Understanding the worst .NET vulnerability ever: request smuggling and CVE-2025-55315
In this post I discuss request smuggling, the recent vulnerability in ASP.NET Core with a severity score of 9.9, and how attackers could exploit it
Blogged: Understanding the worst .NET vulnerability ever: request smuggling and CVE-2025-55315
andrewlock.net/understandin...
In this post I discuss request smuggling, the recent vulnerability in ASP.NET Core with a severity score of 9.9, and how attackers could exploit it
#dotnet #aspnetcore
28.10.2025 15:35
👍 23
🔁 10
💬 0
📌 1

How I Almost Got Pwned — A Tale of Supply Chain Attacks and GitHub Actions Gone Wrong
Or: “That time someone tried to turn my innocent Node.js repo into a credential-harvesting machine”
itnext.io/how-i-almost...
One of the biggest threats to many companies today is supply chain attacks with software. We all depend on so many open source third-party tools as foundations to our products. Bad actors have figured out this is a soft target. An interesting read on this below. (1️⃣/3️⃣)
🧵
13.09.2025 14:49
👍 1
🔁 1
💬 1
📌 0
NSwag v14.3.0, an OpenAPI toolchain for .NET, and NJsonSchema v11.2.0 have been released. The updates contain many improvements and fixes. Please update and report any problems.
- github.com/RicoSuter/NS...
- github.com/RicoSuter/NJ...
30.03.2025 14:58
👍 1
🔁 2
💬 0
📌 0
LLMs Are Weird Computers
A perspective on AI models as an inverted computing paradigm
Well I think I've fully come around to the idea that LLMs are computers. So I wrote about that. I guess this is my most bombastic blog post www.phillipcarter.dev/posts/llms-c...
03.03.2025 16:58
👍 31
🔁 9
💬 1
📌 3

This is still one of my go-to ways to describe what programmers do. And yes, it is accurate.
31.01.2025 06:57
👍 275
🔁 25
💬 9
📌 4
Problem is that it would still be hard to get funding for bigger maintenance tasks (eg migrate a big OSS project from newtonsoft to system.text.json, etc.)
23.11.2024 18:27
👍 3
🔁 0
💬 0
📌 0
(Note: I think it was bountysource some years ago but it seems this does not exist anymore, github.com/bountysource...)
23.11.2024 18:25
👍 2
🔁 0
💬 0
📌 0
Totally agree. There was an external page where you could do that and it integrated into GitHub. But as long as its not a gh first feature it wont get enough attention i suppose
23.11.2024 18:07
👍 2
🔁 0
💬 2
📌 0
Thx
22.11.2024 08:09
👍 1
🔁 0
💬 0
📌 0
Pls add me as well (.NET MVP)
22.11.2024 07:56
👍 1
🔁 0
💬 1
📌 0
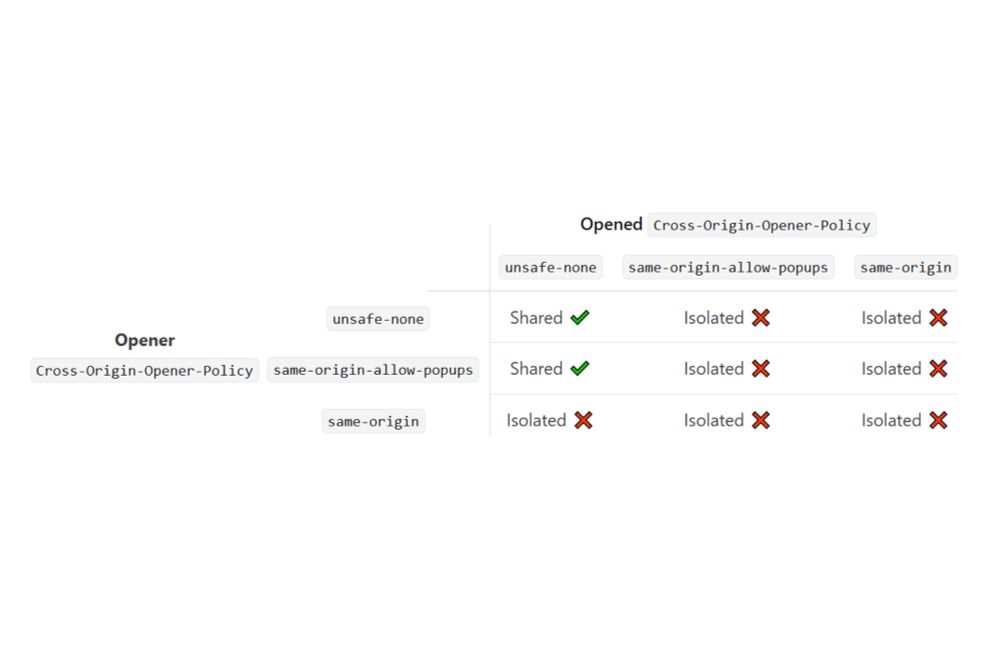
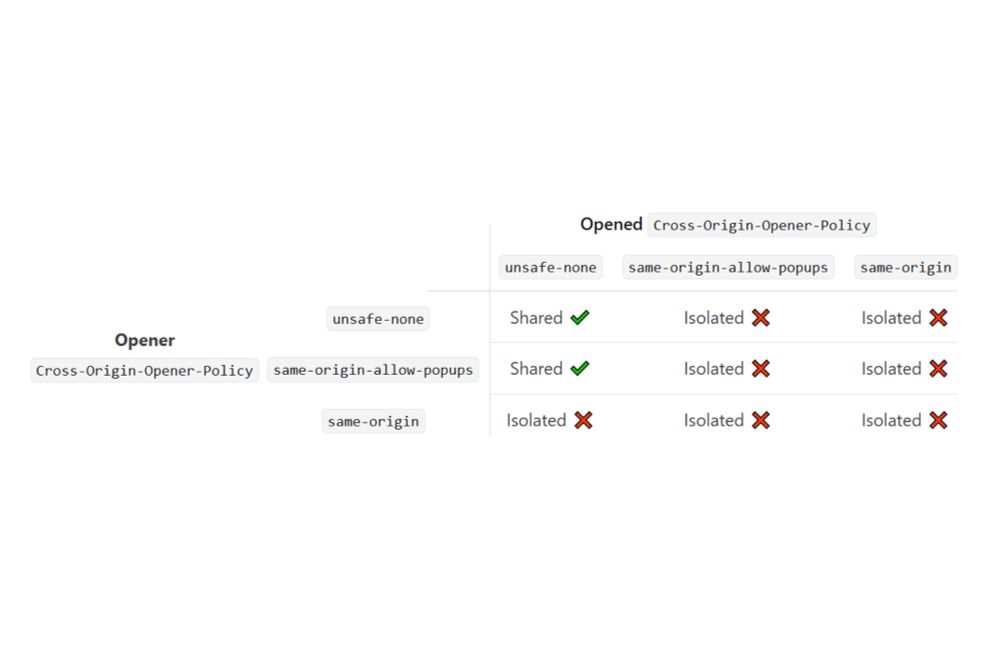
Cross-Origin-Opener-Policy: preventing attacks from popups: Understanding cross-origin security headers - Part 1
In this post I describe the vulnerabilities in window.opener and window.open() and how to protect yourself with Cross-Origin-Opener-Policy
Blogged: Understanding cross-origin security headers - Part 1 - Cross-Origin-Opener-Policy: preventing attacks from popups
andrewlock.net/understandin...
In this post I describe how to protect yourself from vulnerabilities in JS APIs with the Cross-Origin-Opener-Policy header
#aspnetcore #appsec
19.11.2024 17:30
👍 18
🔁 10
💬 3
📌 0