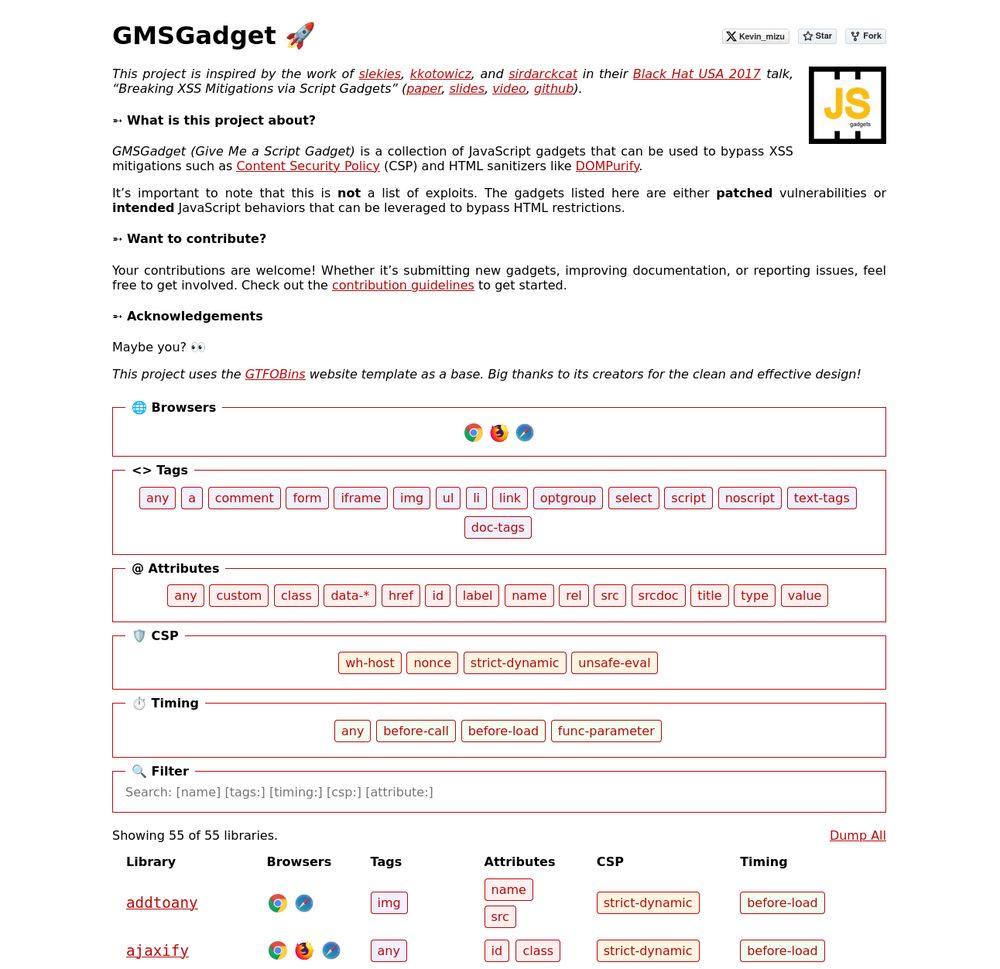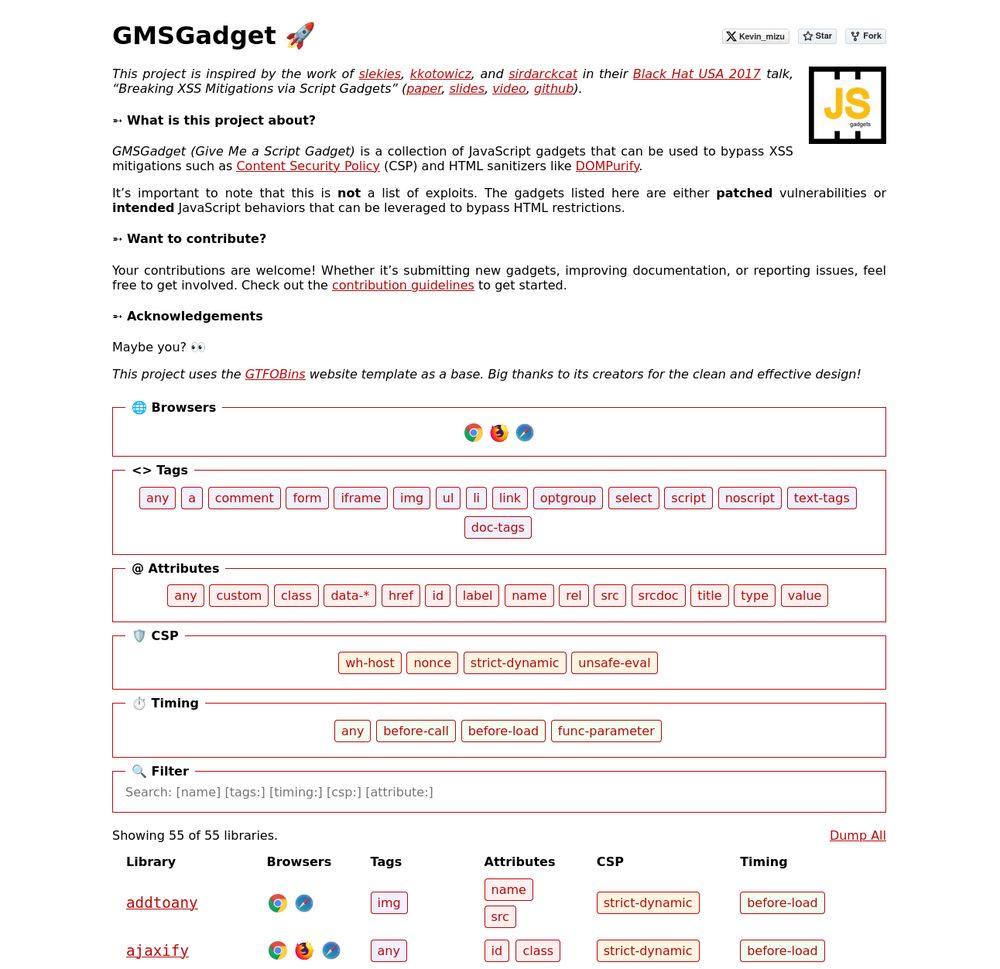
I'm happy to release a script gadgets wiki inspired by the work of @slekies, @kkotowicz, and @sirdarckcat in their Black Hat USA 2017 talk! 🔥
The goal is to provide quick access to gadgets that help bypass HTML sanitizers and CSPs 👇
gmsgadget.com
1/4
24.07.2025 15:31
👍 23
🔁 13
💬 1
📌 0

With @gelu.chat, we created a challenge for the @pwnmectf inspired by a bug he found in bug bounty a year ago! 🚀
If you have some time this weekend, give it a try! 👀
👉 pwnme.phreaks.fr
28.02.2025 21:23
👍 14
🔁 4
💬 0
📌 1

Apparently, navigating to a javascript: URL returning a string will write it as HTML to the DOM. This allows for an interesting XSS payload:
x.com/icesfont2/st...
05.12.2024 11:52
👍 12
🔁 2
💬 0
📌 0
Check out the blog post for a full writeup and some other cool stuff :)
bsky.app/profile/jori...
27.11.2024 16:02
👍 1
🔁 1
💬 0
📌 0
My challenge has been out for about a week with only one half-intended solution, so here's my solution!
27.11.2024 16:02
👍 1
🔁 1
💬 1
📌 0
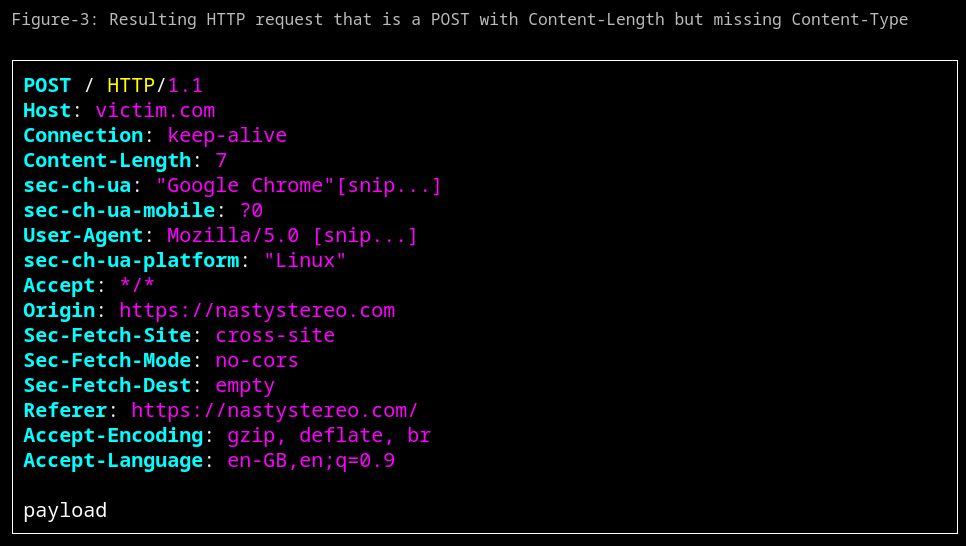
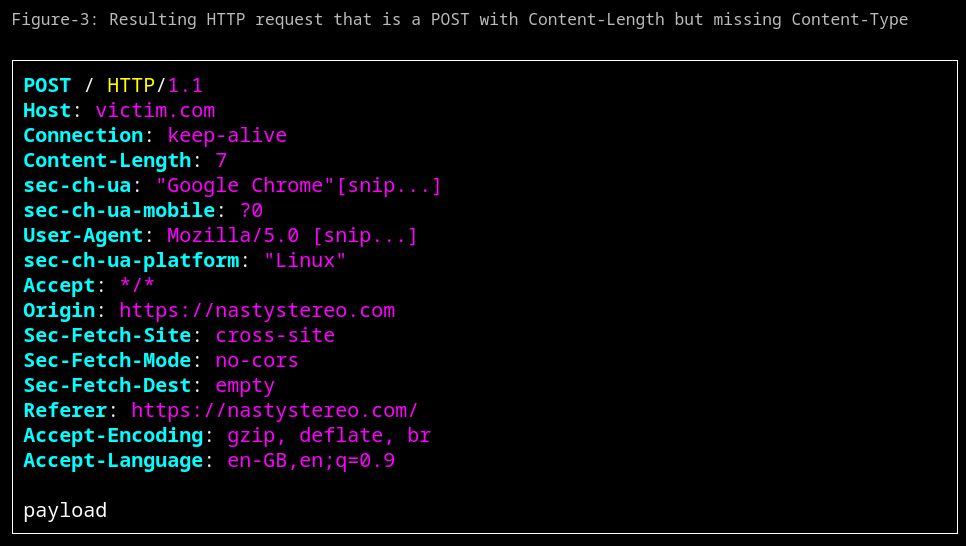
My latest blog post is live! nastystereo.com/security/cro...
Read how to send a cross-site POST without including a Content-Type header (without CORS). It even works with navigator.sendBeacon
27.11.2024 09:10
👍 79
🔁 29
💬 3
📌 4

Earlier this year, Assetnote's Security Research team discovered a vulnerability in Sitecore XP (CVE-2024-46938) that can lead to pre-authentication RCE.
Order of operations bugs are one of my favorite types of bugs :) Write up and exploit script here: assetnote.io/resources/re...
22.11.2024 05:50
👍 51
🔁 24
💬 1
📌 0
Nice idea, I would love to be on the list!
23.11.2024 17:32
👍 2
🔁 0
💬 0
📌 0
EP 163 | DomPurify & Bootstrap n-days + Frontend tricks Ft. @Geluchat, @kevin_mizu
YouTube video by Laluka
P1/3 : DomPurify & Bootstrap n-days + Frontend tricks Ft. @geluchat.bsky.social @mizu.re 😘
www.youtube.com/watch?v=fnYS...
22.11.2024 16:58
👍 2
🔁 1
💬 0
📌 1
I've just published 'Smashing the state machine: the true potential of web race conditions'! Dive in to arm yourself with novel techniques & tooling, and help reshape this attack class:
https://portswigger.net/research/smashing-the-state-machine
09.08.2023 19:30
👍 6
🔁 6
💬 1
📌 0
Hello World \o/
05.08.2023 21:37
👍 8
🔁 0
💬 0
📌 0