Thank you -- hoping to get a few more blog posts out soon :)
Thank you -- hoping to get a few more blog posts out soon :)
userland ROP on day 1 💪

New blog post with @shubs.io:
We found a vulnerability in Subaru where an attacker, with just a license plate, could retrieve the full location history, unlock, and start vehicles remotely.
Full post here: samcurry.net/hacking-subaru
Documentary on Hackers Who Get Paid to Hack Companies. @CyberNews interviewed Bryce (@realytcracker), Ben (@NahamSec), Sam Curry (@zlz), Frederik (@stokfredrik), Neiko (@_specters_), Vanya (@BusesCanFly), Phoenix (LilRed), André (@0xacb).

Did you know you can use an ancient magic cookie to downgrade parsers and bypass WAFs?! Hope you enjoy this quality bit of RFC-diving from @d4d89704243.bsky.social!
portswigger.net/research/byp...
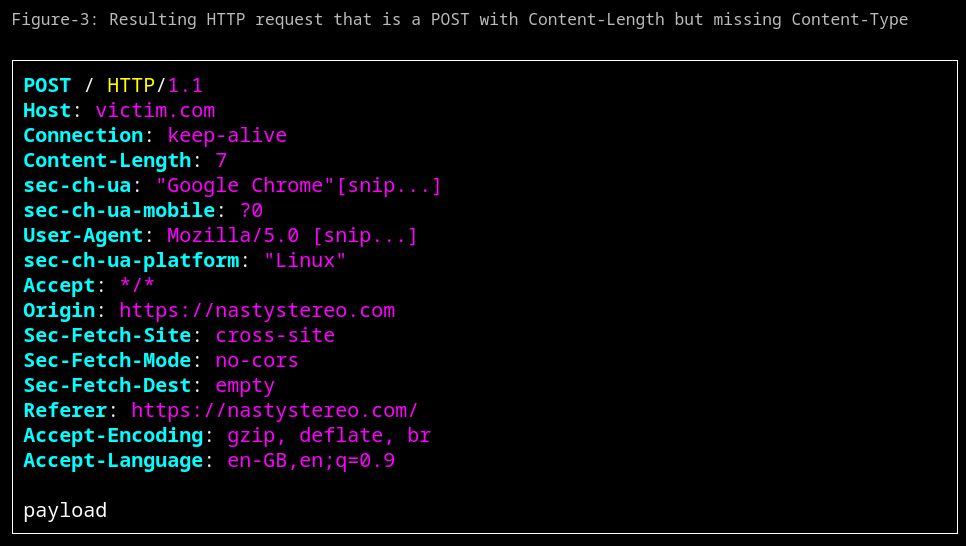
My latest blog post is live! nastystereo.com/security/cro...
Read how to send a cross-site POST without including a Content-Type header (without CORS). It even works with navigator.sendBeacon

This must be the result of the attempts
I'm slowly making my way there... will see where it starts giving me a bad request error as I approach 253 😄
Yup, all parts <63. Wondering if Bluesky explicitly prevented huge usernames as a quality of life thing? 👀

Does anyone know the max size limit for Bluesky usernames? The DNS and everything resolves correctly for this (253 characters), but it seems to throw 400 bad request when I actually try to assign it.