
saw this today too from @citizensoflorcana.bsky.social

saw this today too from @citizensoflorcana.bsky.social

It's on the booster box seen here
cdn11.bigcommerce.com/s-1ksvjps4tz...
It's confirmed that Merida (and presumably others) are coming in May in the Wilds Unknown set.
Not to mention, it was reportedly "just" a CI poly. Not even a full scope.

Oh no, someone gave me the Atlassian MCP
Nomination Form isn't available any more?

Mohammad wanted to get back at his enemies in the regime, by leaking their secrets to me. And he wanted to rekindle his relationship with the CIA, which had not ended on good terms. He was angry. He was determined. And he was desperate. www.theatlantic.com/magazine/202...
How many phishing sims have you triaged since I've left?
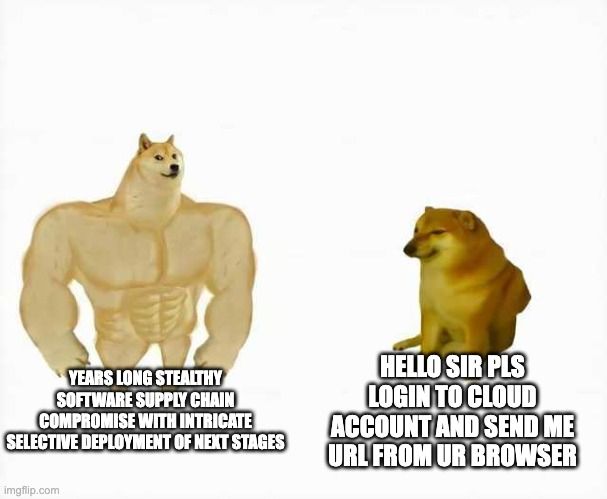
A study in the evolution of SVR cyberespionage tradecraft
That is a super cool lunch box
I'm wondering if there's some nexus of KnowYourCustomer that will allow access into gatekept versions of the models.
#ChangeMyMind #ElfOnTheShelf is a capitalist ploy to normalize a surveillance state to children.

New Iran banger from @saffronsec.bsky.social / @threatinsight.proofpoint.com just dropped. Full of good analytic tradecraft, Indicators and interesting lures showing how self aware Iranian cyber actors are...
www.proofpoint.com/us/blog/thre...

Ninja editing all references in $newjob's documentation from ProofPoint to Proofpoint.
Trying to decide if I should establish a threat actor naming schema based on flavors of Trader Joe's popcorn flavors
true analytic rigor comes from only opening your mouth when you have to and qualifying basically everything you say.
PR professionals hate this one trick...
Refusing to speculate past the published analysis makes for really "fun" media interviews
Talk to me when you've led a convoy of miniature Trader Joe's shopping carts on a successful supply run for apples and veggie straws

The tool has been released in the Proofpoint Emerging Threats public #GitHub for other defenders to leverage.
Learn more about it here: brnw.ch/21wWSH0
#PDF #threatdetection #cyberthreat
If your protest privacy/security advice does not start with a discussion of threat models, it is probably not good advice.
Wearing my NIMUC ribbon from my time with the Bureau on my Army dress uniform is one of my most niche flexes I have. Please respect my service.
ooof. here, they can't be legally driven on any road with a speed limit over 35 mph so it keeps them off the high ways
If you consider yourself a "Threat Intelligence Platform", don't email a spreadsheet of malicious indicators daily.
That helps no one.
What if @greg-l.bsky.social is our favorite threat actor?
In addition to being one of history's most successful musicians, Taylor Swift has also successfully used a fire extinguisher.
Here’s what the Taylor swift and Travis kelce engagement taught me about B2B sales:
Suspected attribution...
Phish & Chips.