data without having to scrape the official website every few hours
github.com/cisagov/kev-...
Via Socket: socket.dev/blog/cisa-br...

🧵 How bad were ransomware attacks against healthcare in 2024? Bad.
As of right now, there were 372 *publicly reported* ransomware attacks against healthcare providers in 2024. Currently down from 2023 (377). BUT there can be a 1-2 month delay in reporting, so the final number will increase.

In case if you wonder what broke #ProcessHollowing on Windows 11 24H2, I have something for you: hshrzd.wordpress.com/2025/01/27/p...
If your company runs Exchange Online and/or Microsoft 365 have a look at CISA's latest publication: Microsoft Expanded Cloud Logs Implementation Playbook.
The report includes KQL, SPL and Powershell code to perform incident response.
www.cisa.gov/resources-to...
Using PowerShell with Microsoft Graph – Yet Another Security Blog garybushey.com/2025/...
#MicrosoftSentinel #Cybersecurity #MicrosoftSecurity #Security #DefenderXDR

I just finished editing the next episode of the "InfoSec Deep Dive" podcast. It's likely one of the best ones I've ever made!
It'll be on malware analysis. It covers everything you need to know to get started and even some advanced topics!
🔗Follow here so you don't miss it:
Sorry, mate. I've been through that a few times too. It never gets any easier. I'll take your advice and go hug my two now.
I don’t normally get worked up about the naming threat actors thing.
But the Volt & Salt Typhoon is a disaster as it’s so hard for non-specialists to tell them apart:
- Salt is Snowden style espionage by China against US
- Volt is a direct 🇨🇳 military threat to degrade western infrastructure 1/2

Black Basta Ransomware Uses MS Teams, Email Bombing to Spread Malware

Chinese hackers targeting large IT service providers in Southern Europe were seen abusing Visual Studio Code (VSCode) tunnels to maintain persistent access to compromised systems.
www-bleepingcomputer-com.cdn.ampproject.org/c/s/www.blee...
Awesome work by Lance, clear write-up on the issue, the solution, a PR to ROADtools and more tradecraft!