
Another example of a Windows 0-day found with PrivescCheck. Congrats to Compass Security for investigating the issue and exploiting it. 👏
blog.compass-security.com/2025/04/3-mi...

Another example of a Windows 0-day found with PrivescCheck. Congrats to Compass Security for investigating the issue and exploiting it. 👏
blog.compass-security.com/2025/04/3-mi...

I got a chance to try out @Burp_Suite Burp AI, and it's... honestly really cool 😅 Video showcase where we cruise through a web app scan, crawl and audit, and it rips through findings including an explicit UNION SQL injection vulnerability and more 🤩 youtu.be/v-McepNOrTQ

Calling all relationship builders! 👋 We're looking for a Channel Account Manager to help grow our partner network for BloodHound Enterprise.
If you love connecting with VARs, distributors, & consultants, submit your application today: ghst.ly/3XYrzO4
New blog post 🤗
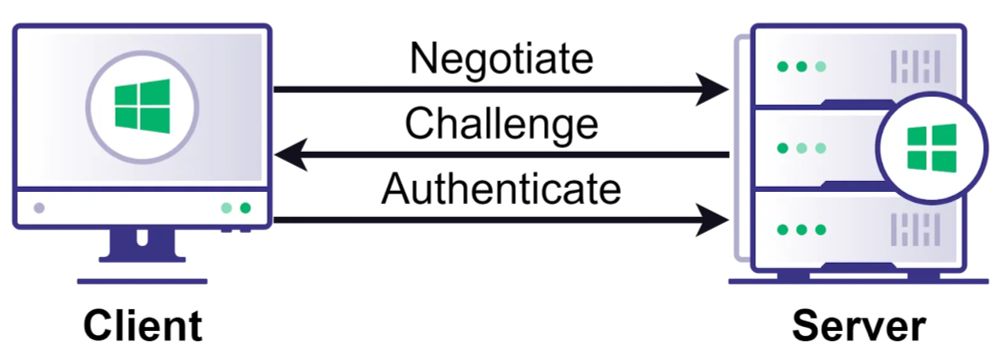
Think NTLM relay is a solved problem? Think again.
Relay attacks are more complicated than many people realize. Check out this deep dive from Elad Shamir on NTLM relay attacks & the new edges we recently added to BloodHound. ghst.ly/4lv3E31

New tool drop from jfjallid (not on this platform)
github.com/jfjallid/go-...

New day, new #BloodHoundBasics post!
DYK that BloodHound CE now supports deep linking? This week, we released early access support that goes beyond what the old back button offered! Go back (& forward), & share your current view of the graph w/ your fellow operators today!
1/2

🎤As they say, better late than never. Our latest episode is out now! Brought to you by linkedin.com/company/secu...

Zscaler has published a technical report on HijackLoader (IDAT Loader, GhostPulse) and its recent changes, such as its new call stack spoofing module, anti-VM module, and support for scheduled task persistence
www.zscaler.com/blogs/securi...

Spent the evening deep diving into MCPs and started a new project: roadrecon_mcp_server! This #MCP takes the web GUI output from the awesome ROADtools by @dirkjanm.io and offers tools to Claude (or your #AI agent of choice) to interact with the data:
github.com/atomicchonk/...
Looking forward to your vids.

Join @alethe.bsky.social for a behind-the-scenes look at real #RedTeam ops: successes, failures, and the lessons that could level up your security game. #cybersecurity
bishopfox.com/resources/re...

🔒 Are your endpoint defenses prepared to counter EDR bypass techniques?
Discover the latest tactics used by attackers and learn actionable countermeasures during Binary Defense's ThreatTalk webinar. Save your seat today: www.binarydefense.com/resources/we...
#Cybersecurity #ThreatTalk #EDR

Don't miss our next BloodHound Enterprise demo webinar, happening April 8! Register now to hear from Jacob Julian on why you should care about Attack Paths, and how BloodHound approaches identification and elimination.
Register ➡️ ghst.ly/apr-demo-bsky

Automatic browser SSO with a PRT on a victim device over an Outflank C2 implant 🥰 using ROADtools and some hackery from Max Grim.

Troy Hunt's mailing list got phished. Commiserations to him. If it can happen to Troy, it can probably happen to you.
www.troyhunt.com/a-sneaky-phi...

[Blog] This ended up being a great applied research project with my co-worker Dylan Tran on weaponizing a technique for fileless DCOM lateral movement based on the original work of James Forshaw. Defensive recommendations provided.
- Blog: ibm.com/think/news/f...
- PoC: github.com/xforcered/Fo...

Don't miss my teammates as they present the 2025 Red Canary Threat Detection Report tomorrow afternoon! This report is overwhelming with goodness, and they'll help you navigate it. 😀 redcanary.com/resources/we...
Ransomware groups have declared war on small business. It’s time we do the same to them.

Rust is gaining traction in malware development—offering evasion advantages over C. Security Consultant Nick Cerne breaks down why, compares reverse engineering challenges, and builds a Rust-based dropper to stage Sliver.
bishopfox.com/blog/rust-fo...

Hey all! NerdWallet is hiring for several Staff Software Engineer roles in US and Canada. They are all remote.
➡️ jobs.diversifytech.com

We explain everything you need to know about Bluetooth, the long-standing wireless connectivity standard.

Attackers see what you don't: paths between your cloud & on-prem systems.
Our Chief Product Officer Justin Kohler will be at #GartnerIAM demonstrating how attackers exploit these connections & how Attack Path Management can help close these gaps. ghst.ly/4kzkFbB
Happy #BloodHoundBasics day! This week we are looking at how BloodHound classifies Tier Zero.
Q: Why is not just the DA group Tier Zero but also all members?
A: BloodHound classifies a few default Tier Zero assets, then adds more w/ logic from known attack techniques.
1/8

Hello Bluesky! We're live!👋 And so is our new release! Cobalt Strike 4.11 introduces a novel Sleepmask, a novel process injection technique, a new prepend reflective loader with new evasive options, asynchronous BOFs, DNS over HTTPs and more!
cobaltstrike.com/blog/cobalt-...

Malicious OAuth attacks are all the rage right now!
Ex 1 - www.bleepingcomputer.com/news/securit...
Ex 2 -

Evilginx Pro (@mrgretzky.breakdev.org ), Pre-auth RCE in a CMS (@chudypb.bsky.social), GOAD ADCS, YouTube email disclosure (@brutecat.com), SAML parser bug (ulldma.bsky.social), and more!
blog.badsectorlabs.com/last-week-in...

KrbRelayEx-RPC tool is out! 🎉
Intercepts ISystemActivator requests, extracts Kerberos AP-REQ & dynamic port bindings and relays the AP-REQ to access SMB shares or HTTP ADCS, all fully transparent to the victim ;)
github.com/decoder-it/K...

A table that lists Microsoft RDWeb, Cisco ASA, SonicWall NetExtender, Fortinet SSL VPN, WatchGuard SSL VPN, Palo Alto GlobalProtect, and Cisco Gateway
The BlackBasta ransomware gang developed and used its own custom tool to brute-force enterprise firewalls and VPN remote-access products.
Named Bruted, the tool was written in PHP and could brute-force the following products (see image)
blog.eclecticiq.com/inside-brute...

🔐 The threat of #EDR Killer attacks is rising quickly, leaving organizations exposed to sophisticated attacks.
Join Binary Defense's #ThreatTalk to learn strategies that will keep your business ahead of threat actors. Secure your spot here👉: www.binarydefense.com/resources/we...
#Cybersecurity