New users, on Signal, you can mute chats for a period or permanently. No notifications but you can still see if there are unread messages.
On desktop: in that chat, go to Group Settings, then Notifications. On iPhone: in that chat, click on the name at the top, then go to Sounds & Notifications.
30.03.2025 12:23
👍 65
🔁 13
💬 4
📌 1
"Life Safety building automation is pretty awesome. 👏"
30.03.2025 15:43
👍 3
🔁 0
💬 0
📌 0
MCP: The Differential for Modern APIs and Systems | 🤖
<div style={{
Excellent writeup on how MCP future-proofs API integrations ~ @stevemanuel.bsky.social
docs.mcp.run/blog/2025/03...
30.03.2025 10:57
👍 21
🔁 8
💬 1
📌 1

Our second keynote for Offensivecon 2025 will be Dino Dai Zovi! @ddz.bsky.social
25.03.2025 18:18
👍 9
🔁 3
💬 0
📌 1
I'll be doing a speaking!
30.03.2025 15:06
👍 9
🔁 2
💬 0
📌 0

Saw this on the other site but I should comment here:
Can't remember his hacker handle but I think Pad & Gandalf of 8lgm were arrested the same day in 1991.
You may not know it but the entire infosec & software industries owe 8lgm immense gratitude for making vendors accountable for their vulns
17.03.2025 22:59
👍 9
🔁 6
💬 0
📌 0
We are destroying software - <antirez>
We are destroying software: antirez.com/news/145
08.02.2025 14:48
👍 212
🔁 62
💬 17
📌 16
Exactly this. We should instead be investing that energy into making authentication in our environment unphishable by making it impossible to give away access to an attacker, even if someone actually wanted to.
08.02.2025 18:12
👍 5
🔁 1
💬 0
📌 0
I have never once run a phishing sim. I refuse to use the word. I put it in air quotes and say scam by text or email etc
Tech and cyber has been about deflecting blame to anyone else but themselves- which is what sims are. Blaming people when the system they use should protect against issues.
08.02.2025 07:21
👍 10
🔁 3
💬 2
📌 1

WhatsApp says it disrupted a hacking campaign targeting journalists with spyware | TechCrunch
The Meta-owned company said the campaign was linked to Israeli spyware maker Paragon.
NEW: WhatsApp says it has notified 90 victims, including journalists and members of civil society, that they were targeted with spyware made by Paragon.
This is the first time that Paragon is linked to alleged abuse of its products.
techcrunch.com/2025/01/31/w...
31.01.2025 15:16
👍 58
🔁 33
💬 1
📌 3

WhatsApp says journalists and civil society members were targets of Israeli spyware
Messaging app said it had ‘high confidence’ some users were targeted and ‘possibly compromised’ by Paragon Solutions spyware
Meta says almost 100 journalists and activists were targeted with spyware from Israeli company Paragon Solutions using a zero-click vuln in WhatsApp. If you use an iPhone, enabling Lockdown Mode prevents this from working. www.theguardian.com/technology/2...
31.01.2025 19:38
👍 186
🔁 132
💬 7
📌 7
👋
24.01.2025 00:29
👍 0
🔁 0
💬 0
📌 0
I'm really liking the crisp definitions of and boundaries between product engineering, domain engineering, and infra engineering in this.
How much of your security org builds "what any company would need" (infra) vs. "what is unique to this company but shared across the company" (domain) ?
19.01.2025 16:19
👍 11
🔁 1
💬 0
📌 0
There are different privacy concerns and approaches for the training phase of AI as well as for the inference phase of using it. It's a good time to be thinking about what the right approaches are for each.
18.01.2025 16:27
👍 3
🔁 0
💬 0
📌 0
+1, security product vendors, services companies, *and* internal teams must always operate under the Hippocratic Oath, "First, do no harm."
18.01.2025 16:17
👍 3
🔁 2
💬 1
📌 0

Data Safety Levels Framework: The foundation of how we look at data in Block
Block uses the Data Safety Levels (DSL) Framework to evaluate data sensitivity.
We blogged again! This time about our Data Safety Levels framework, which was inspired by the CDC/WHO Biosafety Levels system and Laboratory Biosafety Manuals. Like biological agents, we also don't want sensitive data to be exposed to humans or escape.
code.cash.app/dsl-framework
16.01.2025 22:00
👍 5
🔁 3
💬 0
📌 0
This is the way ;)
14.01.2025 02:09
👍 1
🔁 0
💬 0
📌 0
PRF in WebAuthN is going to enable epic things
11.01.2025 15:39
👍 12
🔁 0
💬 1
📌 0
Fraud is such a broad thing, hard to answer. But I think better forms of digital and cryptographic proofs of selective identity information would help. For example, cryptographic proof of personhood, while still remaining anonymous would help reduce amount of bots and such on social media.
10.01.2025 03:53
👍 3
🔁 1
💬 1
📌 0
That is true that it is not cool, but the shift to EMV also happened in the US with cardholders not being liable for fraudulent charges by law. I'm not sure what the laws were in AU, but wonder if that was only the situation in EU/UK?
10.01.2025 03:49
👍 0
🔁 0
💬 0
📌 0
Any plans on supporting Confidential VMs (e.g. AWS Nitro Enclave, AMD SEV-SNP, Intel TDX) w/ TamaGo unikernels?
06.01.2025 15:21
👍 0
🔁 0
💬 1
📌 0
The way that I think about it is that the systems that I think about the security of have grown larger and more complex. Being Security DRI for Square's EMV launch in 2014 was really educational. True to my roots, I found EMV smartcard parsing mem corruption bugs in our firmware before it shipped :)
01.01.2025 16:49
👍 4
🔁 1
💬 0
📌 0
Well, in the US, cardholders haven't been liable for fraudulent charges since 1974's Fair Credit Billing Act, which meant issuers owned fraud losses. This created the incentive for the EMV liability shift, which was created by contractual agreements between issuers, acquirers, terminal vendors, etc.
01.01.2025 16:39
👍 0
🔁 0
💬 1
📌 0
The placement of liability for fraudulent credit card charges onto the issuer incentivized the shift to EMV, so we now have smartcards in our wallets and secure elements on our smartphones.
Contrast this to the security of authn to way more critical things than buying a coffee.
01.01.2025 16:12
👍 9
🔁 1
💬 3
📌 1

Benchmarking RSA Key Generation
RSA key generation is conceptually simple, but extremely tricky. Even benchmarking involves math: we generated a stable but representative “average case” instead of using the ordinary statistical appr...
Ever wanted to benchmark RSA key generation but found it too slow and variable, like benchmarking a lottery? No? Just me?
Well, I nerd-sniped myself into producing average representative inputs that can be used to benchmark, profile, and compare RSA keygen. c2sp.org/CCTV/keygen
Happy New Year(?)!
31.12.2024 14:19
👍 66
🔁 13
💬 2
📌 0
This Salt Typhoon stuff is insane. The entire FISA surveillance infrastructure has been completely owned by China and literally no part of our telecom infrastructure is safe to use without end-to-end encryption.
29.12.2024 09:50
👍 897
🔁 326
💬 28
📌 28
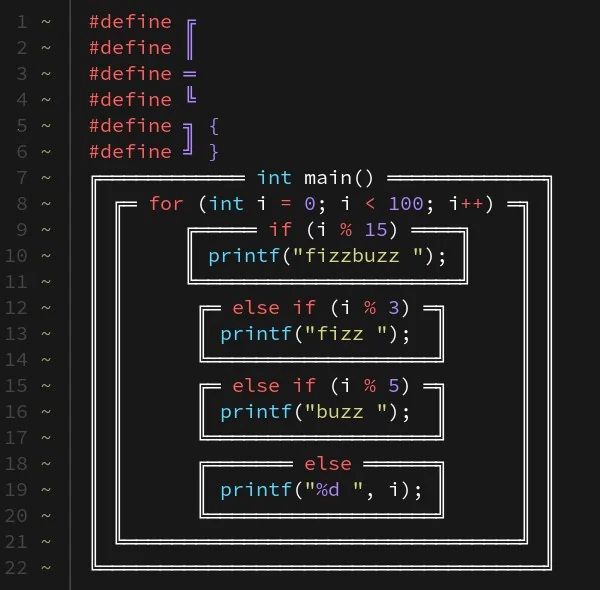
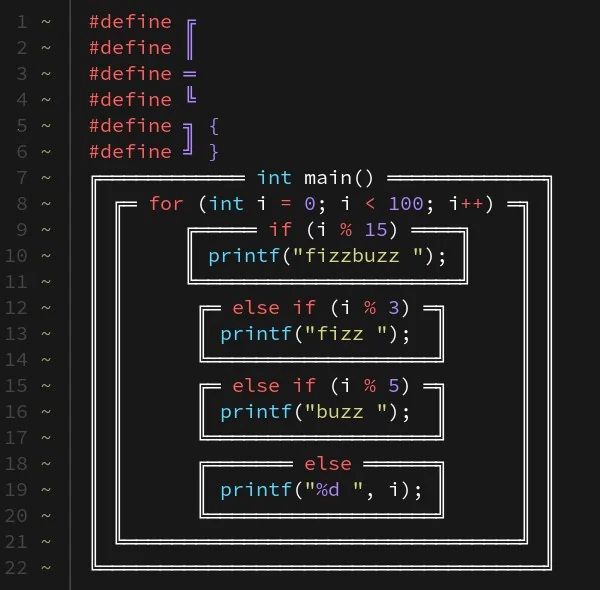
Code written with box characters used on old old software to make fake UIs
You’re still arguing about tabs vs. spaces? May I present…
25.12.2024 18:37
👍 5304
🔁 1284
💬 157
📌 147