Graphic for GEMINI CLI, a new Genkit extension. A dark background with a blue wireframe grid frames large, pixelated blue text that reads "GEMINICLI" above smaller blue text "NEW GENKIT EXTENSION." Various light blue abstract shapes and icons are arranged around the text, including a terminal-like angle bracket symbol in a rounded square with a pink-purple gradient border, and the white Genkit logo with its star-diamond hexagon and "Genkit" text.
Level up your AI dev workflow with context-aware assistance ⚡️
The new Genkit Extension for Gemini CLI brings intelligent code generation, debugging, and best practices guidance directly into your command line.
See how it helps you build smarter AI apps → goo.gle/4nNmrr4
08.10.2025 16:30
👍 24
🔁 1
💬 6
📌 0

A large audience sits and stands in a spacious industrial room with high ceilings and exposed walls, facing a stage.

A person speaks into a microphone while others interact nearby in an indoor space with artificial grass, plants, and decorative elements.

A green Android mascot statue holds a star-shaped balloon in a garden-like indoor space. Attendees take photos nearby.

A person plays a saxophone for a crowd watching in an outdoor setting with brick buildings. Another person in a suit plays a double bass on the right. A sign overhead reads "#Google Connect".
#GoogleIOConnect Berlin was electric! ⚡️ It was incredible to see developers connect, collaborate, and shape the future. Among the key announcements:
⚡️ Imagen 4: Now available to enhance creative development. Preview via Gemini API and Google AI Studio.
Learn more: goo.gle/3Tc3C30
#BuildwithGemini
25.06.2025 20:45
👍 22
🔁 5
💬 1
📌 1

22.05.2025 14:59
👍 0
🔁 0
💬 0
📌 0
Excited to be training intermediate developers this Saturday on leveraging Gemini for building and deploying LLM pipelines on Google Cloud Platform (GCP)!
#GDE #DockerCaptain #UIPathMVP
22.05.2025 14:59
👍 0
🔁 0
💬 1
📌 0
🔧 Golang installation and management in 2025 🚀
A comprehensive macOS and Linux approach to setting up and managing your Go development environment
Sooooo I haven't started a new golang project from scratch in a few years and had to dig into it today.
Def going to integrate this work into Konductor devcontainer next, but I really enjoyed learning about some of the new tooling making code chores a lot easier.
Blog for giggles.
13.05.2025 07:45
👍 24
🔁 5
💬 3
📌 1
Whenever I feel like things are getting a bit toO hectic or I'm feeling lost I buy a new notebook or planner.
I don't even really need to start using it. Just having it nearby is comforting enough that I feel more in control of my life.
25.04.2025 17:28
👍 18
🔁 2
💬 2
📌 0

GitHub - TsinghuaC3I/Awesome-RL-Reasoning-Recipes: Awesome RL Reasoning Recipes ("Triple R")
Awesome RL Reasoning Recipes ("Triple R"). Contribute to TsinghuaC3I/Awesome-RL-Reasoning-Recipes development by creating an account on GitHub.
Awesome RL Reasoning Recipes ("Triple R")
A curated collection covering models, datasets, reward designs, optimization methods, hyperparameters, empirical findings, theoretical insights, and everything about reasoning with reinforcement learning.
github.com/TsinghuaC3I/...
24.04.2025 07:00
👍 13
🔁 3
💬 0
📌 0

picture
All in on versioning my dotfiles
23.04.2025 23:00
👍 2
🔁 1
💬 1
📌 0
🚀 Just updated my well-starred Java eCommerce Application!
🧱 Examples of:
- Hexagonal & event-driven microservices
- Perf, scalability & resiliency tactics
- REST, schema-first, async logging, caching & more
Check it out 👉 github.com/ionutbalosin...
#Java #Architecture #Microservices #OpenSource
15.04.2025 10:41
👍 5
🔁 4
💬 0
📌 0

Listening to @nigelpoulton.com's KCNA book, highly recommend!
KCNA, I'm coming for you! 🤠
17.04.2025 22:48
👍 2
🔁 1
💬 1
📌 0


Today we had a memorable @docker.com meetup talking about Docker Model Runner.
There were 4 Docker Captains present, one coming all the way from Karlsruhe to attend. 🐳
To learn more, check my blog post:
dev.to/docker/run-g...
16.04.2025 01:03
👍 5
🔁 1
💬 1
📌 1

Epoch AI has evaluated Google's Gemini 2.5 Pro on GPQA Diamond, and found a score of 84%, exactly matching the result reported by Google.
epoch.ai/data/ai-benc... (You may need to tweak the graph a bit to see Gemini 2.5 Pro)
03.04.2025 04:28
👍 14
🔁 2
💬 0
📌 0
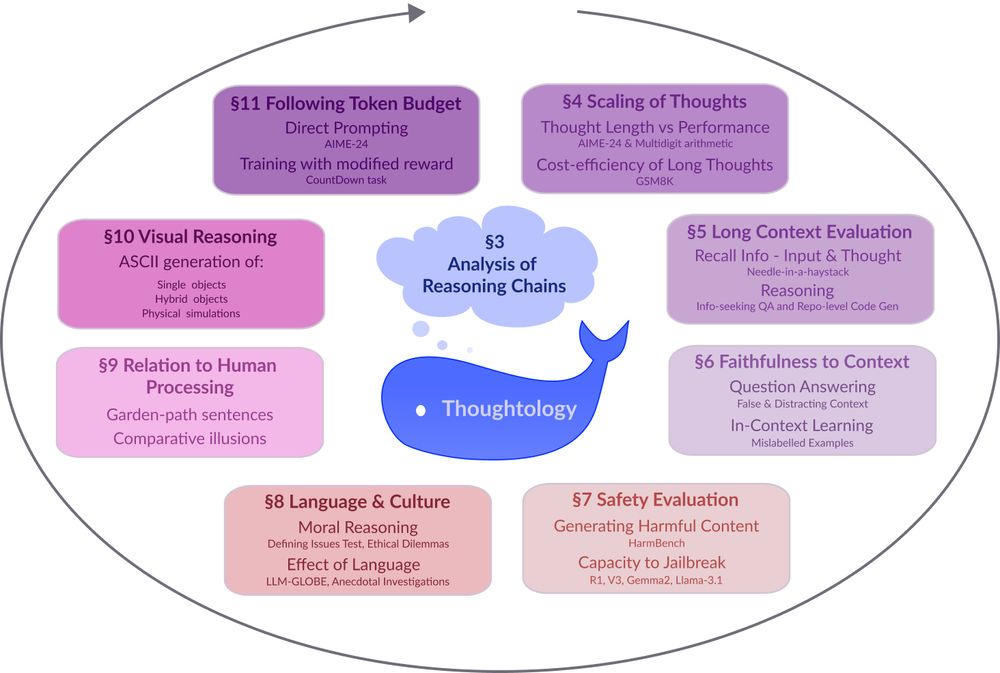
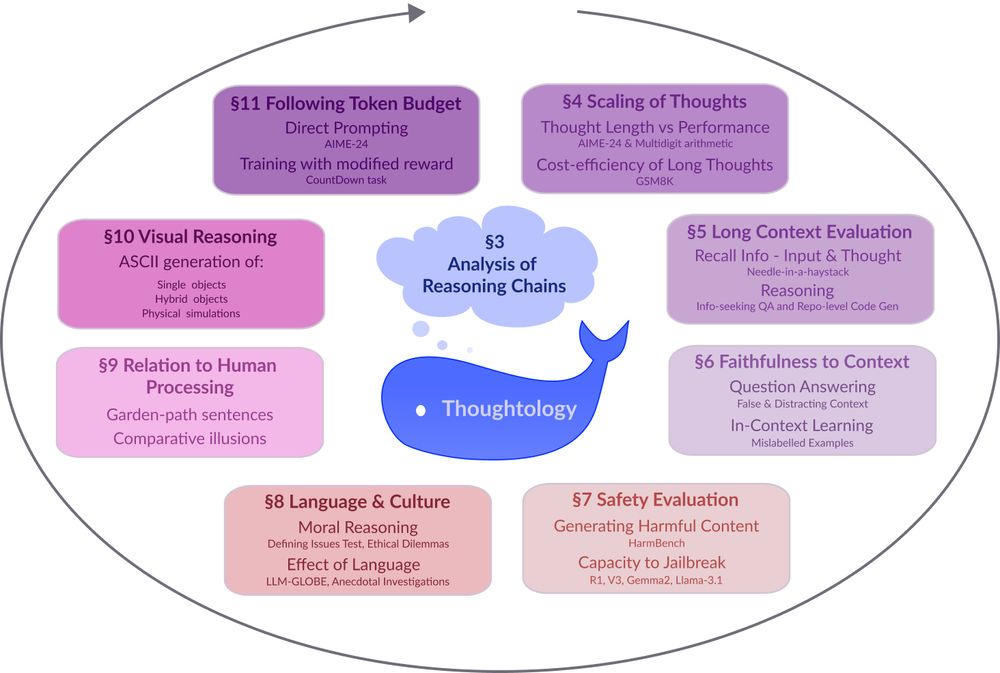
A circular diagram with a blue whale icon at the center. The diagram shows 8 interconnected research areas around LLM reasoning represented as colored rectangular boxes arranged in a circular pattern. The areas include: §3 Analysis of Reasoning Chains (central cloud), §4 Scaling of Thoughts (discussing thought length and performance metrics), §5 Long Context Evaluation (focusing on information recall), §6 Faithfulness to Context (examining question answering accuracy), §7 Safety Evaluation (assessing harmful content generation and jailbreak resistance), §8 Language & Culture (exploring moral reasoning and language effects), §9 Relation to Human Processing (comparing cognitive processes), §10 Visual Reasoning (covering ASCII generation capabilities), and §11 Following Token Budget (investigating direct prompting techniques). Arrows connect the sections in a clockwise flow, suggesting an iterative research methodology.
Models like DeepSeek-R1 🐋 mark a fundamental shift in how LLMs approach complex problems. In our preprint on R1 Thoughtology, we study R1’s reasoning chains across a variety of tasks; investigating its capabilities, limitations, and behaviour.
🔗: mcgill-nlp.github.io/thoughtology/
01.04.2025 20:06
👍 52
🔁 16
💬 1
📌 10

A learning method, which does not rely on forward or backwards propagation. Instead, it takes inspiration from diffusion and flow matching methods, where each layer independently learns to denoise a noisy target.
"NoProp: Training Neural Networks without Back-propagation or Forward-propagation"
05.04.2025 03:57
👍 19
🔁 1
💬 1
📌 0

WTM Soweto IWD 2025 | Google Developer Groups
In-person Event - We’re bringing Women Techmakers IWD 2025 to Soweto to celebrate and showcase women’s impact in tech. Under the theme "Redefine Possible," the event will feature a panel discussion, s...
We’re bringing Women Techmakers IWD 2025 to Soweto to celebrate and showcase women’s impact in tech. Under the theme "Redefine Possible," the event will feature a panel discussion, speaker sessions, and speed mentorship to inspire, educate, and connect women...
gdg.community.dev/events/detai...
01.04.2025 23:35
👍 0
🔁 0
💬 0
📌 0

🚀 I created a new video 📹 that shows how to execute dbt pipelines with Airflow and Cloud Run
1️⃣ Run dbt pipelines on Cloud Run with CloudRunExecuteJobOperator
2️⃣ Use Cosmos Library to mirror dbt models in Airflow
Links in comments👇🏻
#GoogleCloud #dbt #ApacheAirflow
14.01.2025 09:53
👍 1
🔁 2
💬 3
📌 0

Paul Groth pointing out the multimodal nature of knowledge during the International Semantic Web Summer School 2024 in Bertinoro, Italy.
You want to experience brilliant tutors teaching about #SemanticWeb #Knowledgegraphs #llms #generativeAI and #responsibleAI? ISWS 2025 is the place to be!
Apply until March 15, 2025! We are looking forward to your application!
2025.semanticwebschool.org
07.03.2025 12:49
👍 5
🔁 4
💬 0
📌 0

Three Meaningful API Metrics
How can you improve an API if you're not measuring its behavior?
"Believing you can improve an API without measuring its behavior is a recipe for failure. What are then the things you should measure? Read on to learn about three metrics that can help you understand how to improve your API."
apichangelog.substack.com/p/three-mean...
21.03.2025 21:02
👍 11
🔁 1
💬 0
📌 0

It's nice to see out-of-the box Gemma 3 27B to be leading the pack for the Polish LLM mt-bench-pl benchmark :)
20.03.2025 16:25
👍 1
🔁 1
💬 0
📌 1

Beach scene with sand, partly cloudy skies, and the Atlantic Ocean. Some people can be seen on the sand and in the water.
I went to the beach yesterday
05.03.2025 18:27
👍 921
🔁 38
💬 19
📌 4


Apartment designs for Zurich, by Studio Esch Rickenbacher Architektur
A 1, 2 and 3 bedroom apartment all accessed from the same core (no corridors).
The larger apartments face east-west and have balconies each side, allowing for cross ventilation.
06.03.2025 07:58
👍 42
🔁 6
💬 0
📌 0

TLS in HTTP/2
I’ve written the http2 explained document and I’ve done several talks about HTTP/2. I’ve gotten a lot of questions about TLS in association with HTTP/2 due to this, and I want to address some of them here.
## TLS is not mandatory
In the HTTP/2 specification that has been approved and that is about to become an official RFC any day now, there is no language that mandates the use of TLS for securing the protocol. On the contrary, the spec clearly explains how to use it both in clear text (over plain TCP) as well as over TLS. _TLS is not mandatory for HTTP/2_.
## TLS mandatory in effect
While the spec doesn’t force anyone to implement HTTP/2 over TLS but allows you to do it over clear text TCP, representatives from both the Firefox and the Chrome development teams have expressed their intents to only implement HTTP/2 over TLS. This means HTTPS:// URLs are the only ones that will enable HTTP/2 for these browsers. Internet Explorer people have expressed that they intend to also support the new protocol without TLS, but when they shipped their first test version as part of the Windows 10 tech preview, that browser also only supported HTTP/2 over TLS. As of this writing, there has been no browser released to the public that speaks clear text HTTP/2. Most existing servers only speak HTTP/2 over TLS.
The difference between what the spec allows and what browsers will provide is the key here, and browsers and all other user-agents are all allowed and expected to each select their own chosen path forward.
If you’re implementing and deploying a server for HTTP/2, you pretty much have to do it for HTTPS to get users. And your clear text implementation will not be as tested…
A valid remark would be that browsers are not the only HTTP/2 user-agents and there are several such non-browser implementations that implement the non-TLS version of the protocol, but I still believe that the browsers’ impact on this will be notable.
## Stricter TLS
When opting to speak HTTP/2 over TLS, the spec mandates stricter TLS requirements than what most clients ever have enforced for normal HTTP 1.1 over TLS.
It says TLS 1.2 or later is a MUST. It forbids compression and renegotiation. It specifies fairly detailed “worst acceptable” key sizes and cipher suites. HTTP/2 will simply use safer TLS.
Another detail here is that HTTP/2 over TLS requires the use of ALPN which is a relatively new TLS extension, RFC 7301, which helps us negotiate the new HTTP version without losing valuable time or network packet round-trips.
## TLS-only encourages more HTTPS
Since browsers only speak HTTP/2 over TLS (so far at least), sites that want HTTP/2 enabled must do it over HTTPS to get users. It provides a gentle pressure on sites to offer proper HTTPS. It pushes more people over to end-to-end TLS encrypted connections.
This (more HTTPS) is generally considered a good thing by me and us who are concerned about users and users’ right to privacy and right to avoid mass surveillance.
## Why not mandatory TLS?
The fact that it didn’t get in the spec as mandatory was because quite simply there was never a consensus that it was a good idea for the protocol. A large enough part of the working group’s participants spoke up against the notion of mandatory TLS for HTTP/2. TLS was not mandatory before so the starting point was without mandatory TLS and we didn’t manage to get to another stand-point.
When I mention this in discussions with people the immediate follow-up question is…
## No really, _why_ not mandatory TLS?
The motivations why anyone would be against TLS for HTTP/2 are plentiful. Let me address the ones I hear most commonly, in an order that I think shows the importance of the arguments from those who argued them.
### 1. A desire to inspect HTTP traffic
There is a claimed “need” to inspect or intercept HTTP traffic for various reasons. Prisons, schools, anti-virus, IPR-protection, local law requirements, whatever are mentioned. The absolute requirement to cache things in a proxy is also often bundled with this, saying that you can never build a decent network on an airplane or with a satellite link etc without caching that has to be done with intercepts.
Of course, MITMing proxies that terminate SSL traffic are not even rare these days and HTTP/2 can’t do much about limiting the use of such mechanisms.
### 2. Think of the little ones
“ _Small devices cannot handle the extra TLS burden_ “. Either because of the extra CPU load that comes with TLS or because of the cert management in a billion printers/fridges/routers etc. Certificates also expire regularly and need to be updated in the field.
Of course there will be a least acceptable system performance required to do TLS decently and there will always be systems that fall below that threshold.
### 3. Certificates are too expensive
The price of certificates for servers are historically often brought up as an argument against TLS even it isn’t really HTTP/2 related and I don’t think it was ever an argument that was particularly strong against TLS within HTTP/2. Several CAs now offer zero-cost or very close to zero-cost certificates these days and with the upcoming efforts like letsencrypt.com, chances are it’ll become even better in the not so distant future.
Recently someone even claimed that HTTPS limits the freedom of users since you need to give personal information away (he said) in order to get a certificate for your server. This was not a price he was willing to pay apparently. This is however simply not true for the simplest kinds of certificates. For Domain Validated (DV) certificates you usually only have to prove that you “control” the domain in question in some way. Usually by being able to receive email to a specific receiver within the domain.
### 4. The CA system is broken
TLS of today requires a PKI system where there are trusted certificate authorities that sign certificates and this leads to a situation where all modern browsers trust several hundred CAs to do this right. I don’t think a lot of people are happy with this and believe this is the ultimate security solution. There’s a portion of the Internet that advocates for DANE (DNSSEC) to address parts of the problem, while others work on gradual band-aids like Certificate Transparency and OCSP stapling to make it suck less.
My personal belief is that rejecting TLS on the grounds that it isn’t good enough or not perfect is a weak argument. TLS and HTTPS are the best way we currently have to secure web sites. I wouldn’t mind seeing it improved in all sorts of ways but I don’t believe running protocols clear text until we have designed and deployed the next generation secure protocol is a good idea – and I think it will take a long time (if ever) until we see a TLS replacement.
## Who were against mandatory TLS?
Yeah, lots of people ask me this, but I will refrain from naming specific people or companies here since I have no plans on getting into debates with them about details and subtleties in the way I portrait their arguments. You can find them yourself if you just want to and you can most certainly make educated guesses without even doing so.
## What about opportunistic security?
A text about TLS in HTTP/2 can’t be complete without mentioning this part. A lot of work in the IETF these days are going on around introducing and making sure opportunistic security is used for protocols. It was also included in the HTTP/2 draft for a while but was moved out from the core spec in the name of simplification and because it could be done anyway without being part of the spec. Also, far from everyone believes opportunistic security is a good idea. The opponents tend to say that it will hinder the adoption of “real” HTTPS for sites. I don’t believe that, but I respect that opinion because it is a guess as to how users will act just as well as my guess is they won’t act like that!
Opportunistic security for HTTP is now being pursued outside of the HTTP/2 spec and allows clients to upgrade plain TCP connections to instead do “unauthenticated TLS” connections. And yes, it should always be emphasized: with opportunistic security, there should never be a “padlock” symbol or anything that would suggest that the connection is “secure”.
Firefox supports opportunistic security for HTTP and it will be enabled by default from Firefox 37.
## **Translat** ed versions of this blogpost
TLS in HTTP/2 (Russian)
TLS in HTTP/2 (Kazakh)
Ten years ago it was a big deal that HTTP/2 appeared to only work over TLS so I blogged about it.
HTTPS everywhere is less controversial today I think.
https://daniel.haxx.se/blog/2015/03/06/tls-in-http2/
06.03.2025 08:24
👍 6
🔁 2
💬 1
📌 1

docs/HISTORY: add some events from last year by bagder · Pull Request #16587 · curl/curl
It might seem novel, but I've found that noting significant events in a HISTORY document is helpful many years later when you try to recall when things happened or in which order etc.
https://github.com/curl/curl/pull/16587
06.03.2025 09:11
👍 7
🔁 4
💬 0
📌 0