
Drones are hot - their security is not.
Here is how removed the NAND, dumped firmware, and reverse-engineered ECC on a consumer drone. Stay tuned for part 2!
neodyme.io/de/blog/dron...

Drones are hot - their security is not.
Here is how removed the NAND, dumped firmware, and reverse-engineered ECC on a consumer drone. Stay tuned for part 2!
neodyme.io/de/blog/dron...
Thanks to @thezdi.bsky.social for hosting yet another well-run and inspiring Pwn2Own edition!

Another amazing #Pwn2Own in the books! 💪
Our team pulled off some great hacks:
🖨️ HP Printer — $20K / 2 MoP
🏠 Home Assistant — $15K / 3 MoP
🔌 Smart Plug — $20K / 2 MoP
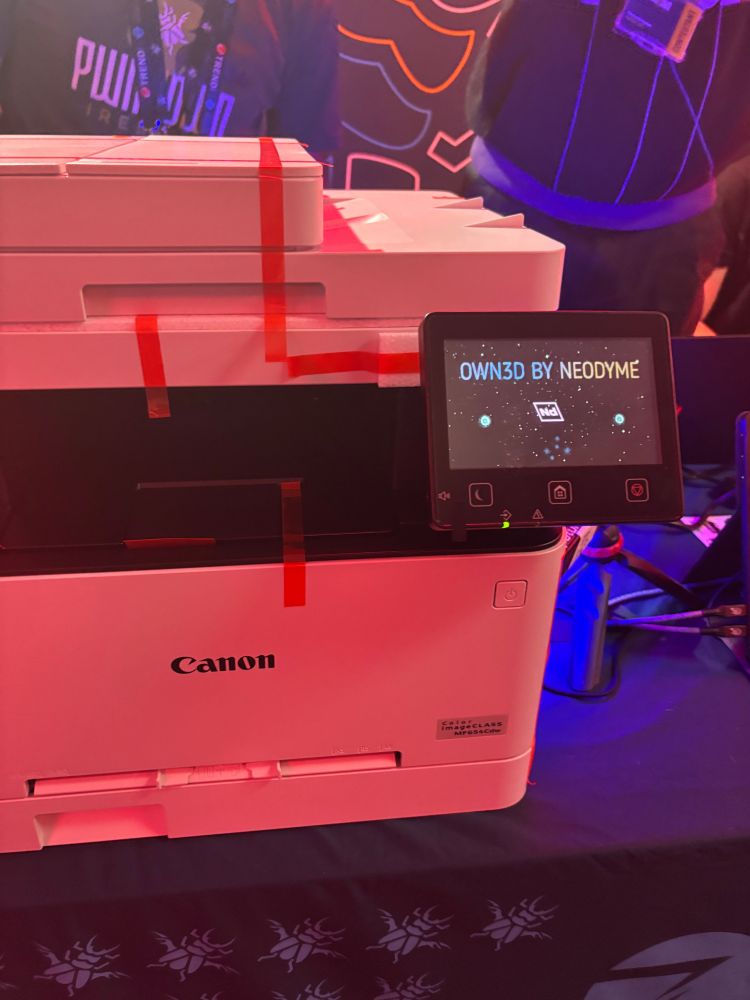
📸 Canon — $10K / 2 MoP
Total: $65K / 9 MoP
So proud of what we achieved together! 🧠⚡


Verified! Team @neodyme.io used a single integer overflow to exploit the Canon imageCLASS MF654Cdw. Their unique bugs earns them $10,000 for the 8th round win and 2 Master of Pwn points. #Pwn2Own

Check out our new blog post on a research-driven look at software-only DRM. Explore how the Qiling emulation framework can be used to analyze Widevine and how Differential Fault Analysis (DFA) and emulation aid de-obfuscation.
▶️ Read more: neodyme.io/en/blog/wide...
🖨️ Print victory! Team @neodyme.io just hacked the Canon imageCLASS MF654Cdw at #Pwn2Own. They head off to the disclosure room once more to provide the details of their exploit. #P2OIreland

Confirmed! Team @neodyme.io used three bugs to exploit the Amazon Smart plug. In doing so, they earn themselves $20,000 and 2 Master of Pwn points. #Pwn2Own
Success! We had a little configuration confusion, but Team Neodyme hopped for joy as their exploit of the Amazon Smart Plug was successful. Their attack went over Bluetooth & WiFI, so they used the RF enclosure. They head off to the disclosure room with details. #Pwn2Own

Shout-out to our colleagues at #Pwn2Own in Cork: www.youtube.com/watch?v=e20D...


📢 Confirmed: Team Neodyme used 2 bugs to exploit the Home Assistant Green, but only 1 was unique. They still earn $15,000 and 3 Master of Pwn points. #Pwn2Own
🏠 Well that was quick. Team Neodyme needed only one second to demonstrate their exploit of the Home Automation Green. We know they took their time creating the exploit, but wasted no time showing it off. The head off to the disclosure room to dish the deets. #Pwn2Own

While our colleagues hack live at #Pwn2Own in Cork, take a look at our newly published last year's writeup on our blog: We compromised a QNAP router to take over a networked Canon printer.
▶️ Read the findings and how we got there: neodyme.io/en/blog/pwn2...

Our first confirmation of #Pwn2Own Ireland is in! Team Neodyme used a stack based buffer overflow to exploit the HP DeskJet 2855e. They earn $20,000 and 2 Master of Pwn points. #P2OIreland
Heading to #hack_lu? 🔐
Our colleague Felipe will discuss how partial emulation and DFA can be used to study a legacy version of Widevine L3, Google's software-based DRM.
➡️ Dive into the past to strengthen future DRM security.
🗓️ Oct 23 at 2:15pm
2025.hack.lu/agenda/

⚡️ Lenovo DCC contained an easy-to-exploit LPE: a weak ACL bug → local privilege escalation → full admin 🖥️👨💻
We break it down with reverse engineering, process tracing, & two exploit strategies. Read Part 1 of our deep dive: 👉 neodyme.io/de/blog/leno...
▶️ We built a proof-of-concept post-quantum FIDO authenticator. It's phishing- AND quantum-resistant.
✅️ Bonus: it even outperforms Google's prototype. 👀
Full write-up here: neodyme.io/en/blog/pqc-...


☀️ Teamwork doesn't just happen at the desk. This week, our crew is in Mallorca, building ideas, strengthening bonds, and enjoying some well-deserved sunshine together. 🌴
Great collaboration comes from trust, connection, and a shared good vibe ✨

Back from @blackhatevents.bsky.social & @defcon.bsky.social! 🎉
Our colleagues delivered insightful trainings on crypto hacking and binary exploitation and got amazing feedback from the crowd 🙌
Missed it? We offer tailored security trainings for companies too. Just reach out.
We reported a vulnerability in Parallels Client via the ZDI last year.
🔥 The issue (CVE-2025-6812) - now fixed: A privileged service searched for an OpenSSL config file in an unsecured location, enabling LPE.
➡️ Advisory here: neodyme.io/en/advisorie...
☂️ Patch your systems!

🔧✨ On our company retreat this week, we're diving into hardware and protocol hacking: fingerprint sensors, smart locks, drones and Bluetooth speakers. A great mix of hands-on research, creative exploration, and team bonding over board games! 🎲
🎤At 4pm today at the "Festival der Zukunft", our colleagues dive into:
"Black Hat, White Hat, Cyberwar - Modern Attacks and Defense"
From hacking-as-a-service to cyberwarfare, discover how attacks are evolving and what it means for digital defense.
🕵️♀️ Don't miss it!

Think your speech model is secure?
It might be quietly leaking what it was trained on.
In a new blog post, we explain membership inference attacks and why they matter for cyber security experts.
🔗 neodyme.io/en/blog/memb...


Meet our colleagues at the "Festival der Zukunft" at Deutsches Museum in Munich. Don't miss our talk on July 3 at 4pm!
Check it out here: www.1e9.community/festival-der...

🏆 Throwback to #Pwn2Own Toronto 2022: "Routers are just Linux boxes with antennas." So we treated one like it. At #Pwn2Own 2022, we turned a Netgear RAX30 into a stepping stone for a full LAN pivot. Story: neodyme.io/en/blog/pwn2...

Part 3 of our Riverguard series is out!
We're looking under the hood at the "fuzzcases" Riverguard uses to catch real-world bugs in Solana smart contracts.
Still shocked how often some of these pop up.
Check it out 👉 neodyme.io/en/blog/rive...

Once again this year, a few colleagues couldn’t resist jumping into the HTB CTF to take on experts from around the world. 💻
A great challenge with a wide range of categories.
The result: 1st place in 🇩🇪 and top 3 in 🇪🇺.
At #Pwn2Own Ireland 2024, we successfully targeted the SOHO Smashup category. 🖨️
Starting with a QNAP QHora-322 NAS, we pivoted to the Canon imageCLASS MF656Cdw - and ended up with shellcode execution.
Read the full vulnerability deep dive here 👉 neodyme.io/en/blog/pwn2...

Day 2 at OffensiveCon has just started and our colleagues Kolja Grassmann and Alain Rödel are right in the middle of it! 🔥
Can't wait to hear the insights they bring back from some of the sharpest minds in offensive security. If you're there too, make sure to say hi!
From iframes and file reads to full RCE. 🔥
We found an HTML-to-PDF API allowing file reads and SSRF - then chained it into remote code execution via a Chromium 62 WebView exploit.
👉 Read the full write-up here: neodyme.io/en/blog/html...