Excellent blog as always from James
Excellent blog as always from James
Part 2 of @tiraniddo.dev’s Windows Administrator Protection journey is here!
projectzero.google/2026/02/wind...
Yes they do not share pdf. Chromes is extremely fast, loads the Arm ARM in a few seconds.
Chrome is also extremely fast for PDF. Edge is super slow. Was surprised they do not use the same engine
Was wondering if MTE would impact it, glad to see it mentioned at the end! Very nice write up as always from GPZ

Oh hey, we're [finally] killing RC4 everywhere officially. www.microsoft.com/en-us/window...
advice to every Rust organizational decisionmaker out there: shut up, stop making excuses, and take notes from the PSF: bsky.app/profile/pyth...
Yeah but remember Trump said that was Biden’s economy lol

Over the summer we published documentation for the new usermode accessor APIs that we will be making all drivers use going forward. We’ve now ported over 2/3rd of our usermode accesses in kernel code to use these APIs and the rest is in progress! learn.microsoft.com/en-us/window...
We hold ourselves to a high performance bar when rolling out new security mitigations only to have security software completely tank system performance. Sometimes makes me wonder why we care so much 🥲

I'm thrilled to announce "HTTP/1 Must Die! The Desync Endgame", at #BHUSA! This is going to be epic, check out the abstract for a teaser ↓
I do! Easier to make a local copy of.
Are the slides published?
I actually was not super optimistic this would work due to compatibility but it ended up being pretty easy to get through.
This was my team, sorry not sorry :-)
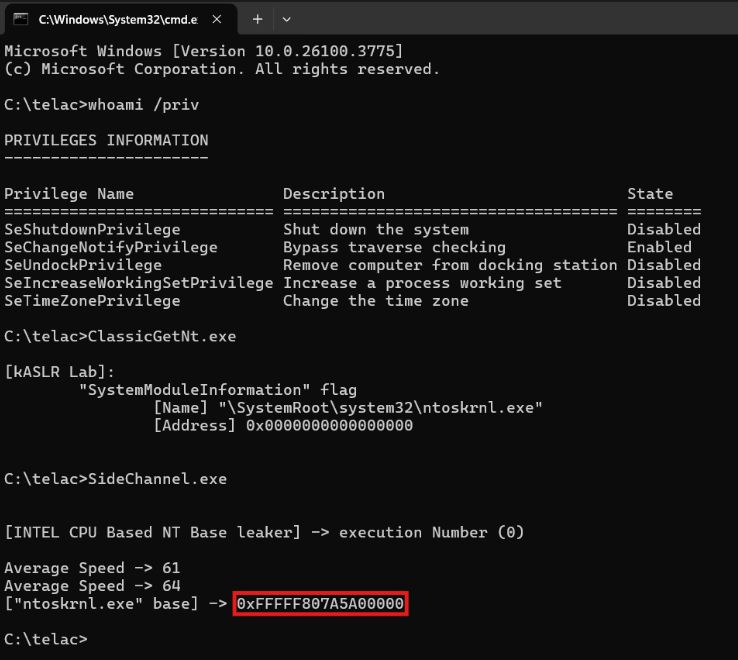
Bypassing kASLR via Cache Timing : r0keb.github.io/posts/Bypass...
kASLR Internals and Evolution : r0keb.github.io/posts/kASLR-... credits @r0keb

Important news: Microsoft is working to bring SMAP into Windows
www.youtube.com/watch?v=-3jx...
Great talk by Joe Bialek from MORSE team
Very cool!
New blog post on the abuse of the IDispatch COM interface to get unexpected objects loaded into a process. Demoed by using this to get arbitrary code execution in a PPL process. googleprojectzero.blogspot.com/2025/01/wind...
In the past 6 months we’ve ported over 2,000 usermode accesses in ntoskrnl and securekernel to usermode accessors and discovered and fixed a handful of vulnerabilities in the process. I never thought we’d see such large scale refactoring
Simple 3 steps to boot Arm64 WinVOS in QEMU (emulation mode).
linaro.atlassian.net/wiki/spaces/...
Boots in under a minute.

TIL we published WinVOS, a super lightweight Windows SKU. This is a great way to debug ultra hot system calls and other things that are just too noisy on a full version of Windows. I use it for development. learn.microsoft.com/en-us/window...
I didnt realize we publish WinVOS, that’s awesome
More usermode accessor improvements are landing in Windows 😊
Work-around for long-term issue in Cygwin's fork() running on Arm64 resolved.
Really appreciate the energy and collaboration with the @msys2org.bsky.social folks!