
DKnife primarily targets Chinese-speaking users, indicated by credential harvesting for Chinese-language services, exfiltration modules for popular Chinese mobile applications and code references to Chinese media domains.

DKnife primarily targets Chinese-speaking users, indicated by credential harvesting for Chinese-language services, exfiltration modules for popular Chinese mobile applications and code references to Chinese media domains.

The #Shadowpad samples are signed with two certificates both issued from the signer “四川奇雨网络科技有限公司”. This is a company located in Sichuan Chengdu, China specialised in developing computer software and providing network communication devices.

DKnife inspects network traffic to monitor and report users’ activity to its remote C2. Observed telemetry spans multiple categories, including messaging on #Signal and #WeChat, news consumption, map searches, dating app usage, taxi requests, and email activity.

DKnife can hijack #Android application updates by intercepting the update manifest requests. The targeted applications are mostly popular Chinese-language services.

🔥 NEW research published: We uncover #DKnife, a China-nexus gateway-monitoring framework that intercepts network traffic, monitors user activity, and delivers malware #Shadowpad & #DarkNimbus via routers and edge devices.
blog.talosintelligence.com/knife-cuttin...

1/ Today we release a new report exposing previously undisclosed entities connected to the wider #Intellexa ecosystem as well as newly identified activity clusters in Iraq and indications of activity in Pakistan: www.recordedfuture.com/research/int...

So excited that I’m going to present my latest research at @districtcon.bsky.social in January! The last round of tickets are going on sale on this Sunday (Nov 16th @12pm EST). Looking forward to see you in DC!

New Iran drop from me tracking an attribution nightmare - UNK_SmudgedSerpent! A little Charming, a little Muddy, and a lot C5. Targeting policy experts with benign conversation starters, health-themed infra, OnlyOffice spoofs, and RMMs. Check out the full story www.proofpoint.com/us/blog/thre...

Gonna be in Belgium for the first time after living in Europe for 7 years. Come catch me if you are at @what-is-sos.bsky.social tomorrow!!!
Great work and thanks for referencing our research on redefining IAB! The four-tier classification framework is insightful for identifying collaborative campaigns!
I don’t have enough data to speak confidently on that. In my own observations I haven’t seen much SNMP exploitation, though I’ve come across a few cases of suspected tunnelling traffic.

Great investigation from Trend Micro with the contributions from Joey Chen! Threat actor are actively targeting the SNMP protocol on routers for exploitation.
www.trendmicro.com/en_us/resear...

Quite a bit of CN APT activity in europe in the past week
strikeready.com/blog/cn-apt-...
As always, if you're interested in tuning your skills, download the samples here github.com/StrikeReady-...
There's was a mad dash on SOS tickets over the weekend.
SOS is two weeks away, if you've been putting off getting a ticket... your time is now.
stateofstatecraft.com/register

text that reads: In Italy, investigative journalist Gianluigi Nuzzi was tracked days after publishing a dramatic exposé of corruption in the Vatican, as police closed in on his source. In California, Anne Wojcicki, founder of DNA startup 23andMe and then married to Google’s Sergey Brin, was tracked more than a thousand times as she moved across Silicon Valley. And in South Africa, associates of Rwandan opposition leader Patrick Karegeya were tracked before his assassination in a Johannesburg hotel room.
Another major surveillance provider exposed: First Wap
Its product was used to track some very high-profile figures
www.lighthousereports.com/investigatio...

👾 Had a great time at the DC4131 Padawan CTF with the Swiss @defcon.bsky.social community! Back to CTFs after a while teamed up with J & M and knocked out a few challenges. Go, pwnrpuffgirls girl power! 💪 Big thanks to the organizing team. Looking forward to the next one! #CTF


Caught a Pokémon at @defcon.bsky.social 😍 Big fan of @lauriewired.bsky.social. It was so interesting to discuss about reverse engineering with her. Please can we all have a card like this?

At @defcon.bsky.social today. Come find me!
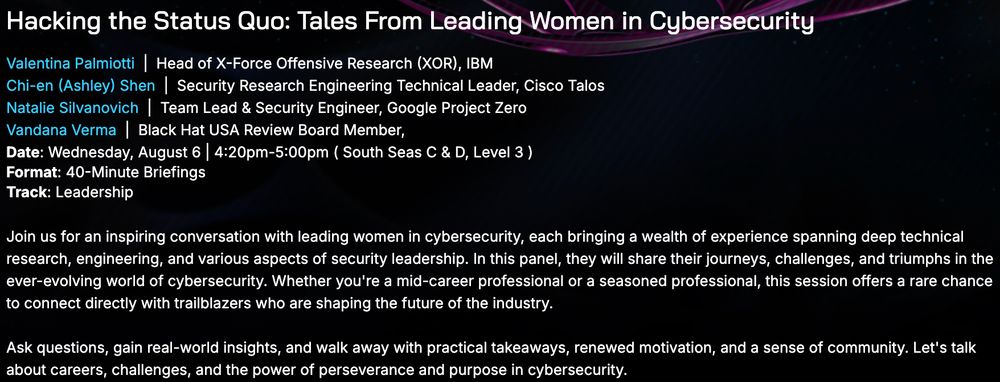
Heading to Hacker Summer Camp next week? 🌵If you’re curious about the journeys behind the hacks, the challenges and the stories that shaped us, come join our panel: "Hacking the Status Quo”. With Valentina Palmiotti (Chompie), Natalie Silvanovich, and Vandana Verma. #BHUSA #blackhatusa
The SOS conference is officially THREE months away! On October 28, we gather to discuss the latest developments in nation-state operations with leading experts!
⏰ CFP Ends September 1st!
🐧 Early Bird Tickets almost sold out!
🕵️ Come talk espionage, sabotage, ORBATs, and more!
stateofstatecraft.com

Excited to see another threat intel focused conference taking place in Europe, and it’s organized by threat analyst in the field! The CFP is opened until Sept 1st. Looking forward to see your amazing research!
#What_is_SOS #StateOfStatecraft
www.stateofstatecraft.com
Had a great time on the @malspace.bsky.social podcast with Julien talking about my PIVOTcon presentation from tracking compartmentalized attacks to thoughts on attribution. Fun convo (and I loved the theme song at the end!). 🎶 Thanks for having me!
malspace.com/episodes/mul...

I'm excited to return to Black Hat USA this year and have the opportunity to give away one briefings pass to the conference. If you're a student or someone who could use a little support to attend, I'd love to hear from you. DM me if you're interested!
#BHUSA
Looking forward to my week at @botconf.infosec.exchange.ap.brid.gy ! Please come say hi if you are around! #Botconf2025

Talks from the OffensiveCon 2025 security conference, which took place last week, are now available on YouTube
www.youtube.com/playlist?lis...
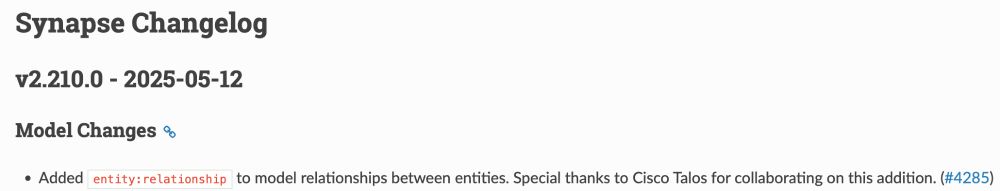
Huge thanks to @vertexproject.bsky.social for updating Synapse to support the new "relationship" context.
We’re excited to see this research foster collaboration and push real change across the threat intelligence community. (3/3)

In blog 2, we dive into the challenges of investigating compartmentalized campaigns. We share our approach to identifying them and propose an extended Diamond Model with a new "relationship" layer to close the analytical gaps. (2/3)
blog.talosintelligence.com/compartmenta...
📡 New blogs out: Compartmentalized attacks are no longer limited to financially motivated actors, state-sponsored groups are adopting them too. We propose a new taxonomy for initial access groups to reflect broader motivations and affiliations. (1/3)

@greg-l.bsky.social drops knowledge on TA406 (Konni) as North Korea shows new interest in Ukraine, likely to keep tabs on the progress of the war and Russia's ability to keep pace on the battlefield www.proofpoint.com/us/blog/thre...


Had an amazing time speaking at @pivotcon.bsky.social last week! Grateful for the chance to share insights and connect with the brilliant minds. PIVOTcon remains my favorite threat intel event in Europe. Huge thanks to the organizers for creating this community and the memorable experience.