
We released version 1.11.2 of #OWASP #WrongSecrets: it's faster than ever, has now 55 challenges and a lot of fun! Check it out at github.com/OWASP/wrongs... or test it at www.wrongsecrets.com and don't forget to give the repo a 🌟 if you like it!

We released version 1.11.2 of #OWASP #WrongSecrets: it's faster than ever, has now 55 challenges and a lot of fun! Check it out at github.com/OWASP/wrongs... or test it at www.wrongsecrets.com and don't forget to give the repo a 🌟 if you like it!

I just built a custom action to let you test for race conditions with a single click! No tab groups required, and it uses the cutting edge single-packet attack under the hood: gist.github.com/albinowax/10...
For more info check out portswigger.net/research/sma...

Ever heard of LLM poisoning? 🤔
Recently, Leif Dreizler joined Travis McPeak and William Bengtson on the @404security.bsky.social podcast to discuss how misinformation websites are intentionally spreading fake news to influence AI model responses.
🎧 Listen here: www.resourcely.io/podcast/deal...
I will for sure!
I will attend!

Hello friends. The dreaded and long awaiting blog on WHAT THE FUCK HAPPENED TO THE CYBERSECURITY JOBS MARKET has arrived.
tisiphone.net/2025/04/01/l...
I'm sorry.

As a follow up to @maxenceschmitt.bsky.social's amazing #CSPT research, we've published a list of resources to help people interested in this class of vulnerabilities. Check it out today for video, tools, challenges and variety of publications!
blog.doyensec.com/2025/03/27/c...
#Doyensec #appsec

The Threat Modeling Connect community are launching the first-ever community-driven State of Threat Modeling (SOTM) Report, led by @rewtd.bsky.social
and Dave Soldera, and we’d love your input!
docs.google.com/forms/d/e/1F...
The survey will take 15-20 minutes to complete.
#cybersec #infosec


OWASP Global AppSec EU 2025 Barcelona: full training schedule is out now!
Day 3 is packed with even more hands-on training sessions to enhance your AppSec expertise!
Register now:
owasp.glueup.com/eve...
#AppSecEU2025 #Cybersecurity #DevSecOps #SecureCoding #ThreatModeling #Infosec #Barcelona

Exciting news! The #OWASP Global #Appsec SF videos have arrived! 🎥 Get ready to boost your knowledge and skills by checking them out here: www.youtube.com/play...

You might have noticed that the recent SAML writeups omit some crucial details. In "SAML roulette: the hacker always wins", we share everything you need to know for a complete unauthenticated exploit on ruby-saml, using GitLab as a case-study.
portswigger.net/research/sam...
There's now a ZAP Slack that's open to everyone. You can get an invite to it via zaproxy.org/slack/invite
AppSec Ezine - 573rd pathonproject.com/zb/?3970e59b... #AppSec #Security 🎁

🤔 Based on issues that I have seen during recent assessments, I updated my code sharing project with a method related to JWT based tokens:
#appsec #appsecurity #jwt #web
🌍 URL:
github.com/righettod/co...
righettod.github.io/code-snippet...

Get ready for an eye-opening session with Kevin Hemmingsen, Director of Trust & Security at Bugcrowd as he explores lessons from bug bounty / offsec to help devs build more securely at the OWASP Security Summit!
OWASP Community Save 25% on tickets: http://www.eventbrit...
Practice on Portswigger Academy

The results are in! We're proud to announce the Top 10 Web Hacking Techniques of 2024! portswigger.net/research/top...

GET /%0D%0ASet-Cookie: foo=bar 403 Forbidden GET /%E4%BC%8D%E4%BC%8ASet-Cookie: foo=bar 200 OK Set-Cookie: foo=bar
Discover blocklist bypasses via unicode overflows using the latest updates to ActiveScan++, Hackvertor & Shazzer! Thanks to Ryan Barnett and Neh Patel for sharing this technique.
portswigger.net/research/byp...

Sarah-Jane Madden is a keynote speaker at OWASP Global AppSec EU 2025
🎟️ Attention to those in App Sec, Cybersecurity, and Developers: take advantage of the early bird discount!
Don’t wait, register now!
owasp.glueup.com/eve...
#owaspglobalappseceu2025 #AI #threatmodeling #devsecops #infosec
I've just released HTTP Request Smuggler 2.17 which fixes a nasty Client-Side Desync false-negative. Big thanks to @t0xodile.com for reporting it! Hope you all find some nice CSDs in 2025 :)

Nominations are now open for the Top 10 Web Hacking Techniques of 2024! Browse the contestants and submit your own here:
portswigger.net/research/top...

🚨 Attention all developers and code enthusiasts! Get ready to elevate your skills with "Alice and Bob Learn Secure Coding." Secure your copy now and embark on a transformative learning experience.
shehackspurple.ca/bo...

Somebody uploaded to SlideShare the slides of my talk at @northsec.bsky.social 2023 🌐
It’s the sequel of the first @burpsuite.bsky.social talk I ever gave, exactly 10 years before 🛠️
Enjoy these 50 slides of Burp tips 🎁🎅
Extended the starter with shy writers! 😀 If you're not on the list but write about web security, then feel free to reply with the article you're most proud of, and I will add you to the pack!
Make sure to resubscribe to not not miss on the amazing 🌐research!
go.bsky.app/9JXnB17

Screenshot of Burp's HTTP settings, where streaming URLs must be defined

Chunked response as seen in Repeater, with chunk metadata (their size) not stripped
Ever wondered why you NEVER see chunked responses in Burp? 🤔
The answer is simple, default settings hide them! 🫣
Go to "Settings > Network > HTTP > Streaming responses" to make them appear 🔍
Check out the tools I've been working on this year:
🔐 Hackvertor: Web app: hackvertor.co.uk
🔒 Hackvertor BApp: portswigger.net/bappstore/65...
⚡ Shazzer: shazzer.co.uk
🛠️ Recorder: Chrome extension: chromewebstore.google.com/detail/burp-...
🕵️ DOM Invader: portswigger.net/burp/documen...

Overview of the attack flow

Overview of how a large number of credentials were leaked

Clusters of fake GitHub profiles

Phishing e-mail
New research: We've been monitoring a threat actor publishing dozens of trojanized GitHub repositories targeting threat actors, leaking hundreds of thousands of credentials along the way
securitylabs.datadoghq.com/articles/mut...
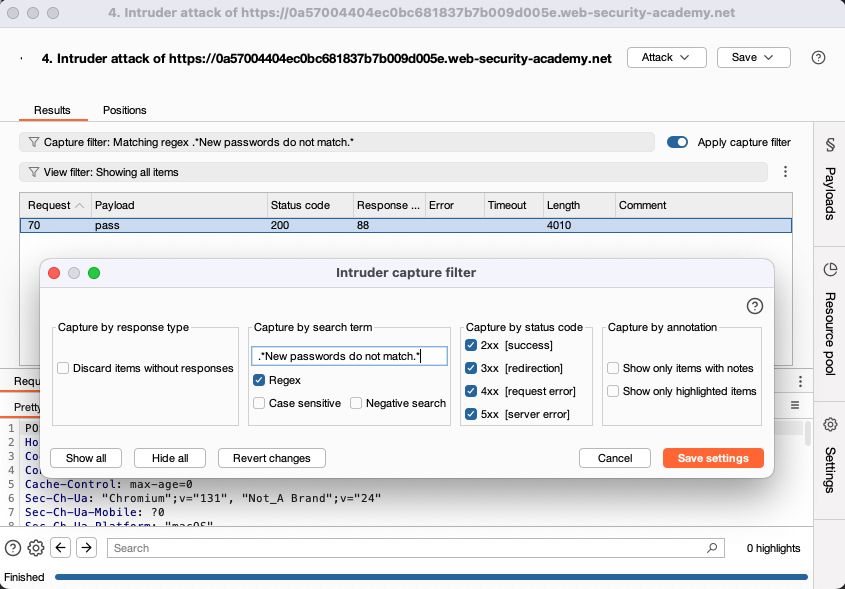
🤫 #sneakpeek #BurpSuite #Intruder