GitHub - 0x4D31/finch: Fingerprint-aware TLS reverse proxy. Use Finch to outsmart bad traffic—collect client fingerprints (JA3, JA4 +QUIC, JA4H, HTTP/2) and act on them: block, reroute, tarpit, or dec...
Fingerprint-aware TLS reverse proxy. Use Finch to outsmart bad traffic—collect client fingerprints (JA3, JA4 +QUIC, JA4H, HTTP/2) and act on them: block, reroute, tarpit, or deceive in real time. -...
Finch v0.1.0 is live! ✨
excited to open-source another pet project: a fingerprint-aware TLS reverse proxy. use Finch to collect client fingerprints and act on them: block, reroute, tarpit, or deceive in real time!
go break it & report bugs! github.com/0x4D31/finch
28.07.2025 15:06
👍 3
🔁 0
💬 0
📌 0
haha 🤷♂️ give oai o3 and o3-pro a try if you haven’t. at least they can reason better than half the people i’ve worked with.
20.06.2025 12:17
👍 0
🔁 0
💬 1
📌 0
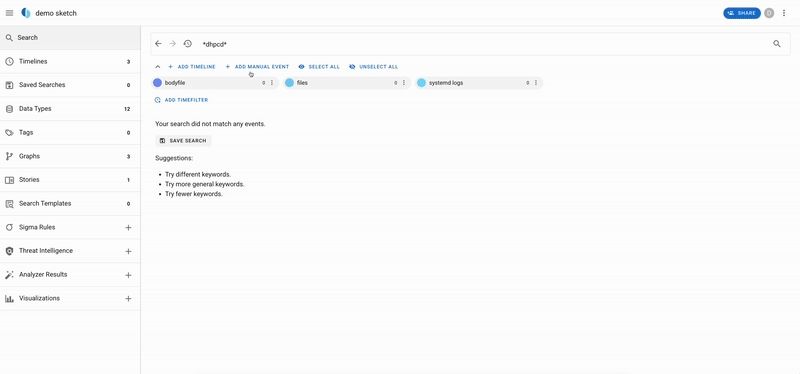
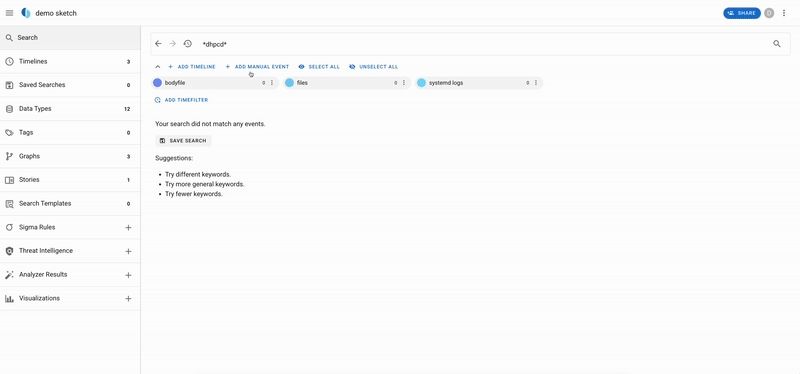
Using Timesketch for timeline analysis? We recently added a new feature: LLM summaries of up to 500 events in view. Example below uses Gemini Flash, but you can just as easily use a local Ollama model. Setup guide: timesketch.org/guides/user/...
19.06.2025 18:01
👍 6
🔁 4
💬 0
📌 1

dig @.lmctfy -p 5353 -y hmac-sha256:mykey:SGVsbG8h "whats-the-meaning-of-life" TXT
spent an afternoon over the holidays on a mini project, but it’s so silly i’m not sure it’s worth sharing. who else, besides me, would use `dig` and `ssh` to interact with an llm?
🤪 llm over dns—maybe to brainstorm with chatgpt during a long flight without paying for inflight internet!?
15.01.2025 11:50
👍 0
🔁 0
💬 0
📌 0

My latest work has been published:
"CTU Hornet 65 Niner: A network dataset of geographically distributed low-interaction honeypots"
The dataset has a unique value for studying the nature of Internet attacks over time and their changes and characteristics.
www.sciencedirect.com/science/arti...
13.01.2025 10:26
👍 12
🔁 8
💬 0
📌 0
I'm watching some folks reverse engineer the xz backdoor, sharing some *preliminary* analysis with permission.
The hooked RSA_public_decrypt verifies a signature on the server's host key by a fixed Ed448 key, and then passes a payload to system().
It's RCE, not auth bypass, and gated/unreplayable.
30.03.2024 17:13
👍 687
🔁 275
💬 7
📌 13
hello @bsky.app!
i hate the app icon and splash screen.
05.11.2023 23:03
👍 2
🔁 0
💬 0
📌 0