Books
"Threat Modeling: Designing for Security" is an excellent book by @adamshostack.bsky.social that begins with an introductory perspective and gradually builds toward more complex concepts, supported by real-world examples. Overall, a well written, enjoyable read.
kbala97.github.io/CyberTechHea...
31.01.2026 23:31
👍 1
🔁 1
💬 0
📌 0
Creates the number 1 Threat Modeling company focused on secure by design!
09.01.2026 18:35
👍 0
🔁 0
💬 0
📌 0
I had the pleasure and good fortune of collaborating with Jon on a board of a company. I have no doubt Jon will continue to influence our world!!
21.12.2025 15:02
👍 1
🔁 0
💬 0
📌 0

Massive Cloudflare outage was triggered by file that suddenly doubled in size
“I worry this is the big botnet flexing,” CEO said. But outage was self-inflicted.
Cloudflare’s outage root cause is well explained here:
Prince (CEO) explained that a feature file doubled in size. The larger-than-expected feature file was then propagated to all the machines that make up our network.”
arstechnica.com/tech-policy/...
20.11.2025 10:28
👍 0
🔁 0
💬 0
📌 0

Cyber Technology and Health
OWASP’s 2025 Wake-Up Call: Why Broken Access Control Still Haunts Web Security
November 18, 2025
OWASP’s 2025 findings show broken access control remains one of the most persistent and damaging web security problems.
kbala97.github.io/CyberTechHea...
18.11.2025 21:32
👍 1
🔁 0
💬 0
📌 0

Cyber Technology and Health
The Security Vulnerabilities to Watch For When You’re Vibe Coding:
This article discusses common security vulnerabilities developers should be aware of when “vibe coding”—coding quickly without strict adherence to best practices. @harryguinness.bsky.social
kbala97.github.io/CyberTechHea...
04.09.2025 20:59
👍 1
🔁 0
💬 0
📌 0

Cyber Technology and Health
Separating AI Hope from AI Hype:
If you believe the hype, AI will soon take all our jobs, or solve all our problems, or destroy all boundaries between reality and lies. This brilliant podcast by @randomwalker.bsky.social Arvind Narayanan will help sort that out.
kbala97.github.io/CyberTechHea...
28.08.2025 21:01
👍 1
🔁 0
💬 0
📌 0

Cyber Technology and Health
Why Good Security Fails: The Asymmetry of InfoSec Investment
A paradox of security is that when you have invested appropriately and have less incidents, someone will ask: “Why are we spending on security when we don’t have any issues?"
@philvenables.bsky.social
kbala97.github.io/CyberTechHea...
13.08.2025 21:18
👍 1
🔁 0
💬 0
📌 0

Cyber Technology and Health
The Art of Selling as an Engineer: What Does a Solutions Architect Do?
A great podcast to learn about what a “Solutions Architect” does and brings value! As always, a great podcast from Daliani Liu.
kbala97.github.io/CyberTechHea...
10.08.2025 01:52
👍 2
🔁 0
💬 0
📌 0

Cyber Technology and Health
What are AI Foundational Models?
The current wave in AI is replacing task-specific models with those that are trained on a broad set of unlabeled data that can be used for different tasks, with minimal fine-tuning.
kbala97.github.io/CyberTechHea...
02.08.2025 23:47
👍 1
🔁 0
💬 0
📌 0

Cyber Technology and Health
AI Tools Make development Slower for Senior Open-Source Developers: AI tools take 19% longer to complete tasks compared to those working without AI assistance. A lot of nuances to this very interesting study.
kbala97.github.io/CyberTechHea...
26.07.2025 22:13
👍 1
🔁 0
💬 0
📌 0

Cyber Technology and Health
Input Validation Vulnerabilities Dominate MITRE’s 2024 CWE Top 25 List
kbala97.github.io/CyberTechHea...
20.07.2025 13:37
👍 1
🔁 0
💬 0
📌 0

Microsoft Readies Multiple Security Updates in Name of Windows 'Resiliency' -- Redmondmag.com
Seven months after unveiling its Windows Resiliency Initiative (WRI), Microsoft on Thursday announced a raft of new and upcoming security capabilities.
A year after the CrowdStrike incident spawned BSODs across the world, in July, Microsoft will roll out its Windows endpoint security platform to allow Windows solutions to run outside the kernel, hopefully eliminating the chance of such an incident again.
redmondmag.com/articles/202...
27.06.2025 10:35
👍 4
🔁 4
💬 0
📌 0
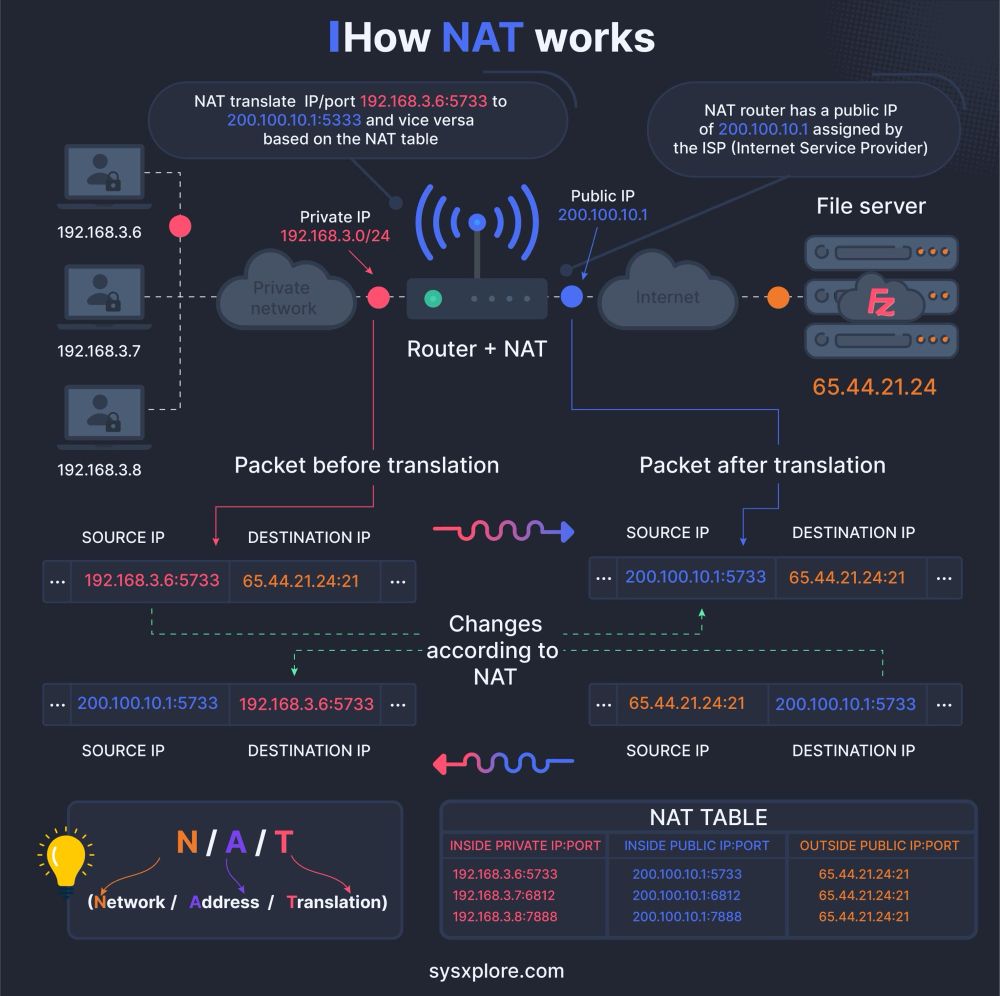
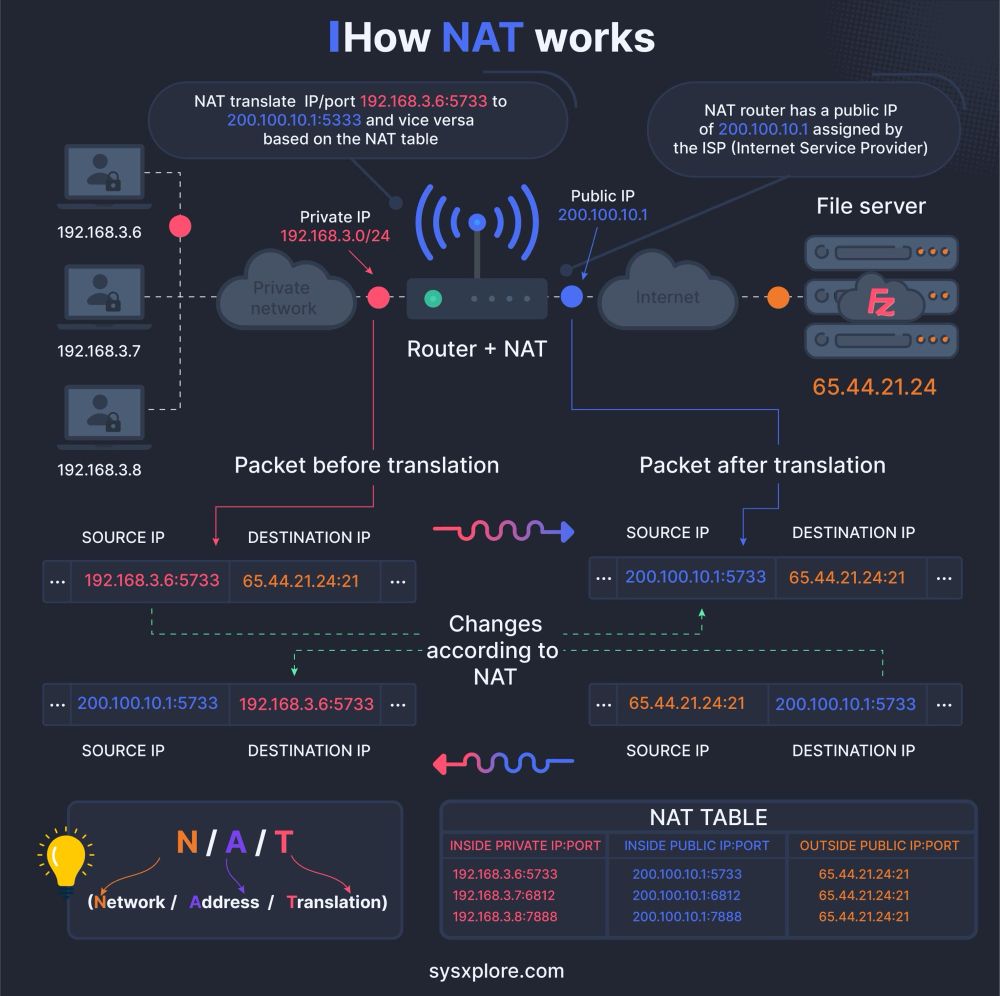
How NAT works?
14.12.2024 14:20
👍 11
🔁 3
💬 0
📌 0
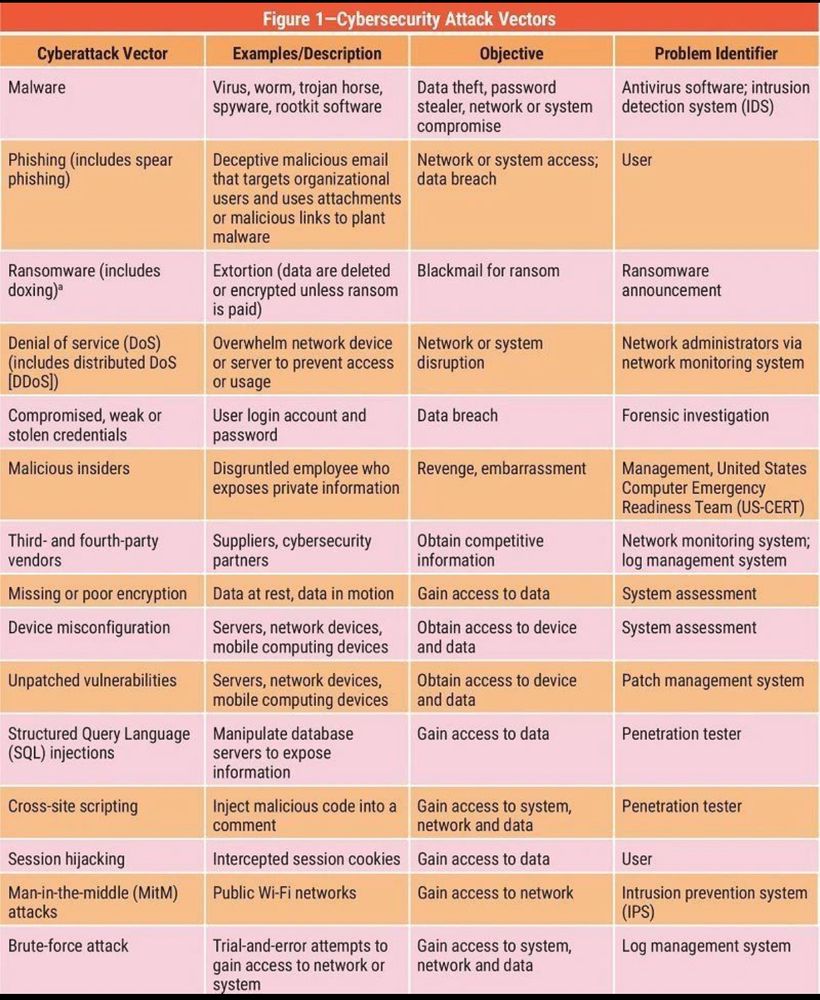
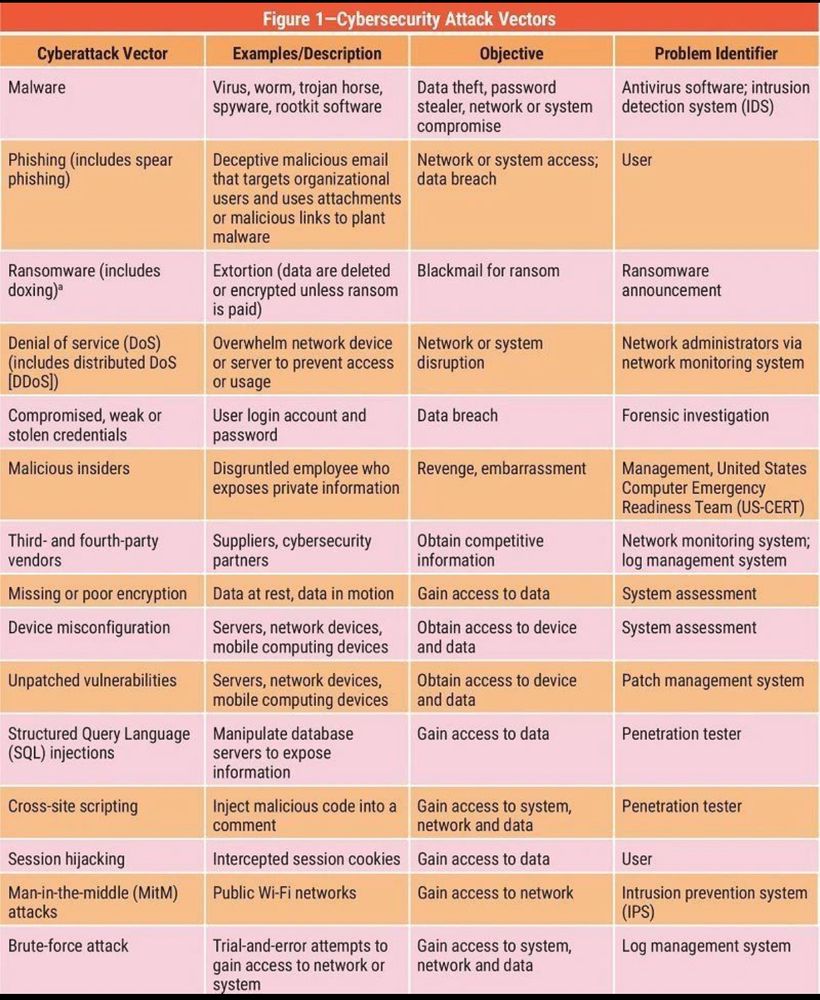
#Cybersecurity attack vectors.
06.12.2024 22:51
👍 16
🔁 3
💬 1
📌 1
Good to know:
Privacy advocates have long advocated using end-to-end encrypted apps. Signal and WhatsApp automatically implement end-to-end encryption in both calls and messages. Google Messages and iMessage also can encrypt calls and texts end to end
05.12.2024 01:46
👍 0
🔁 0
💬 0
📌 0
Love the simple graphic!
03.12.2024 02:23
👍 4
🔁 0
💬 0
📌 0
Super creative!
29.11.2024 13:19
👍 2
🔁 0
💬 0
📌 0