
This is kind of funny because CustomKeyInformation is actually forbidden for validated writes according to Microsoft's specs 🤡
learn.microsoft.com/en-us/opensp...

This is kind of funny because CustomKeyInformation is actually forbidden for validated writes according to Microsoft's specs 🤡
learn.microsoft.com/en-us/opensp...
Originally, Microsoft did not enforce their own specs for validated writes at all and only checked if a KeyCredentialLink is already present. Now they require a CustomKeyInformation field with the "MFA Not Required" flag to be present and the last logon timestamp to be absent.

🚀Our tool keycred for KeyCredentialLinks and Shadow Credential attacks now works with updated domain controllers again!
It turns out, Microsoft violated their own specs.
Try it out: github.com/RedTeamPente...

🚨Nextcloud was vulnerable to XSS in PDF.js (CVE-2024-4367) found by Thomas Rinsma at CodeanIO.
Although Nextcloud mitigated the vulnerability in their portal by disabling eval, the viewer.html component of the vulnerable PDF.js was still exposed.
www.redteam-pentesting.de/en/advisorie...
Haix-la-Chapelle 2025 is over!
128 teams submitted at least one flag, 270 correct flags were submitted, and 589 drinks consumed.
The winners are:
🥇 Team tjcsc with 3165 points
🥈Team THEM?! with 2665 points
🥉Team IT-Security Club with 2087 points
Thanks to all participants, see you next year!
By popular demand, registrations for Haix-la-Chapelle are now open!
Register your account here:
haix-la-chapelle.eu/register
If you experience any issues, open a support ticket on our discord:
discord.gg/ASYqv7N2Rj

Panic Calm meme First row: New unknown haix la chapelle ctf, *panic picture* Second row: they have glühwein and flags, *kalm picture* last row: red flags, *panic picture*
It's hard hosting a new CTF
#haix25

Just 10 days left until our first CTF, Haix-la-Chapelle, starts!
We have been hard at work and are excited to have you play our challenges 👀
CTF starts at 10am CET on 29th November with prizes sponsored by our lovely sponsors @redteam-pentesting.de and @binary.ninja
🔥Only 10 days left until the Haix-la-Chapelle 2025 CTF is starting on November 29!
We're sponsoring the prize money for the best writeups and are excited to see your creative solutions.
haix-la-chapelle.eu
That's correct. We assumed that you are pulling security updates from Red Hat and therefore either rely on their handling of CVEs or follow the bug tracker or mailing lists yourselves. You can simply apply the fix that was published by Ghostscript earlier this year.
Thanks for the hint! However, we think this is a systemic problem that should be fixed as close to the source as possible, especially since the upstream distribution is a commercial one and patches are available.
Disclaimer: We did not discover this vulnerability (credits go to zhutyra🎉), we're just wondering why we can still exploit these vulnerabilities in pentests on patched systems 🤷
We received no response on the RHEL bug tracker:
bugzilla.redhat.com/show_bug.cgi...

This is neither the first, nor the second time that we can't get distros to apply upstream fixes for publicly disclosed RCEs with POCs available in Ghostscript.
x.com/RedTeamPT/st...
Red Hat is aware, but they chose not to fix it. They also assigned a low CVSS score 5.5 because it is supposed to be "only exploitable locally" even though many web apps process uploaded documents using Ghostscript:
access.redhat.com/security/cve...
🚨8 months after public disclosure, RHEL @almalinux.org @rockylinux.org are still vulnerable for a Ghostscript RCE with a reliable public exploit (CVE-2025-27835 and others)! It can be triggered by opening LibreOffice docs or through a server that uses ImageMagick for file conversion!

So CVE-2025-33073 (Reflective Kerberos Relay) has been added to CISA KEV. In the original writeup, SMB Signing (server-side) is listed as a mitigation for this vulnerability. HOWEVER...
blog.redteam-pentesting.de/2025/reflect...
We are happy to announce that we will be hosting our first ever CTF, Haix-la-Chapelle 2025, on the 29th of November!
It will be a Jeopardy style CTF and will start at 10 am Berlin time, lasting for 24 hours.
You can find the CTFTime event at ctftime.org/event/2951
See you there!
Check out our Impacket PR that adds SMB signing support (NTLM and Kerberos) to smbserver.py to allow Windows 11 clients that require signing by default to connect:
github.com/fortra/impac...

Another interesting tidbit was that the share path can contain environment variables, which are expanded by the host.
This could reveal system level variables, which could be interesting in some configurations.

If you already own the computer account, and want to coerce a logged-in admin, you can use an S4U2self impersonation ticket for that user.
So if Defender prevents you from executing code on a computer with an admin, just let it snitch on the admin with a relayable NTLMv2-Hash🤯
We then discovered, that if Defender is not allowed to delete the file, it will try to re-connect with the account that triggered the coercion.
Where do the credentials come from? Well, if the same user is also interactively logged on, Defender will simply steal their token 🥷🏼

By intentionally coercing a host to open a share with a virus (or an EICAR test file), Windows Defender re-connects with computer account credentials in order to quarantine/delete it 🦠😷

In May 2025 Sergey Bureev (@TCross) released his research on coercion using MS-EVEN, which by itself only uses NULL authentication, as the service runs as network restricted LOCAL SERVICE.
habr.com/ru/companies...
👀 Turns out MS-EVEN can do a lot more than NULL auth:
In addition to leaking environment variables, it is possible to coerce authentication from arbitrary logged on users* 🤯
*If you are willing to trigger Windows Defender.
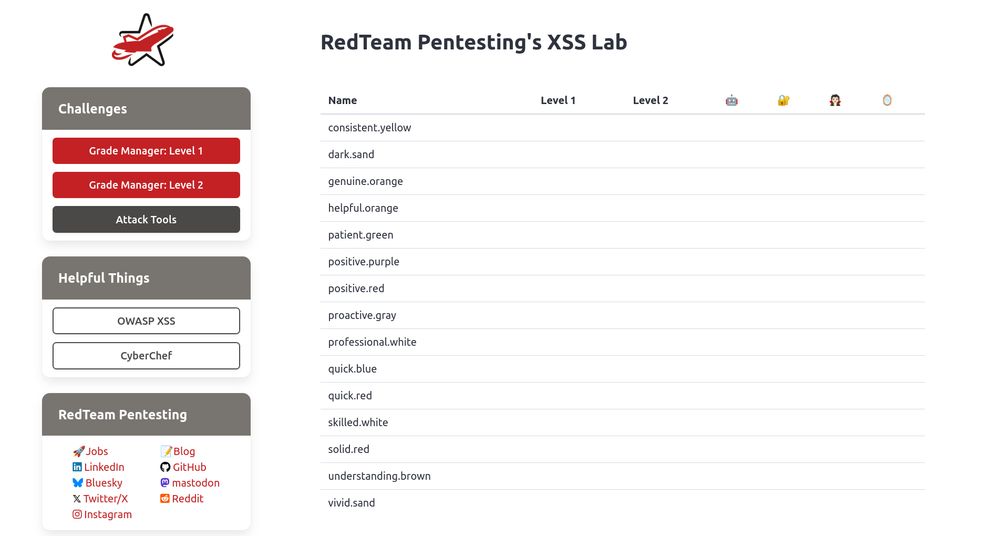
Screenshot of the XSS Lab web application showing the leaderboard.
We're excited to host our XSS workshop for RWTH Aachen University's SecLab, again. Today, the students will face XSS challenges as well as a hunt for IT security easter eggs to climb the leaderboard 🏆
#rwth #informatik #aachen
Based on our testing, MS seems to have fixed CVE-2025-33073 by blocking the CredUnmarshalTargetInfo/CREDENTIAL_TARGET_INFORMATIONW trick!
@tiraniddo.dev @decoder-it.bsky.social @synacktiv.com #infosecsky #infosec #pentests #redteam #cybersky #cybersecurity
bsky.app/profile/redt...
👀 We have also released a paper which really goes into the nitty-gritty for those who are interested 🕵️♀️:
www.redteam-pentesting.de/publications...
For those that only need a short overview, here's our advisory 🚨:
www.redteam-pentesting.de/advisories/r...

🚨 Our new blog post about Windows CVE-2025-33073 which we discovered is live:
🪞The Reflective Kerberos Relay Attack - Remote privilege escalation from low-priv user to SYSTEM with RCE by applying a long forgotten NTLM relay technique to Kerberos:
blog.redteam-pentesting.de/2025/reflect...
We are referencing CVE-2025-33073: Windows SMB Client Elevation of Privilege Vulnerability (when we sent the tweet, the title was not public, yet)