
🚢 🏴☠️ YO HO! We've awoken from our slumber, and set sail for @codeblue and @tengusec in Tokyo next week!
Join us alongside @villageb.io @aerospacevillage.bsky.social CHV and ICSV!
#villages #hacking #codeblue #tengusec #maritimesecurity #ctf

🚢 🏴☠️ YO HO! We've awoken from our slumber, and set sail for @codeblue and @tengusec in Tokyo next week!
Join us alongside @villageb.io @aerospacevillage.bsky.social CHV and ICSV!
#villages #hacking #codeblue #tengusec #maritimesecurity #ctf




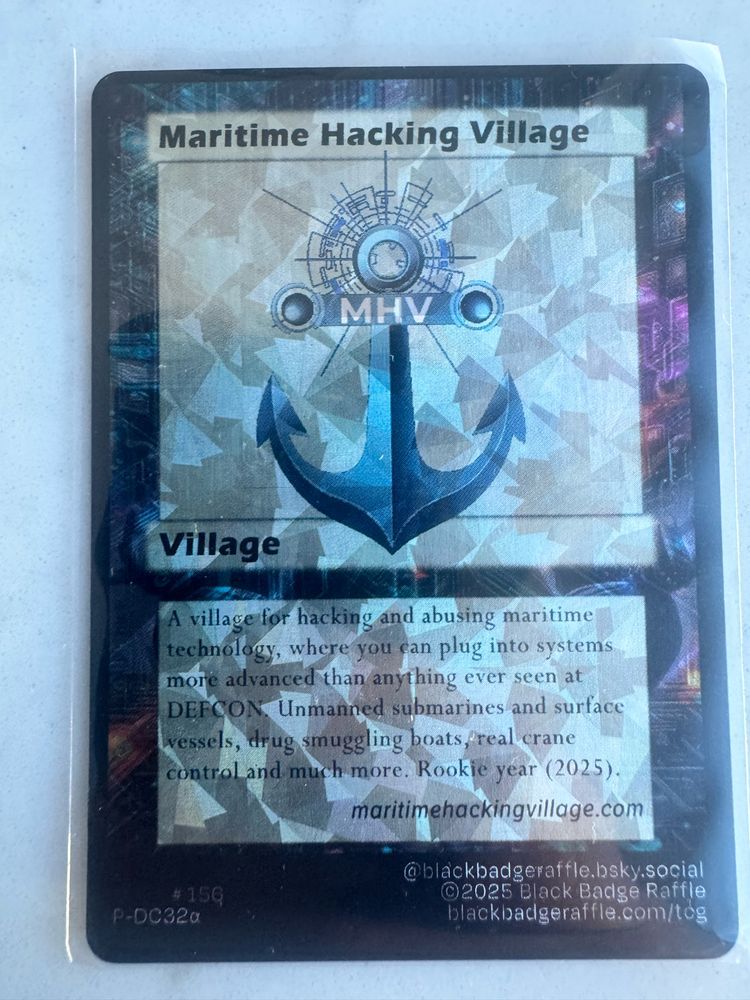
THANK YOU TO OUR SPONSORS! Our first year at Def Con as the Maritime Hacking Village was a HUGE success!
Thank you to ABS Group, Anduril and Dispel, HavocAI, Port of Long Beach, Liberas, MCSI, Splash Robotics, RunSafe Security, OneZero, and Gary Kessler Associates!
#DEFCON #DC33 #MHV

🏴☠️☠️ The crew that made it happen! 🏴☠️☠️
Huge thanks to the Maritime Hacking Village volunteers at DEF CON 33 — from running CTFs and demos to keeping our ship afloat, you made it a success.
Your passion and skill keep the maritime security community thriving. ⚓
#DEFCON33 #MHV @defcon.bsky.social




Day 3 Recap — MHV @defcon@defcon.social 33
MHV’s maiden voyage is complete! 3 teams of pirate warriors liberated Isla Hexa in our CTF. 7 hacked the real crane system! HavocAI is undefeated.
Thank you all for a huge success! Fair winds and following seas!
#DEFCON33 #MHV @defcon.bsky.social


FINAL HOUR! Today has been incredible! CTF area is FULL and 7 teams have hacked the crane control system! Huge success! @DEFCON #DEFCON #DC33 #MHV #DEFCONContests

🚢 Dead Reckoning: Hijacking Marine Autopilots
Sunday 12:30 PM | Room 229
Carson Green & Rik Chatterjee show how SD cards & NMEA2000 can let attackers hijack autopilots—no physical access needed.
Firmware hacks + live demo = ⚓️ wake-up call!
#DEFCONSpeakers #DEFCONCreators @defcon.bsky.social




Scenes from Day 2 at MHV: CTF teams in action, workshops in full swing, and hands-on testing on the boat and container systems. Strong engagement across the board — one day left.
#DEFCON33 #MHV #CTF #MaritimeSecurity #DEFCONVillages @defcon.bsky.social



🏴☠️ Congrats to our Container Challenge CTF champs! 🏴☠️
Enzo “Paniq” Genovese & Spencer Beer conquered codes, puzzles & the Digital Blockade at MHV during DEF CON 33. ⚓💻
#DEFCON33 #MHV #CTF #MaritimeSecurity #DEFCONVillages @defcon.bsky.social
Navigating the Invisible
Learn how to use AIS data, port logs & social media to build threat models—no packets needed, just OSINT.
🕒 16:30 | Creator Stage 3 (Room 231)
#MaritimeOSINT #CyberThreatIntel #DEFCON33 #DEFCONSpeakers #DEFCONCreators @defcon@defcon.social

🛰️⚡ The lights are going out. Can you stop it?
Face off in a 30-min cyber wargame to defend Taiwan’s infrastructure from sabotage and electronic warfare. No experience needed.
🎲 Dice, strategy, and real-world scenarios.
🕒 16:30 | MHV Booth (W2-504) Workshop Area
#CyberWarfare @defcon.bsky.social
🛰️ From drones to underwater nets, maritime comms are evolving—so are the threats.
At 16:30, AviNash Srinivasan & Brien Croteau present a resilient SDN-SDR SATCOM framework for secure ops.
🕒 16:30 | Creator Stage 4 (Room 228)
#DEFCON33 #DEFCONSpeakers #DEFCONCreators @defcon@defcon.social

📡 What can OSINT reveal about maritime cybersecurity? A lot.
At 16:00, Vlatko Kosturjak & MJ Casado walk through passive scans of 50 top orgs using LLMs, DNS, and email signals.
🕓 16:00 | Room 232
#MaritimeOSINT #CyberRecon #DEFCON33 #DEFCONSpeakers #DEFCONCreators @defcon@defcon.social

🛠️ What happens when attackers nudge your ship’s sensors?
Dean Macris & Anissa Elias use custom hardware to fingerprint maritime OT and test NMEA2000 attacks with custom hardware.
🕓 16:00 | Creator Stage 1 (Room 233)
#NMEA2000 #DEFCON33 #DEFCONSpeakers #DEFCONCreators @defcon.bsky.social
🚢 Most ship simulators weren’t built for cyber. What if we could turn them into training grounds?
At 15:30, Jeff Greer & Dr. Laavanya Rachakonda demo how to transform simulators into cyber ranges.
🕒 15:30 | Creator Stage 2 (Room 232)
#DEFCON33 #CyberTraining #DEFCONSpeakers #DEFCONCreators

🏴☠️ Red Team on a cruise ship?
John Andre Bjørkhaug shows how hackers boarded real vessels, bypassed controls, and took over comms & nav systems.
🕒 15:00PM | Creator Stage 1 (Room 233)
#DEFCON33 #RedTeam #MaritimeHacking #PirateOps #DEFCONSpeakers #DEFCONCreators @defcon.bsky.social
What’s “normal” on a ship’s CAN bus?
Dive into NMEA2000 network behavior with live sensor fingerprints, attack simulations, and a dataset you’ll wish existed sooner. Stop on by!
🕒 15:00 | MHV Booth (W2-504) Workshop Area
#DEFCON33 #NMEA2000 #OTsecurity #MaritimeHackingVillage @defcon.bsky.social

The CGAUX boat is a HIT! And the pirate crew is hard at work hacking the HavocAI autonomous watercraft!
#DEFCON #DC33 #MHV
⚙️ Hack your own boat.
Alex Lorman dives into hacking outboards, steering systems, and the stubborn black boxes of marine propulsion.
🕝 14:30PM | Creator Stage 4 (Room 228)
#DEFCON33 #ReverseEngineering #MarineHacking #AutonomousBoats #DEFCONSpeakers #DEFCONCreators @defcon.bsky.social

New to PLCs? No problem.
In just 1 hour, you’ll program a real Allen Bradley Micro820 with Rockwell tools and learn the logic behind industrial control systems.
🕒 13:30 | MHV Booth (W2-504) Workshop Area
#DEFCON33 #PLChacking #ICSsecurity #MaritimeHackingVillage @defcon.bsky.social
🛰️ Backdoors on the high seas.
Juwon Cho reveals real VSAT exploits, testbed demos, and live CVEs. From firmware to fail states, this talk hits hard.
🕧 12:30PM | Creator Stage 4 (Room 228)
#DEFCON33 #VSAT #MaritimeCyber #SatelliteHacking #DEFCONSpeakers #DEFCONCreators @defcon.bsky.social

🚨 WARGAME PREMIERE!
CYBERCLAW or CYBERsecurity Card-based Learning And Wargaming
Join the premiere of CYBERCLAW, a new undersea cyber warfare game. Strategy, sabotage, and a dash of saltwater.
🕒 12:00 | MHV Booth (W2-504) Workshop Area
#DEFCON33 #Wargaming #Maritime @defcon.bsky.social

From port outages to cyber flare-ups at sea—what really happens when a ship or harbor goes dark?
Capt. Kit Louttit and Steve Winston break down real-world incident response from both the bridge and the basement.
🕦 11:30AM | Stage 4 (Room 228)
#DEFCONSpeakers #DEFCONCreators @defcon.bsky.social

Can you keep Taiwan’s power and data flowing? A 30-minute attacker-defender wargame straight from Naval War College playbooks is coming your way at 10:30 this morning.
Join us for Taiwan Digital Blockade Lite: Wargame!
#DEFCON33 #Maritime #Taiwan @defcon.bsky.social

Ahoy! MHV CTF 101 starts in just 30min.
Gear up for Isla Hexa: AI boats, smuggler ops, and real-world maritime tech in the most ambitious CTF on the floor.
🕒 10:30 | MHV Booth (W2-504) Workshop Area
#DEFCON33 #Maritime @defcon.bsky.social

When software fails at sea, people can die.
Join Michael DeVolld and Austin Reid as they dissect real-world failures in military and maritime systems, from Smart Ship crashes to firmware flaws.
🕥 10:30AM | Room 231
#DEFCON33 #MaritimeCyber #SoftwareSafety
We're 30 minutes away from the first workshop of the day! MHV Overview 101
Get briefed on the most advanced maritime hacking setup ever seen at DEF CON. We have unmanned vessels, crane systems, and cyber-physical targets awaiting you.
🕒 10:00 | MHV Booth (W2-504) Workshop Area
@defcon.bsky.social

MHV CTF is popping off - our CTF area is FULL! 25+ teams competing in DIGITAL BLOCKADE. @defcon #DEFCON #DC33

Think you know how to steer a ship or hack one?
At sea, turning left can get you sued... or sunk.
Join us for a crash course in COLREGs, rudder hacks, and why “Don’t Turn to Port” isn’t just a sailor’s superstition.
🕒 17:30PM | Room 229
#DEFCONSpeakers #DEFCONCreators @defcon.bsky.social


No one has completed the container challenge or pwned our boat yet! Come perform a felony of maritime grand theft auto and try your hand at hacking a real world crane control system!
#DEFCON #DC33 #MHV #DEFCONCTF @defcon.bsky.social



DAY 1 DEFCON 33 is a massive success!
The maritime hacking village has been on fire and getting a huge amount of traffic. Come hack our two autonomous boats by HavocAI and Splash Industries, hack our sophia console by Penn State Applied Research Labs, and engage in our maritime CTF!
#DEFCONCTF