
Super proud of the FuTURES³ Lab and everything we accomplished in 2025, and excited for what’s ahead in 2026! Check out our work at futures.cs.utah.edu. 😃

Super proud of the FuTURES³ Lab and everything we accomplished in 2025, and excited for what’s ahead in 2026! Check out our work at futures.cs.utah.edu. 😃

Awesome to see @yeaseen.bsky.social's work on transpiler testing recognized by the Go2Hx dev community! community.haxe.org/t/go2hx-work-in-progress/2821/24#p-14532-research-paper-review-1 😁
Interested in improving transpilers? Check out our fuzzer TeTRIS! github.com/FuturesLab/TeTRIS

Transcompiler lost in translation? Let TeTRIS uncover all its syntax frustrations! Happy to share my #ACSAC paper w/@snagycs.bsky.social:"TeTRIS: General-purpose Fuzzing for Translation Bugs in Source-to-Source Transpilers"!
PDF: futures.cs.utah.edu/papers/25ACS...
Code: github.com/FuturesLab/T...


Crashing calculators and CAD editors? GUIFuzz++ is finally here to help make them better! 🔥
Come see my undergraduate student @trowlett0.bsky.social's very first paper "GUIFuzz++" at @aseconf.bsky.social this Wednesday.
Also now integrated in @aflplusplus.bsky.social! 😃
github.com/AFLplusplus/...
Super psyched to unveil GUIFuzz++: our grey-box fuzzer for desktop GUI applications, led by FuTURES³ Lab undergraduate researchers Dillon Otto and @trowlett0.bsky.social.
Coming soon to ASE 2025!
futures.cs.utah.edu/papers/25ASE...
github.com/FuturesLab/G...

GUIFuzz++ is the first general-purpose fuzzer for desktop GUI software! Fuzzing by translating AFL++ random input into user interaction with GUIs, leading to the discovery of 23 new bugs!
Paper: futures.cs.utah.edu/papers/25ASE.pdf
Source: github.com/FuturesLab/GUIFuzzPlusPlus
Go test some GUIs!
Fuzzing GUIs shouldn’t be harder than fuzzing files.
That's why I am excited to share my first paper (w/ fellow undergrad Dillon Otto + @snagycs.bsky.social) "GUIFuzz++: Unleashing Grey-box Fuzzing on Desktop Graphical User Interfacing Applications" at #ASE25.
Curious about fuzzing but don't know where to start? I wrote my first blog post on how to choose your target, build an AFL++-compatible harness, and avoid common pitfalls.
Check it out:
gabe-sherman.github.io/2025-09-17-b...
It's grey-box by default but also supports black-box fuzzing!

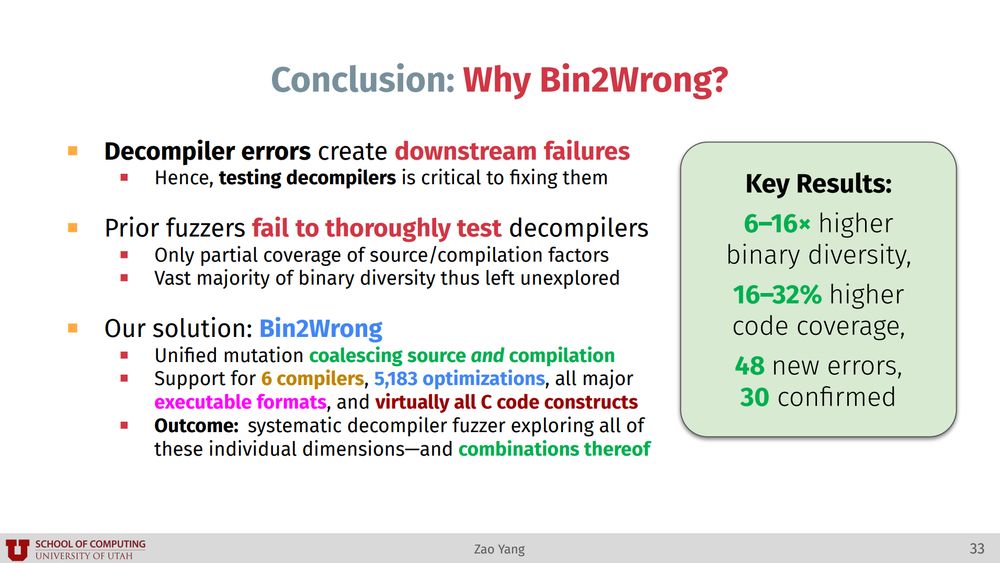
Fantastic job by my student @zaoyang.bsky.social presenting his decompiler fuzzing work Bin2Wrong at USENIX ATC! 🔥
Paper: futures.cs.utah.edu/papers/25ATC...
Slides: futures.cs.utah.edu/papers/25ATC...
Code: github.com/FuturesLab/B...
Impacts of Bin2Wrong-found bugs: binary.ninja/2024/06/19/r...
I'll be in Boston for #USENIX #ATC25. Reach out if you'd like to meet up to talk fuzzing / binary analysis!

Check it out!
📄 Paper: futures.cs.utah.edu/papers/25ATC.pdf
🛠️ Bin2Wrong: github.com/FuturesLab/Bin2Wrong
💥Some impacts of bugs Bin2Wrong found: binary.ninja/2024/06/19/restructuring-the-decompiler.html
#fuzzing #decompilation
Happy to share my upcoming #ATC25 paper w/ @snagycs.bsky.social: "BIN2WRONG: a Unified Fuzzing Framework for Uncovering Semantic Errors in Binary-to-C Decompilers"!
Bin2Wrong creates binaries by mutating source, compiler, optimizations, and format—revealing 48 new bugs in 7 decompilers! 💪
Paper: futures.cs.utah.edu/papers/25ICSE-b.pdf
Slides: futures.cs.utah.edu/papers/25ICSE-b_slides.pdf
Code: github.com/FuturesLab/OGHarn
Happy fuzzing!
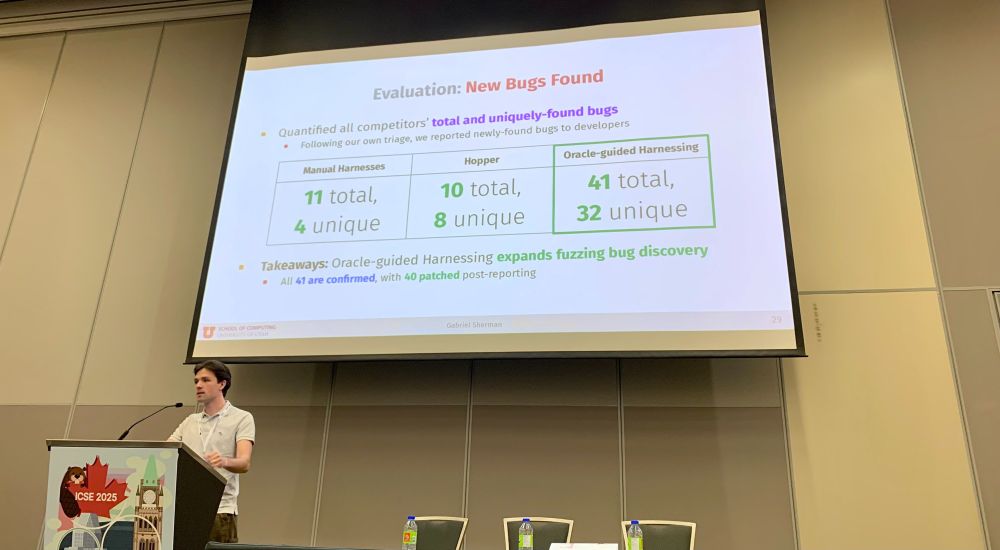
Awesome job by my PhD student @gabriel-sherman.bsky.social presenting his work on Oracle-guided C Fuzzing Harness Generation! @icseconf.bsky.social
TLDR; 41 new bugs (40 now patched)... with 0 false positives!
✈️ I'll be at @icseconf.bsky.social this week — find me if you'd like to chat about all things fuzzing / binary analysis!

The April 16 Memorial is pictured in front of Burruss Hall against a blue sky.
Today, we’re honoring the lives of the 32 Hokies who were tragically taken from their loved ones and the Virginia Tech community on April 16, 2007.
On the 2025 Day of Remembrance, we're honoring the lasting impact they continue to have on our world. #VTWeRemember 🧡
[RSS] What could cause a memory corruption bug to disappear in safe mode?
devblogs.microsoft.com ->
Original->

OGHarn mutationally generates harnesses and uses 3 oracles of behavior to determine both their utility and validity, leading to the discovery of 41 new bugs(with zero false-positive crashes)!
Paper: futures.cs.utah.edu/papers/25ICS...
Source: github.com/FuturesLab/O...
Happy Fuzzing! 🐛
Need a fuzzing harness? No time to write one? Tired of false-positives? Let OGHarn lead the way to bug discovery!🐞
I'm excited to share my paper(with @snagycs.bsky.social)"No Harness, No Problem: Oracle-guided Harnessing for Auto-generating C API Fuzzing Harnesses" at @icseconf.bsky.social 2025!
I will really miss the good ol' days of Twitter. As a grad student it was a go-to place for all things fuzzing/security, and I'm sad to see it fall apart. Having folks spread-out on three platforms (this, Mastodon, and X) will never quite feel the same. 😔
Howdy, world. This interface looks oddly familiar...