
I don’t think I’ll ever get tired of the sunsets in the Philippines

I don’t think I’ll ever get tired of the sunsets in the Philippines

Threats is a very serious book with a silly coat of paint on it. Some folks seem to judge books by their cover. But, for a very limited time, you can get the book for free, and judge it on the content. If you’ve been waiting, there’s now no risk.
www.neowin.net/sponsored/th...

Think I’ll be having a play with this today and see what detection opportunities are in there #linux #ttp #detectionengineering github.com/Aegrah/PANIX...
There was sensitive media stored in the account so having a way to know if they pulled it down or not might save her worrying too much.
So it looks like it was successful. Does anyone know if there is any route to requesting what activity occurred even if its a long process? We think it was approx. 1-2 mins afterward that she logged in and rolled creds.
The Attemped auth looks to be from a sketchy hosting provider. I'd like to give her some reassurance if possible. The creds were reset very quickly. And I know Snapchat does some auth analytics as I've failed auth with unusual country/
device in the past. I'm desperately hoping it was a failed auth.
I've done all the usual (confirmed she reset with a strong, unique pass, enabled 2FA, checked with her that the phished creds weren't reused elsewhere). The Snapchat Sessions page only shows her current session with valid IP.
Do any of my followers have any contacts at Snapchat? A close friend has been phished but realised a couple of mins later and reset her creds. The email she has received afterwards isn't clear if the attempted auth was successful or not. She is fraught with worry. Please repost for visibility.
@markrussinovich.bsky.social Thanks for posting this as it’s given me a project to have a go at! Been looking for a reason to have a play with LLMs :)
Taking it a step further, an LLM that could take a bunch of logs, take a draft detection in the prompt, show alerts that would trigger and then spit out out suggested recommended tuning for the detection would be really interesting too.
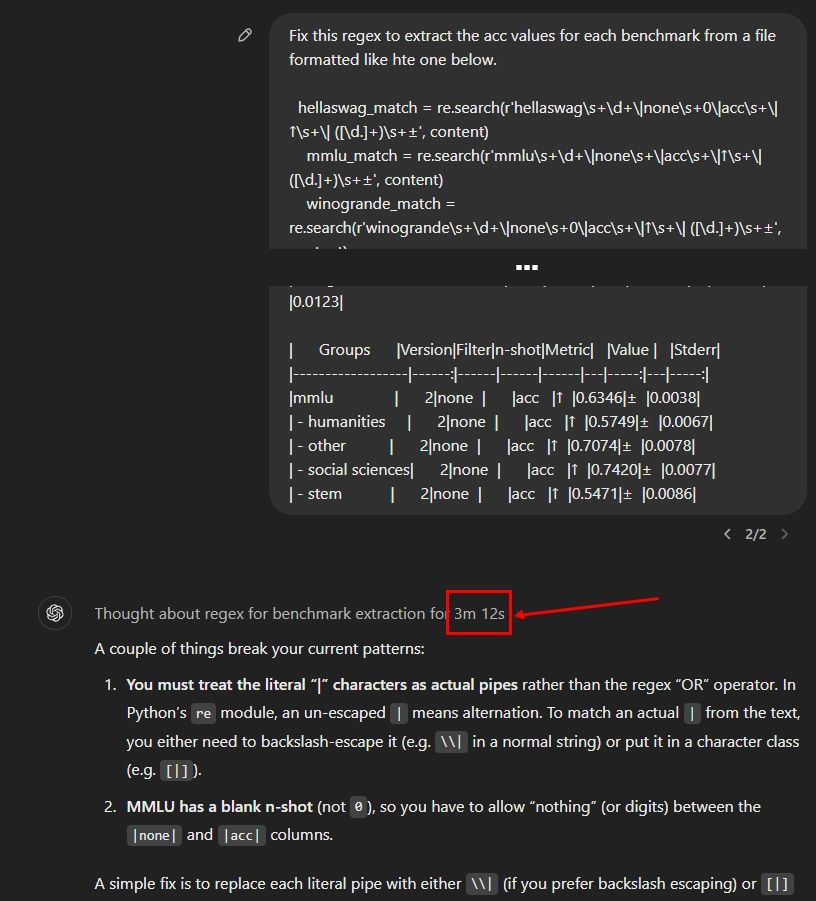
Regex is too hard for even OpenAI o1: it thought for over three minutes and then produced regex that didn't work. Looks like regex is a good test for AGI.
Maybe an LLM specifically trained on regex would be an interesting project. Who wouldn’t like an LLM to take a sample of logs and spit out an efficient and effective regex ;)
I decided to put together a starter pack of oldskool hacker and/or hacker-adjacent folks you may want to follow (Or, y'know, maybe you want to block them all, what do I know? You do you, homeslice.)
go.bsky.app/HQWqtno
Magical. Out of interest, which Leica?
Hope to see some of you tonight for discussions
I actually lol’d when they didn’t pick up on any of them. Obviously not a hacker haha.
Nice touch with the Hackers references :D

This blog is wild. “Secret Blizzard (Turla) has used the tools and infrastructure of at least 6 other threat actors during the past 7 years.”
www.microsoft.com/en-us/securi...

Sekoia has published some pretty comprehensive research on how ransomware gangs exfiltrate data from compromised environments.
blog.sekoia.io/ransomware-d...

DualCore and I spoke at the Red Team Village this year. Here are the slides. QR code with link to gist with all the reference links on last page. Unfortunately it wasn't recorded.
docs.google.com/presentation...
#redteam #purpleteam #redteamvillage

If you'll be at BSides London this year please do find the time to check out this talk by my student Ana, she's going to be talking about the intersection of security and disability with her talk on password accessibility
After that I’d add the collection of some specific Events for Windows eg. User added to Security-Enabled Group and PowerShell logs.
Please don’t do what I see so often and focus on collecting firewall events.
For anyone just getting into detection engineering or hunting, I’d strongly recommend starting out by making sure you’re collecting process events (with full command lines), persistence locations (eg. scheduled tasks, services, reg run keys, cron, etc) and process network connections.
Just added a boatload of new detection engineers who joined Bluesky this week. Make sure to check this starter pack out

If you're interested in Linux DFIR? Then check all our talks/workshops below. #Linux #DFIR #Cybersecurity
CC: @maryst33d.bsky.social
linuxdfir.ashemery.com

We have just managed to free up some more tickets for #BSidesLDN2024, when they are gone, they are gone!
www.eventbrite.co.uk/e/bsides-lon...
Please be a team player and remember to cancel your ticket if you can no longer be there on the day!
#Security #BSides #London #Tickets
Whilst helping someone out with their gmail security, I’ve just realised they offer darkweb/leak monitoring. How did I not know about this already?
🧵5/5 ..FCUK ransomware. And FCUK this group in particular. I’ll be tracking their TTPs and building detections ESPECIALLY FOR THIS GROUP at every opportunity.
Ps. when I say fairly sophisticated, I mean as far as ransomware groups go