Microsoft says hackers are exploiting critical zero-day bugs to target Windows and Office users | TechCrunch
Critical security flaws targeting Windows and Office users allow hackers to take complete control of a victim's computer by clicking a malicious link or opening a file. Patch now.
By me: Microsoft has fixed three zero-day bugs in Windows and Office that are being actively abused by hackers to break into people's computers. Microsoft said three of the exploits are now public.
Google, which helped find the bugs, said one of them is under “widespread, active exploitation."
11.02.2026 21:33
👍 36
🔁 20
💬 8
📌 5
Outstanding work 👏
10.02.2026 09:49
👍 1
🔁 0
💬 0
📌 0

Report cover showing a dark blue patch with crossed sword, arrow and scroll emblem, titled "Unveiling GRU's Information Operations Troops (VIO)"
🔴 𝗡𝗘𝗪 𝗥𝗘𝗣𝗢𝗥𝗧
Last year, we've been able to unearth the infrastructure of the FSB's 16th Centre, combining #OSINT techniques and photos of old medals. We replicated this method to explore the Information Operations Troops (#VIO) of #Russia’s military intelligence service (#GRU).
09.02.2026 10:23
👍 26
🔁 18
💬 1
📌 8
Overall, this activity underscores the GRU’s continued reliance on credential harvesting as a low-cost, high-yield intelligence collection method, enabled by the persistent abuse of legitimate internet services and disposable infrastructure. (5/5)
07.01.2026 15:39
👍 1
🔁 0
💬 0
📌 0
Victimology indicates targeted activity rather than broad spraying. Observed targets included researchers linked to a Turkish energy research agency, a European think tank, and organizations in North Macedonia and Uzbekistan, which align with Russian intelligence priorities. (4/5)
07.01.2026 15:39
👍 2
🔁 1
💬 1
📌 0
The credential-harvesting pages captured usernames and passwords and then redirected victims to legitimate portals to reduce suspicion. BlueDelta refined its JavaScript to automate URL handling, victim tracking, and data exfiltration, lowering operational overhead and complicating detection. (3/5)
07.01.2026 15:39
👍 1
🔁 0
💬 1
📌 0
BlueDelta impersonated MS OWA, Google, and Sophos VPN login pages, often using multi-stage redirection chains hosted on free services such as Webhook[.]site, InfinityFree, Byet Internet Services, and ngrok. Several campaigns began with legitimate PDF lures to increase credibility. (2/5)
07.01.2026 15:39
👍 2
🔁 0
💬 1
📌 0

GRU-Linked BlueDelta Evolves Credential Harvesting
Insikt Group reveals how GRU-linked BlueDelta evolved credential-harvesting campaigns targeting government, energy, and research organizations across Europe and Eurasia.
Today, we released new @RecordedFuture research detailing BlueDelta’s expanded credential-harvesting activity observed between February and September 2025. #BlueDelta #APT28 #FANCYBEAR #ForestBlizzard #FROZENLAKE #ITG05 #PawnStorm #Sednit #Sofacy #TA422 (1/5) www.recordedfuture.com/research/gru...
07.01.2026 15:39
👍 7
🔁 5
💬 1
📌 0
Notably, the infrastructure shows rapid adaptation following previous takedown actions. BlueDelta continues to rely on free, disposable hosting and tunneling services, enabling resilient, low-cost credential theft operations targeting Ukrainian users. (5/5)
17.12.2025 15:46
👍 1
🔁 0
💬 0
📌 0
While the campaign does not reveal specific victim industries, this activity aligns with BlueDelta’s longstanding objective: collecting credentials to support GRU intelligence requirements amid Russia’s ongoing war in Ukraine. (4/5)
17.12.2025 15:46
👍 2
🔁 0
💬 1
📌 0
These pages harvested usernames, passwords, MFA codes, and CAPTCHA responses. BlueDelta refined its JavaScript to automate URL handling and exfiltration, reducing operational overhead and complicating detection efforts. (3/5)
17.12.2025 15:46
👍 0
🔁 0
💬 1
📌 0
BlueDelta impersonated UKR.NET login pages using multi-stage redirection chains hosted on free services such as Mocky, DNS EXIT, and later ngrok and Serveo. The group also deployed PDF lures to bypass automated email filtering and increase user trust. (2/5)
17.12.2025 15:46
👍 1
🔁 0
💬 1
📌 0

BlueDelta’s Persistent Campaign Against UKR.NET
Discover how Russia’s BlueDelta targets UKR.NET users with advanced credential-harvesting campaigns, evolving tradecraft, and multi-stage phishing techniques.
Today, we released new @RecordedFuture research detailing BlueDelta’s sustained credential-harvesting campaign targeting UKR.NET users between June 2024 and April 2025. www.recordedfuture.com/research/blu...
#BlueDelta #APT28 #FANCYBEAR #ForestBlizzard #FROZENLAKE #PawnStorm #Sednit #Sofacy (1/5)
17.12.2025 15:46
👍 3
🔁 2
💬 1
📌 0

APT28 Operation Phantom Net Voxel
APT28 Operation Phantom Net Voxel: weaponized Office lures, COM-hijack DLL, PNG stego to Covenant Grunt via Koofr, BeardShell on icedrive.
Great work by Sekoia uncovering new #BlueDelta #APT28 #Sofacy #FancyBear #ForestBlizzard #TAG110 malware samples. Linked to CERT-UA’s BeardShell & Covenant frameworks + revealed fresh weaponized docs & subtle TTPs. Activity ties to Russia-nexus ops incl. Double-Tap. blog.sekoia.io/apt28-operat...
16.09.2025 09:24
👍 2
🔁 1
💬 0
📌 0
This report on Stark Industries is a fantastic case study in the cat-and-mouse game between hosting providers and law enforcement. The new "Threat Activity Enabler" (TAE) terminology is spot-on and highlights the critical role these providers play in the cybercrime ecosystem.
27.08.2025 14:57
👍 3
🔁 4
💬 0
📌 0

Finnish police wiretap reveals Russian ‘shadow fleet’ captain instructed to destroy evidence
The captain of a Russia-linked oil tanker that damaged five subsea cables in the Baltic Sea was reportedly instructed to destroy evidence after the ship was seized by authorities.
Scandi noir meets The Wire...
🇫🇮🚢
The captain of a Russia-linked oil tanker that damaged five subsea cables in the Baltic Sea on Christmas Day was instructed by his shipping company to destroy evidence after the ship was seized by Finnish authorities, according to a wiretap transcript.
27.08.2025 12:33
👍 56
🔁 22
💬 0
📌 3
Fantastic new report by @julianferdinand.bsky.social and @aejleslie.bsky.social exposing Lumma’s vast info-stealing ecosystem—where affiliates juggle scams, MaaS platforms, and evasion tools to stay ahead of defenders💪 Great work team 🔥
21.08.2025 08:23
👍 4
🔁 1
💬 0
📌 0
Saher's first blog on the scourge that is ClickFix usage in the espionage space!!
Had to sneak in the UNK_RemoteRogue RDP shenanigans as well - a thus far unattributed group we assess to be Russia-aligned, using a pretty fun set of email tactics
17.04.2025 12:22
👍 16
🔁 7
💬 1
📌 0


Attention!
Check your Compromised Website Report for critical events tagged “fortinet-compromised” and follow Fortinet's mitigation advice on compromised devices:
fortinet.com/blog/psirt-b...
Data available from 2025-04-11+
shadowserver.org/what-we-do/n...
12.04.2025 12:15
👍 14
🔁 10
💬 3
📌 1
Snoop, a Romanian investigative journalism outlet, has linked an online advertising company named AdNow to intelligence officials from Russia's FSB and SVR services
snoop.ro/pe-urmele-ba...
04.03.2025 14:15
👍 79
🔁 34
💬 1
📌 0
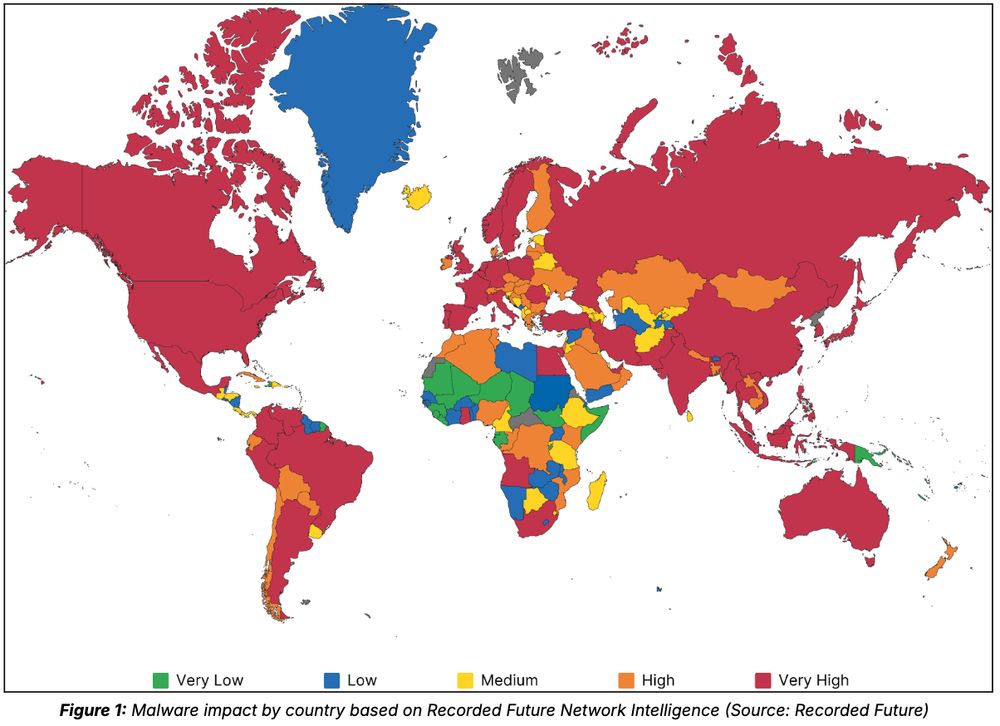
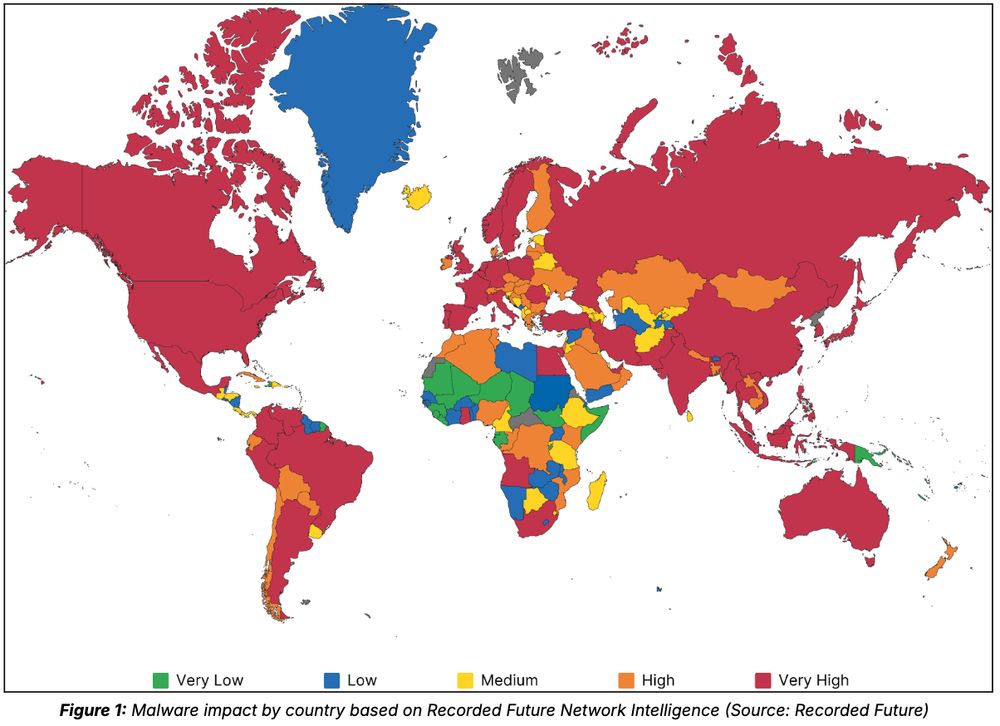
🪡 Our 2024 Malicious Infrastructure Report showcases the results of our detections across hundreds of malware families and threat actors, revealing victims in 200+ countries and highlighting the global scale of cyber threats.
Blog: www.recordedfuture.com/research/202... (1/10)
28.02.2025 15:03
👍 10
🔁 6
💬 1
📌 1
New Insikt Report just landed: RedMike AKA Salt Typhoon targeting of Global Telcos.
www.recordedfuture.com/research/red...
13.02.2025 10:25
👍 5
🔁 1
💬 0
📌 0