"Where is she!??!!??" Wait a minute, that's Batman. This is Liam Neeson.
February 2026 #TrafficAnalysisExercise
You get a pcap, you find your kidnapped daughter--I mean, you find the infected Windows host!
Join the fun at www.malware-traffic-analysis.net/2026/02/28/i...
01.03.2026 02:04
👍 1
🔁 0
💬 0
📌 0

Screenshot of my blog post with the files and information from this infection.

Screenshot of the email with an attached RAR archive.

The malware, extracted from the attached RAR archive.

Traffic from the infection filtered in Wireshark.
2026-02-03 (Tuesday): #GuLoader for #AgentTesla style malware with FTP data exfiltration. A #pcap of the infection traffic, associated files, and a list of indicators are available at www.malware-traffic-analysis.net/2026/02/03/i...
03.02.2026 18:39
👍 4
🔁 2
💬 0
📌 0

Fake "Verify You Are Human" CAPTCHA page that can appear when viewing a page from a legitimate but compromised website.

Text from KongTuke's fake CAPTCHA page injected into the viewer's clipboard, and the CAPTCHA page contains instructions to run the text as a command in Window's Run window.

Traffic from the KongTuke activity and resulting infection filtered in Wireshark.
Reposted with correct malware names:
2026-02-02 (Monday) #KongTuke #ClickFix activity leads to #MintsLoader and #GhostWeaver RAT
Today's ClickFix uses the "finger" command, a tactic seen in previous ClickFix activity.
Further details available at www.malware-traffic-analysis.net/2026/02/02/i...
03.02.2026 03:25
👍 6
🔁 3
💬 1
📌 0

Screenshot showing Google search results for a cracked version of ArcGIS where I specify site:drive.google.com. The results shown here all lead to PDF files hosted on Google Drive, and these PDF files contains links that lead to malware.

Here's an example of one of these PDF files hosted on Google Drive with a link that leads to malware.

Here's the page that pushes a password-protected 7-zip archive that contains an inflated EXE padded with null bytes. This EXE is for Lumma Stealer malware.

Lumma Stealer traffic generated by the extracted malware. This is filtered in Wireshark to focus on the Lumma Stealer C2 traffic.
2026-02-01 (Sunday): It's easy enough to find #LummaStealer malware samples.
Just do a Google search for cracked versions of popular software and specify site:drive.google.com.
Details on today's haul at github.com/malware-traf...
02.02.2026 03:46
👍 4
🔁 2
💬 0
📌 0

2026-01-31 (Friday): I've posted a new traffic analysis exercise. It's Lumma in the room-ah! Join the fun at www.malware-traffic-analysis.net/2026/01/31/i...
I mean, this guy looks like he's having fun.
31.01.2026 05:58
👍 4
🔁 2
💬 0
📌 0

Screenshot from an infected Windows host showing Remcos RAT and how it is persistent.
2026-01-22 (Thursday): #RemcosRAT infection persistent on an infected Windows host. This was caused by #ClickFix instructions from #SmartApeSG through a fake CAPTCHA page. Details of this #Remcos #RAT infection are available at www.malware-traffic-analysis.net/2026/01/06/i...
29.01.2026 02:36
👍 3
🔁 2
💬 0
📌 0

2026-01-19 (Monday): Catching up on two infections in my lab from last week, and I added an entry with a #pcap of scans and probes and web traffic hitting my web server. Feel free to check out my latest posts at www.malware-traffic-analysis.net/2026/index.h...
Or not. I'm not the boss of you.
20.01.2026 03:41
👍 5
🔁 1
💬 1
📌 0

ISC Logo
ISC Diary: Infection repeatedly adds scheduled tasks & increases traffic to same C2 domain https://isc.sans.edu/diary/32628
14.01.2026 18:21
👍 3
🔁 2
💬 0
📌 0

Some of the scans, probes, and web traffic from the pcap filtered in Wireshark.
![HTTP stream of the last HTTP request in the pcap showing a POST request that retrieves malicious content from a server at 91.92.241[.]10.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreifbztcodx2egdob5q7qeavrl37vol6y4ccid2oxb2la2m3u2hd6b4@jpeg)
HTTP stream of the last HTTP request in the pcap showing a POST request that retrieves malicious content from a server at 91.92.241[.]10.
![Using the wget command to retrieve one of the malicious files from the server at 91.92.241[.]10 on Sunday, 2026-01-11.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreie4mnwflndg2wx3wus6vluilyqceqbg3emwi7k5ybw44uuzmp3pei@jpeg)
Using the wget command to retrieve one of the malicious files from the server at 91.92.241[.]10 on Sunday, 2026-01-11.
![Example of a shell script downloaded from 91.92.241[.]10 on Sunday, 2026-01-11, likely for Mirai botnet malware.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreifuapqt3w53o5vbkuyxkri6tsnyvthsrxxwu4hybekm5e2qnxcttu@jpeg)
Example of a shell script downloaded from 91.92.241[.]10 on Sunday, 2026-01-11, likely for Mirai botnet malware.
2026-01-10 (Saturday): Ten days of scans, probes, and web traffic hitting my web server. A #pcap of the traffic is available at www.malware-traffic-analysis.net/2026/01/10/i...
11.01.2026 17:10
👍 3
🔁 0
💬 0
📌 0

Screenshot of the email, its attachment, and the VBS file within the attachment for VIP Recovery malware.

Traffic from the infection filtered in Wireshark.

TCP stream of the unencrypted SMTP traffic from one of the data exfiltration emails sent by my infected lab host.

Screenshot of the start of my blog post with information on this VIP Recovery infection.
2026-01-09 (Friday): #VIPRecovery infection from an email attachment. A #pcap of the infection traffic, associated files, and more information are available at www.malware-traffic-analysis.net/2026/01/09/i...
09.01.2026 21:48
👍 5
🔁 0
💬 0
📌 0

Fake CAPTCHA window and ClickFix script after visiting legitimate, but compromised website.

Traffic from the infection filtered in Wireshark (part 1 of 2).

Traffic from the infection filtered in Wireshark (part 2 of 2).

Screenshot from the start of the page for this blog post.
2026-01-08 (Thursday): Got a full infection from #KongTuke campaign #ClickFix activity today. Traffic from the infection in two #pcap files, the associated malware, artifacts, and further information is available at www.malware-traffic-analysis.net/2026/01/08/i...
08.01.2026 20:52
👍 3
🔁 0
💬 0
📌 0

One of the emails and its associated attachment for MassLogger malware.

Traffic from the infection filtered in Wireshark.

Example of a data exfiltration email sent from an infected host in my lab.
2026-01-07 (Wednesday): #MassLogger infection from email attachment. Copies of the emails, associated malware, indicators, and a #pcap of the infection traffic are available at www.malware-traffic-analysis.net/2026/01/07/i...
08.01.2026 01:48
👍 3
🔁 1
💬 0
📌 0

Example of a legitimate but compromised site showing the SmartApeSG fake CAPTCHA page.

HTTPS URLs from the infection run.

Traffic from an infection filtered in Wireshark.

Remcos RAT infection persistent on an infected Windows host.
2026-01-06 (Tuesday): #SmartApeSG CAPTCHA page uses #ClickFix technique to push #RemcosRAT, with #Remcos #RAT C2 server at 192.144.56[.]80. A #pcap of the traffic, the Remcos RAT #malware, and a list of indicators are available at www.malware-traffic-analysis.net/2026/01/06/i...
06.01.2026 18:04
👍 6
🔁 2
💬 0
📌 0

Injected KongTuke script in page from compromised website.
![Fake CAPTCHA page from KongTuke domain, scrroeder[.]com.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreielwil5fxjm3tv2gkrdwcv4airp2xlmojctkj7wjgyzh7ogo7bfzu@jpeg)
Fake CAPTCHA page from KongTuke domain, scrroeder[.]com.

KongTuke's "ClickFix" command injected into the viewer's clipboard.

Traffic from the activity filtered in Wireshark. I did not get the malware from this.
2026-01-05 (Monday): #KongTuke domain scrroeder[.]com generated #ClickFix script for 144.31.221[.]71, but I didn't get a malware infection when I tried it today.
05.01.2026 16:50
👍 7
🔁 1
💬 0
📌 0

ISC Logo
ISC Diary: Cryptocurrency Scam Emails and Web Pages As We Enter 2026 https://isc.sans.edu/diary/32594
04.01.2026 05:25
👍 2
🔁 2
💬 0
📌 0

A screenshot of my blog post for the Lumma Stealer infection

Traffic from the Lumma Stealer infection filtered in Wireshark.
2026-01-01 (Thursday): #LummaStealer infection with follow-up malware. A #pcap of the infection traffic, the #Lumma #Stealer files, and a list of IOCs are available at www.malware-traffic-analysis.net/2026/01/01/i...
01.01.2026 21:43
👍 3
🔁 1
💬 0
📌 0

Screenshot of my blog post to share information on this Lumma Stealer infection with follow-up malware.
2025-12-30 (Tuesday): #LummaStealer infection with follow-up malware. A #pcap of the infection traffic, the associated #Lumma with follow-up #malware samples, and some IOCs are available at www.malware-traffic-analysis.net/2025/12/30/i...
31.12.2025 05:37
👍 7
🔁 3
💬 0
📌 0
![Example of initial URL from sites.google[.]com.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreibriehckfna3yrmrvecncgppyh5rijr22fgs3pd2duuc6kc6art3i@jpeg)
Example of initial URL from sites.google[.]com.

Example of a fake CAPTCHA page with ClickFix-style instructions and the ClickFix script.

Traffic from the infection filtered in Wireshark.

NetSupport RAT persistent on an infected Windows host.
2025-12-29 (Monday): #ClickFix page leads to #NetSupportRAT infection.
Details at www.malware-traffic-analysis.net/2025/12/29/i...
29.12.2025 22:41
👍 1
🔁 1
💬 0
📌 0
Lol, I originally meant to say "defang." Several hundred pages without any [.] in the IP addresses and domains or hxxp/hxxps in the URLs. Looking back on it, I marvel that Google didn't flag my site earlier.
29.12.2025 21:26
👍 1
🔁 0
💬 0
📌 0
Just realized this came out as "deindex" which should've been "fix years of" old web pages on my blog and fix the sitemap, which was cleared a few years back, so it was missing a good amount of pages.
27.12.2025 02:26
👍 2
🔁 0
💬 2
📌 0

Downloading the initial file, a DMG image.

Screenshot showing the malicious downloaded DMG image and the associated malicious Mach-O file within the installer.app content.

Traffic generated by the MacSync Stealer malware, filtered in Wireshark.

Example of the data exfiltrated through the MacSync Stealer C2 traffic.
2025-12-23 (Tuesday): Based on yesterday's Jamf article, I ran the fake installer for #MacSyncStealer in my lab on a macOS host. A #pcap of the #MacSync #Stealer traffic, the associated IOCs, the #malware sample, and a link to the Jamf article are at www.malware-traffic-analysis.net/2025/12/23/i...
23.12.2025 18:39
👍 3
🔁 0
💬 0
📌 0

Screenshot of the post with the pcaps, files, and other info from the Kongtuke ClickFix activity using the finger command on 2025-12-11.
I finished compiling the information for #Kongtuke #ClickFix activity using the finger command on 2025-12-11, and it's now live at www.malware-traffic-analysis.net/2025/12/11/i...
I'd already posted the #SmartApeSG ClickFix activity using finger that same day, so now both are available.
23.12.2025 02:33
👍 4
🔁 1
💬 0
📌 0

Screenshot showing links for the three December 2025 blog posts I have so far.
I recently completed a long-term project to deindex old web pages on my blog, and I can now turn my attention back to sharing pcaps and malware samples.
I've posted 3 for December 2025, and I hope to get some more posted before the end of the year.
www.malware-traffic-analysis.net/2025/index.h...
22.12.2025 06:09
👍 13
🔁 4
💬 1
📌 0

ISC Logo
ISC diary: #SmartApeSG campaign uses #ClickFix page to push #NetSupportRAT https://isc.sans.edu/diary/32474
12.11.2025 21:51
👍 3
🔁 2
💬 0
📌 0
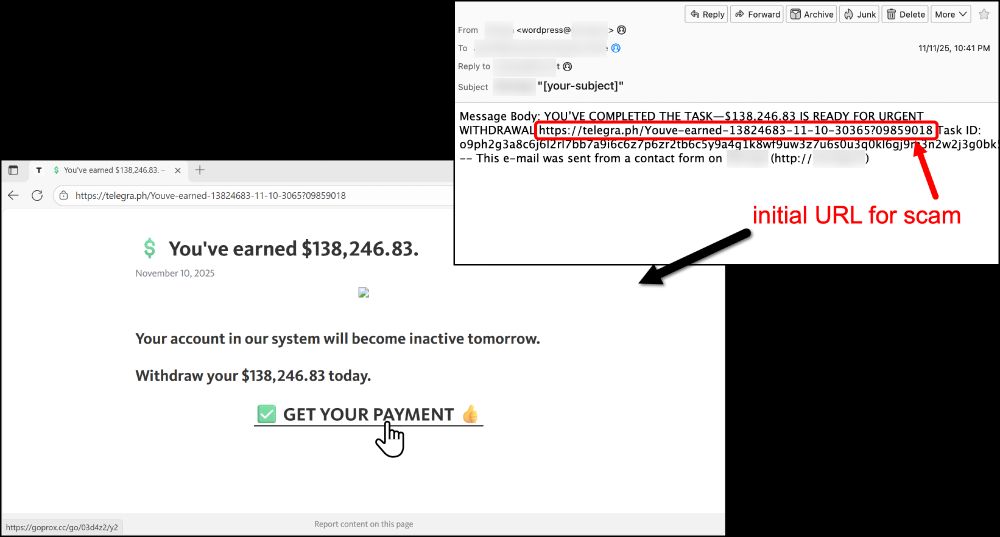
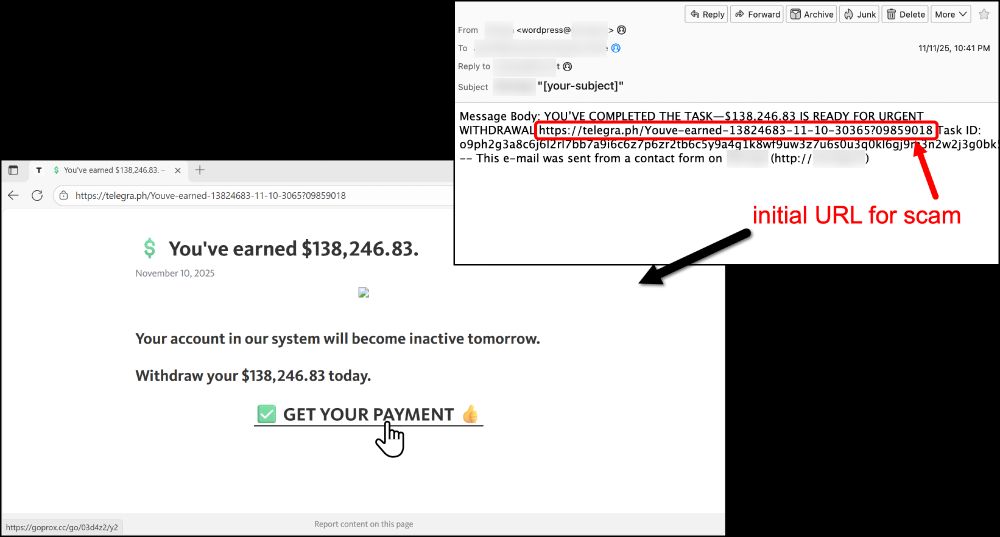
The scam starts with an email that links to a suspicious web page. I've somehow earned $138,246.83 USD... Let's go down this rabbit hole!

Hey, these pages say I already have an account, but I've not been on it for 364 days... Those fools! I'd better click my way through this.

Wow, an account I didn't even know I had! I just want my money. Better keep on clicking!

A progress bar? What the what??? This made me wait several minutes before I could continue. See the video at https://youtu.be/yUV7OkQqSBk for what happened after.
2025-11-11 (Tuesday): Cryptocurrency #scam starts with an email. Potential victims must click through several web pages to finish the process. I recorded a video showing what I did after the last image in this post at youtu.be/yUV7OkQqSBk
More info on this activity at github.com/PaloAltoNetw...
12.11.2025 04:00
👍 3
🔁 1
💬 1
📌 0

Page to download the initial file.

HTTPS URLs seen from the infection.

Traffic from the infection filtered in Wireshark.

Example of post-infection data exfiltration traffic.
2025-10-16 (Thursday): Unidentified #stealer/#Loader found when searching for URLs that follow patterns previously seen for Koi Loader/Koi Stealer.
Details at github.com/malware-traf...
16.10.2025 17:18
👍 1
🔁 1
💬 0
📌 0

Malicious Windows shortcut (LNK) files on the WebDAV server. Both are the same file with different names.

Traffic from the initial infection filtered in Wireshark.

Malware that was persistent on the infected Windows host.

Post-infection traffic generated by the peristent malware.
2025-10-10 (Friday): Was looking for Koi Loader/Koi Stealer, and I found this #WebDAV server that hosted malicious Windows shortcut (#LNK) files.
Not sure what type of #malware this is, but it's not Koi Stealer.
Details at github.com/malware-traf...
11.10.2025 01:16
👍 4
🔁 2
💬 1
📌 0

Traffic from the infection filtered in Wireshark.

Page from a compromised site with injected Kongtuke script.

Fake CAPTCHA page, courtesy of the Kongtuke campaign.

Following instructions from the Kongtuke campaign's fake CAPTCHA page.
2025-10-08 (Wednesday): #Kongtuke campaign fake CAPTCHA page with #ClickFix instructions. Got a full infection chain, this time. A 205MB zip download makes the #pcap take a while to load in Wireshark. Some IOCs and associated malware/artifacts at www.malware-traffic-analysis.net/2025/10/08/i...
09.10.2025 04:48
👍 3
🔁 1
💬 0
📌 0

Screen shot of the blog post.
2025-10-06 (Monday): A collection of 200+ phishing emails in Japanese that were sent to my blog email addresses. Available at www.malware-traffic-analysis.net/2025/10/06/i...
07.10.2025 03:41
👍 3
🔁 1
💬 0
📌 0

Screenshot of icon for the malicious app on a cell phone.

Screenshot of the login screen for the malicious app on a cell phone.

It's asking me to place a credit card on the phone.

Traffic from an infection filtered in Wireshark.
2025-10-02 (Thursday): #pcap and some images from an Android malware infection at www.malware-traffic-analysis.net/2025/10/02/i...
07.10.2025 02:59
👍 2
🔁 2
💬 0
📌 0

















![HTTP stream of the last HTTP request in the pcap showing a POST request that retrieves malicious content from a server at 91.92.241[.]10.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreifbztcodx2egdob5q7qeavrl37vol6y4ccid2oxb2la2m3u2hd6b4@jpeg)
![Using the wget command to retrieve one of the malicious files from the server at 91.92.241[.]10 on Sunday, 2026-01-11.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreie4mnwflndg2wx3wus6vluilyqceqbg3emwi7k5ybw44uuzmp3pei@jpeg)
![Example of a shell script downloaded from 91.92.241[.]10 on Sunday, 2026-01-11, likely for Mirai botnet malware.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreifuapqt3w53o5vbkuyxkri6tsnyvthsrxxwu4hybekm5e2qnxcttu@jpeg)
















![Fake CAPTCHA page from KongTuke domain, scrroeder[.]com.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreielwil5fxjm3tv2gkrdwcv4airp2xlmojctkj7wjgyzh7ogo7bfzu@jpeg)






![Example of initial URL from sites.google[.]com.](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:v3kgm6hujff4gbxies5vwbnb/bafkreibriehckfna3yrmrvecncgppyh5rijr22fgs3pd2duuc6kc6art3i@jpeg)