Little introduction for my next talk @hack_lu , this article, co-authored with @cousky_ present all details of the full exploit chain that impacted global protect : blogit.michelin.io/palo-alto-gl...
Little introduction for my next talk @hack_lu , this article, co-authored with @cousky_ present all details of the full exploit chain that impacted global protect : blogit.michelin.io/palo-alto-gl...

Michelin CERT striked back. A regression in #PaloAlto Global Protect (CVE-2025-2183) allowed to fully compromise remotely the workstation. All details will be revealed during my talk at @hack_lu. security.paloaltonetworks.com/CVE-2025-2183

Excited to be a speaker at @hack_lu! Looking forward to discussing vulnerabilities in VPN clients 🇱🇺 #hacklu #cybersecurity
🚨 Michelin Red Team starting the year with a bang! Multiple vulnerabilities discovered in VMware Aria Operations (CVE-2025-22218, 22219, 22220, 22221, 22222) 🔥 Time to patch and stay sharp!
🔗 VMware Advisory: support.broadcom.com/web/ecx/supp...
#CyberSecurity #RedTeam #VMware #CVE2025
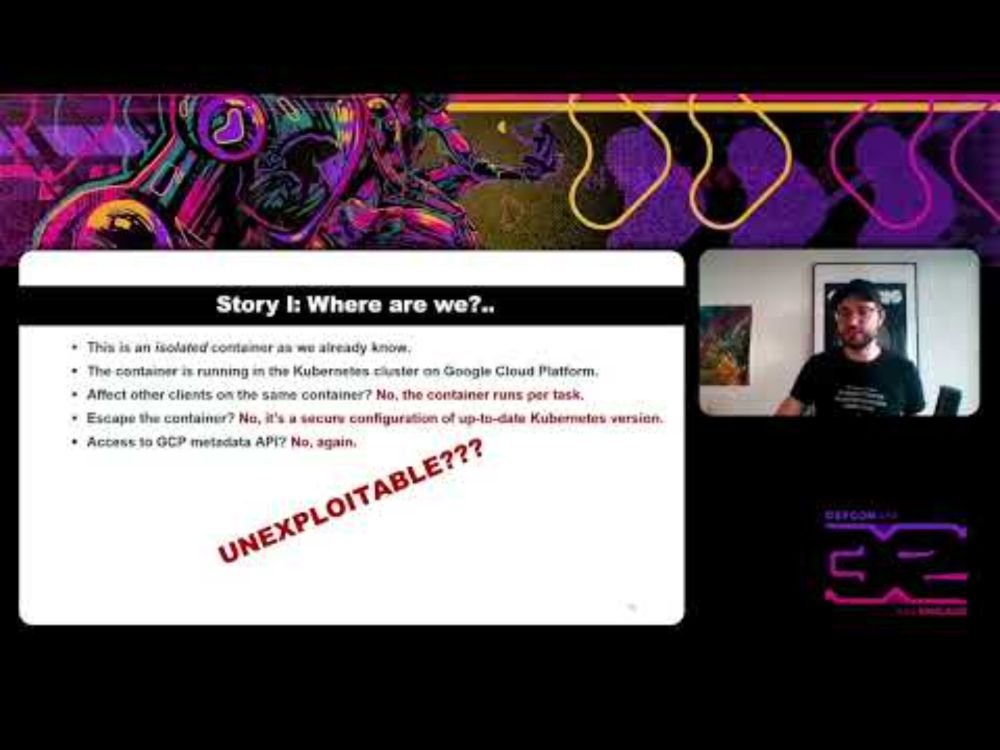
If you missed it, my #DEFCON talk "Exploiting the Unexploitable: Insights from the Kibana Bug Bounty" is now live on YouTube!
youtu.be/H-bhmSwnRdY
#Michelin CERT was also acknowledged for discovering CVE-2024-38832 and CVE-2024-38833, which affect VMware Aria Operations. Additional vulnerabilities are still undergoing the disclosure process. support.broadcom.com/web/ecx/supp... #security #bugbounty

#Michelin CERT was acknowledged for identifying CVE-2024-5921, which impacts #PaloAlto GlobalProtect. A detailed report was sent to their PSIRT team on February 26th, demonstrating how to impersonate a legitimate portal and fully compromise a workstation. #security