For anyone interested in Velociraptor hunting - just added a refactored Windows.Detection.Webhistory into DetectRaptor 🚀
This is useful for hunting across browser artefacts - covers Chrome, Edge and Firefox
LINK: github.com/mgreen27/Det...
#DFIR
02.05.2025 06:46
👍 2
🔁 0
💬 0
📌 0

Just added LolRMM project to DetectRaptor for Velociraptor.
Expanded to look at installed applications, dns and running applications (process name and original/internal name of binaries on disk).
github.com/mgreen27/Det...
#dfir
06.03.2025 06:25
👍 5
🔁 0
💬 0
📌 0
github.com/Velocidex/ve...
21.02.2025 00:11
👍 0
🔁 0
💬 0
📌 0


This #100daysofyara shows but bad rules can be good when used correctly :)
Im using it for targeted live strings extraction in Velociraptor and some cool workflow to drive things like building yara rules.
The screenshot shows VQL to dynamically generate a yara rule to preferred string size.
21.02.2025 00:10
👍 1
🔁 0
💬 1
📌 0

Todays #100daysofyara rule targets the CISA report for this Contec CMS8000 backdoor
Rule: github.com/mgreen27/100...
01.02.2025 13:06
👍 2
🔁 1
💬 0
📌 0

#100daysofyara todays rule hits on a suspicious LNK executing mshta.exe using yara-x format.
github.com/mgreen27/100...
31.01.2025 12:40
👍 4
🔁 1
💬 0
📌 0


Messing with a couple of anomaly rules for #100daysofyara
1. Packer related API strings and no import
Rule: github.com/mgreen27/100...
2. Downloader related API strings and no import
Rule: github.com/mgreen27/100...
30.01.2025 12:00
👍 5
🔁 2
💬 0
📌 0


#100daysofyara todays rule finds kimsuky MSC payloads by unique Icon Index. In a previous rule I detected on a binary representation of pdf and was interested to understand how this may be generated.
27.01.2025 11:53
👍 4
🔁 1
💬 0
📌 0
VirusTotal
VirusTotal
Can you see this list?: www.virustotal.com/gui/collecti...
26.01.2025 13:21
👍 2
🔁 0
💬 1
📌 0
very cool!
25.01.2025 01:57
👍 2
🔁 0
💬 0
📌 0


#100daysofyara hunting inspired from a sample share from VT
1. Microsoft Teams without a MS cert
2. Detect cert metadata
github.com/mgreen27/100...
3. Anomaly detection for PE files with large difference between physical and virtual size of a section
github.com/mgreen27/100...
24.01.2025 12:46
👍 8
🔁 3
💬 1
📌 0
💡Interested in #memoryforensics ? Follow
✅ @volexity.com
✅ @volatilityfoundation.org
✅ @attrc.bsky.social
✅ @rmettig.bsky.social
✅ @nolaforensix.bsky.social
➡️ more to come!
20.11.2024 18:49
👍 53
🔁 23
💬 1
📌 0



#100daysofyara todays rule is detecting patched clr.dll in memory AmsiScanBuffer bypass. My @velocidex Windows.System.VAD artifact can be used to target clr.dll mapped sections for an easy detection.
Rule: github.com/mgreen27/100...
VQL: github.com/mgreen27/100...
22.01.2025 03:50
👍 6
🔁 5
💬 0
📌 0

Todays #100daysofyara rule looks for a PE file with an unusual debug info type. Yara doesnt directly expose these debug structures so had to search for the RSDS header and find type field by offset.
github.com/mgreen27/100...
21.01.2025 02:04
👍 4
🔁 2
💬 0
📌 0

This #100daysofyara rule looks for a PE with .reloc section and no relocation.
github.com/mgreen27/100...
20.01.2025 01:30
👍 3
🔁 1
💬 0
📌 0

This #100daysofyara rule looking for a PE with unusual NumberofRVAandSizes attribute
github.com/mgreen27/100...
18.01.2025 11:53
👍 2
🔁 2
💬 0
📌 0


#100daysofyara MSC files appear to store their icons inside a BinaryStorage field. Todays rule hits on a suspicious PDF icon.
Rule: github.com/mgreen27/100...
16.01.2025 11:22
👍 3
🔁 2
💬 0
📌 0

#100daysofyara This rule detects PE files with SUBSYSTEM_WINDOWS_GUI and no Window API function import.
Rule: github.com/mgreen27/100...
15.01.2025 10:46
👍 3
🔁 2
💬 0
📌 0

yara-x dump

#100daysofyara
more yara-x > Dumping a RedCurl malware pe I saw Rich Header and thought I would give it a try.
Rule: github.com/mgreen27/100...
14.01.2025 12:24
👍 3
🔁 2
💬 0
📌 0
Sorry - I think I was wrong.
I just asked a friend who went through 482 - he said this part takes 2 weeks and was great. PR is another story though.
13.01.2025 06:29
👍 1
🔁 0
💬 1
📌 0
I think you will find timeframe will be in months and not weeks.
13.01.2025 00:05
👍 0
🔁 0
💬 1
📌 0

#100daysofyara sometimes simple rules work really well!
In an IR last week, we discovered and stopped an in progress exfil. This process rule detects the in memory renamed rclone - should be cross platform.
Rule: github.com/mgreen27/100...
10.01.2025 23:05
👍 2
🔁 1
💬 0
📌 0


#100daysofyara continuing the LNK language theme. Todays rule hits ExtraData ConsoleDataBlock targeting less known Face Name field.
In the example rule I’m targeting the Korean font gulimche - ive added a few other system fonts for reference.
Rule: github.com/mgreen27/100...
08.01.2025 09:24
👍 4
🔁 0
💬 0
📌 0

#100daysofyara todays post is generic and looking at LNK files. Finding samples with specific attributes that may not be parsed (or dumped by yara-x) can be difficult. This rule finds LNK files with the rare in field CodePage language setting.
Rules: github.com/mgreen27/100...
07.01.2025 10:19
👍 10
🔁 3
💬 1
📌 0

#100daysofyara todays post I do a simple search for payload and QEMU local dll files observed both in the zip and imports of the QEMU executable.
I initially tried to do a fancy for loop looking at zip attributes but performance was terrible so simple strings wins the day!
github.com/mgreen27/100...
06.01.2025 11:44
👍 2
🔁 2
💬 0
📌 0
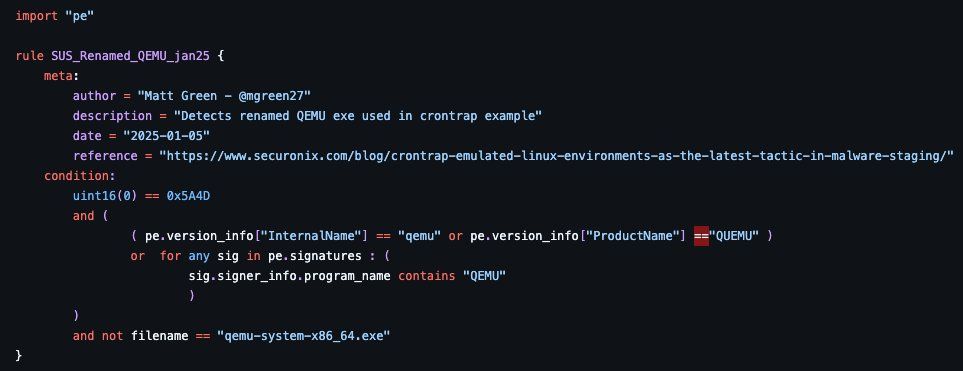
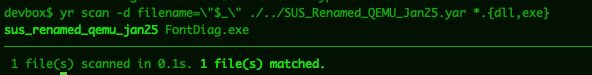
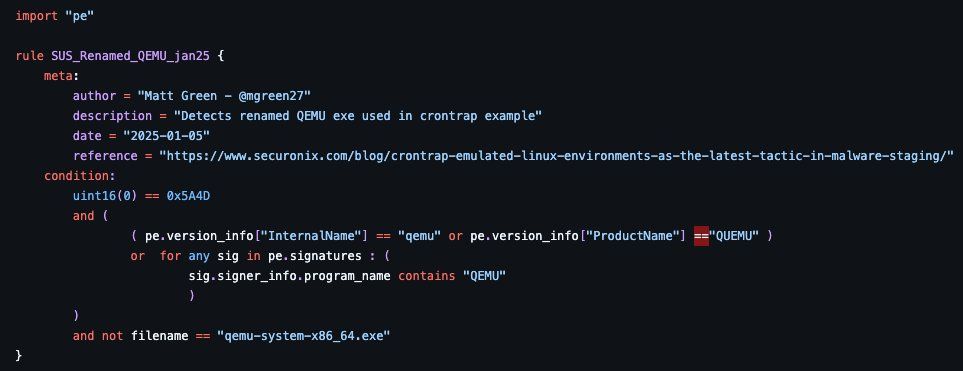
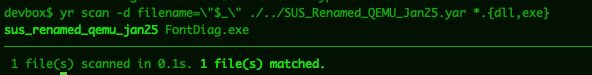
crossposting here #100daysofyara continuing to explore yara-x today I tried to detect a renamed QEMU exe using pe attributes and a dynamic variable.
05.01.2025 11:43
👍 7
🔁 3
💬 1
📌 0

Metasploit Weekly Wrap-Up 11/22/2024 | Rapid7 Blog
Roses are red, the sky is blue —
This week's #Metasploit wrap-up has Windows secrets dump improvements (and a JetBrains TeamCity login scanner, too!)
We're bad at poetry but good at shells. Check out the latest. www.rapid7.com/blog/post/20...
22.11.2024 21:01
👍 11
🔁 7
💬 0
📌 0