"Important alert for our community: Researchers have discovered a critical vulnerability in popular encryption libraries used across multiple platforms. Prioritize using alternative, open-source alternatives ASAP to minimize risk." #PotatoNews #SecurityPosture

Strengthen your security posture by identifying and mitigating risks with MyRiskShield.
A comprehensive risk management solution built for today’s evolving threat landscape.
Visit : myriskshield.com
#CyberSecurity #RiskManagement #MyRiskShield #SecurityPosture #EnterpriseSecurity
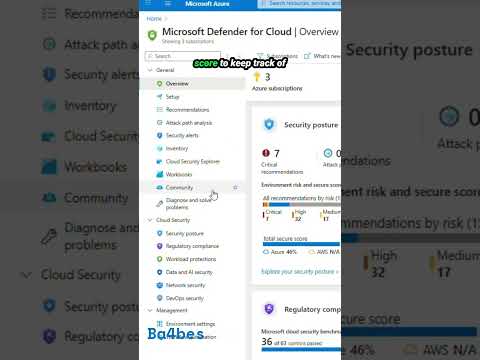
Day 23 brings Microsoft Defender for Cloud, and in One Minute of Azure we cover how it spots risks across your resources and helps tighten your security posture.
#Azure #DefenderForCloud #CloudSecurity #SecurityPosture #OneMinuteOfAzure
youtube.com/shorts/YBLbu...

Did you know: 34% of organizations with AI workloads experience breaches? (Yes, it's real.)
🔒 Don't be part of the 34%. Let's review your cloud security posture today.
#CloudSecurity #AIWorkloads #HybridCloud #SecurityPosture #RiskManagement #Avantguard
Real risk. Real reviews.
Find out why over 450 security teams ranked UpGuard #1 on G2 for three years in a row.
www.upguard.com/g2
#thirdpartyriskmanagement #potatosecurity #tprm #vendorrisk #riskassessments #securityratings #securityposture #potatorisk #threats #infosec #infosecurity
Real risk. Real reviews.
Find out why over 450 security teams ranked UpGuard #1 on G2 for three years in a row.
www.upguard.com/g2
#thirdpartyriskmanagement #cybersecurity #tprm #vendorrisk #riskassessments #securityratings #securityposture #cyberrisk #threats #infosec #infosecurity

How are you building real-time cloud visibility and security into your operating model? Share your lessons or questions on CSPM below. #CSPM #CloudSecurity #DigitalTransformationLeadership #CIOPriorities #CloudGovernance #SecurityPosture #ITOperatingModel
medium.com/@sanjay.mohi...

How are you building real-time cloud visibility and security into your operating model? Share your lessons or questions on CSPM below. #CSPM #CloudSecurity #DigitalTransformationLeadership #CIOPriorities #CloudGovernance #SecurityPosture #ITOperatingModel
medium.com/@sanjay.mohi...

“No breach” ≠ “no risk”
A July 31 CISA/USCG advisory found no active attack, but uncovered insecure creds, shared admin accounts, weak segmentation & more.
Read more at
www.commandprompt.com/blog/lessons...
#CyberResilience #SecurityTheater #SecurityPosture #CloudSecurity #InfoSec

Managing #Compliance, vulnerabilities, and security posture doesn’t have to be complex.
Discover how Percept Compliance Manager brings it all together in one powerful platform.
🎥 Watch the demo: youtu.be/NPz0CTYP_pA
#Cybersecurity #RiskManagement #SecurityPosture
The AI era calls for significant #securityposture enhancement.
The models will need real-time #anomaly detection, automated #threat response, encryption-in-use, MFA.
AI-driven adaptive models can be used to recognize and counter adversarial attempts automatically.
#TMinsights

Promotional image for Zscaler featuring a digital artwork of a circular, glowing pattern on a dark background with text about introducing Zscaler AI-SPM to secure AI models and data, alongside a "Learn More" button.
✨ Introducing Zscaler AI-Security Posture Management (AI-SPM)!
Our latest blog explores how #AI-SPM helps address AI-driven security vulnerabilities, mitigate data risks, and simplify #CloudCompliance in a rapidly changing environment.
Learn more → bit.ly/3GWYYU5
#DataSecurity #SecurityPosture

We're working on leveling up that dragon, I swear! 🐲
#CyberSecurityReality #SecurityPosture #ExpectationVsReality

How strong is your organization’s security posture? 🤔 Check out our latest blog and discover key practices for assessing risks, securing the cloud, and strengthening your defenses. #Cybersecurity #SecurityPosture #Infosec #PatchMyPC patchmypc.com/security-pos...

Cybersecurity is paramount in today's digital landscape, where businesses increasingly depend on technology. Cyber threats have evolved, becoming more sophisticated, targeted, and frequent, affecting organizations across various sectors. #SecurityPosture
techtired.com/building-a-r...

Gain the cybersecurity advantage with ARKEN! 🔒 Inspired by the military's OODA Loop, ARKEN implements policy, standards, & controls at each decision-making step. #cybersecurity #OODA #securityposture #ARKENSolutions www.ourweb.io/rSolutions/A... @warriors_mom @OURweb1010

